mbed OS 5.2 now released!
I’m pleased to announce that mbed OS 5.2 is now released and available for developers!
This release builds on all the significant enhancements that were released in mbed OS 5.1, adding the following headline features:
Support for integrated Wi-Fi SoCs and modules
Wireless modules are a great way to cope with the complexity of integrating radios in to a design and are commonly used in design runs of 10-100k units, possibly even higher. Even the highest volume smartphones often use modules to benefit from this separation of concerns.
To help developers take advantage of these modules, we’ve been working to build flexible integration support for different SoC, Module and Network Processor Wi-Fi architectures into mbed OS. In many cases, this means mbed OS can now be ported to run on modules themselves, opening them up as development targets and meaning they may be the only processing unit on your BOM.
The first integrated module support has already been added by u-blox, the ODIN-W2 module and development platform.
Over the next few weeks we’ll be able to share some of the other platforms our partners have been working on as the support goes live. And if you are a Wi-Fi module manufacturer and would like to get your parts supported, please contact us at partnership@mbed.com
Hardware Entropy, security and the importance of being random
We’re committed to building security in to our platform that all developers can rely on and take advantage of the security features of hardware platforms. Strong entropy is a vital cornerstone of strong security, and therefore we’re making it an important ingredient in the mbed OS platform and the target parts where mbed OS runs.
For more on the theory and considerations around entropy and its relation to security, take a look at this video:
We've been working to implement hardware entropy support in to the core of mbed OS and make it easy for partners to add support for their target platforms by extending the mbed HAL. Partners have been working on introducing the first platform support, and we’ll soon add filters to the mbed developer website so it is easy to find platforms that have achieved this level of security.
Memory footprint profiling
The size of the memory footprint of an application can have a direct impact on the BOM for a device and even the range of hardware that is applicable for designing a device.
To help both end developers and the teams building mbed OS itself, we’ve implemented a number of tools and libraries that hook in to the mbed OS core to allow memory footprint tracking and analysis. This includes runtime tools for tracking of dynamic memory utilisation and heap information and stack checking to trap stack over-runs.
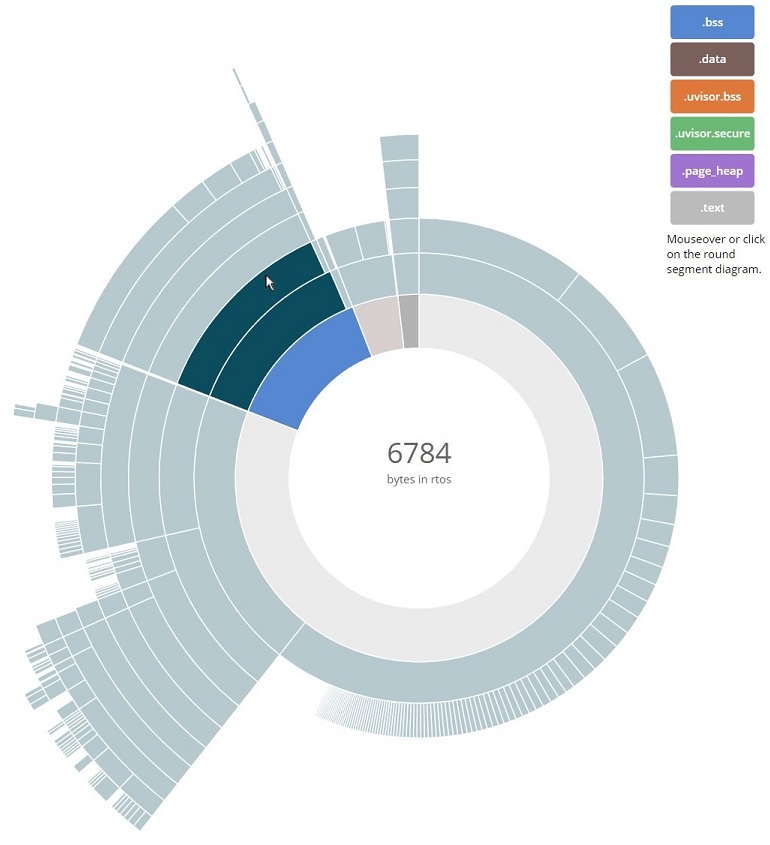
We’ve already started using this internally to analyze and optimize libraries and it is going in to our test framework to allow our CI to pick up memory footprint regressions as code is developed. We are also aiming to release a few useful tools to interpret the raw data, like the explorer you can see above (currently just an internal prototype). Static memory analysis is built into mbed CLI and for more information on the dynamic memory hooks, you can take a look at the runtime statistics documentation.
What else?
There are lots of other enhancement including an events library for use within RTOS threads, an implementation of Cipher-based Message Authentication Code (CMAC) as used in our mbed OS Thread stack and an improved export mechanism supporting project generation for different toolchains and IDEs. For more information, you can read our full release note for mbed OS 5.2
Thanks to our partners’ hard work, mbed OS 5.2 has been extended to support over 60 targets, and more will be added in our bi-weekly releases.
We hope you like the new features; if you have any feedback, questions or issues on this release, please don't hesitate to get in contact.
You need to log in to post a discussion