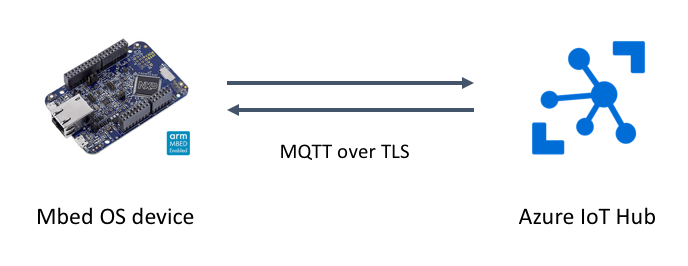
Azure IoT Hub from Mbed OS device
Overview
In this page, we'll try to connect to Microsoft Azure IoT Hub from an Mbed OS device using MQTT over TLS. Authentication is done by X.509 certificates.
Prerequisites
- Microsoft Azure account and IoT Hub - If you don't have, see here and create an IoT Hub.
- IoTHub Explorer (guidance appears in a following section)
- Mbed OS target board
- Network connectivity
- Node.js
- git
- Mbed account
Test Environment
This page's contents were tested on this environment:
- macOS HighSierra 10.13.6 (17G65)
- Mbed Enabled board - FRDM-K64F
- Ethernet (on the board)
- git version 2.15.1
- Node.js: node v8.9.4
Prepare Azure IoT Hub
Here, we create certificates and set up IoT Hub to connect your device. Suppose that you have already created an IoT Hub.
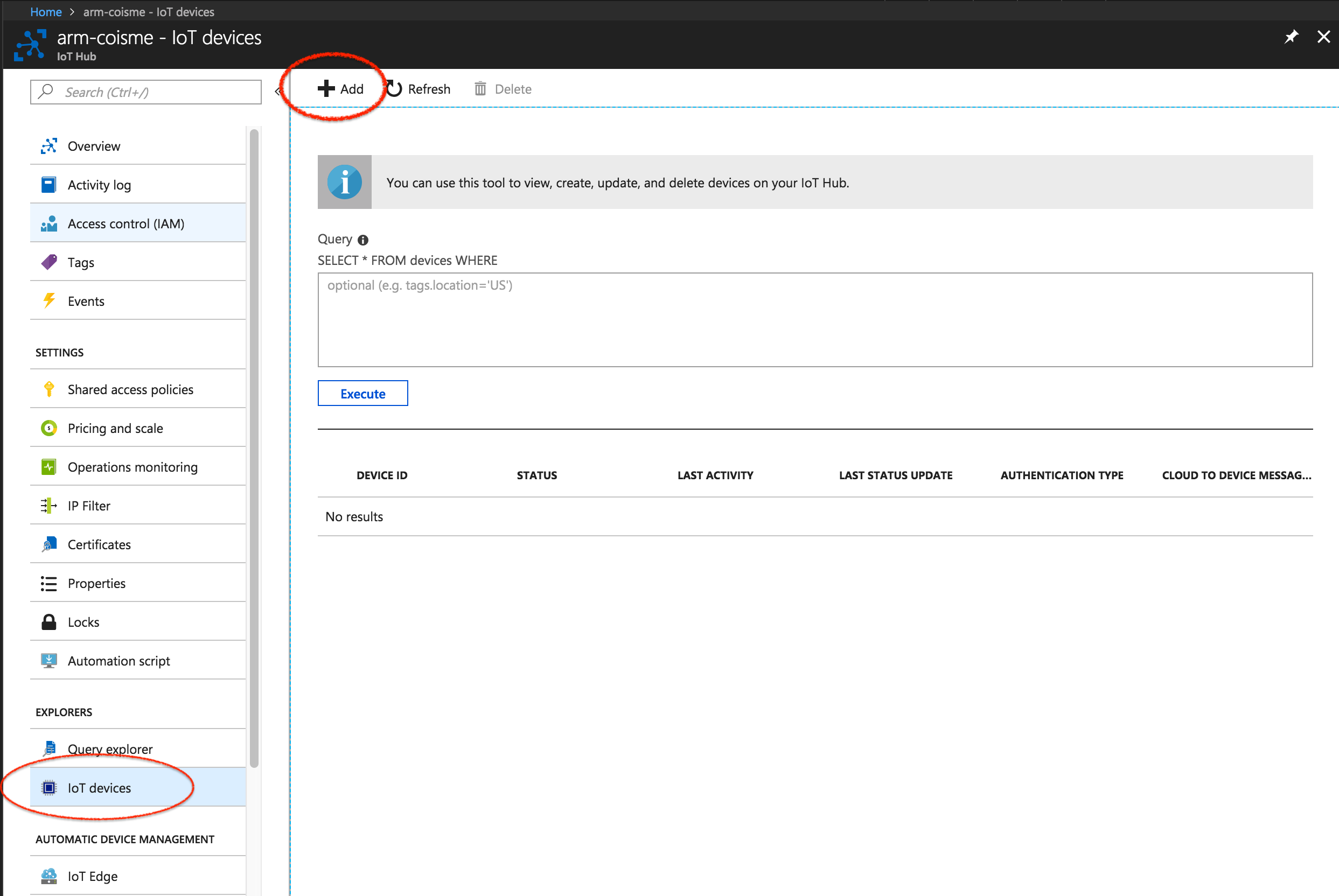
Add a new device
Go to Azure IoT Hub, then choose IoT Devices from the left menu. Then click the Add button.
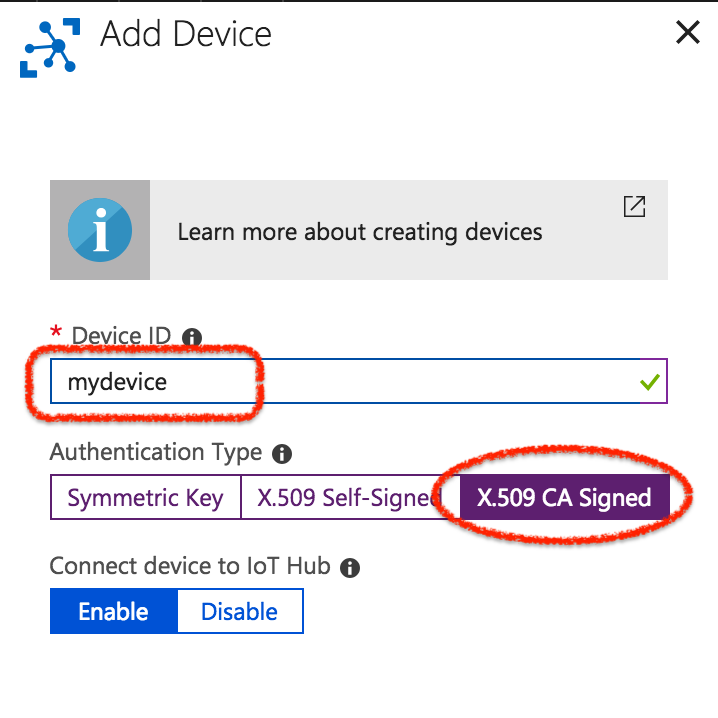
Input Device ID. Choose X.509 CA Signed for Authentication Type. Then click the Save button at the bottom.
Create certificates
Let's create certificates to connect your device to Azure IoT Hub. We use a certificate generation tool in azure-iot-sdk-c. Download the tool to your computer with this git command:
$ git clone https://github.com/Azure/azure-iot-sdk-c.git
Once download is finished, change the directory to azure-iot-sdk-c/tools/CACertificates. Then create certificates by following this instruction page.
Attention
At Step 4 - Create a new device in the instruction page above, choose IoT Leaf Device. The argument mydevice should be changed to your device ID which you input above.
We'll use these two files later:
azure-iot-sdk-c/tools/CACertificates/certs/new-device-full-chain.cert.pemazure-iot-sdk-c/tools/CACertificates/private/new-device.key.pem
Please keep these files.
That's it! All set in the IoT Hub side.
Build firmware
Next, let's build the firmware. You can use either online compiler or CLI. Here, we use the online compiler.
Import project
Log in to online compiler and click Import. You'll see the import wizard. Follow the link click here in the image below.
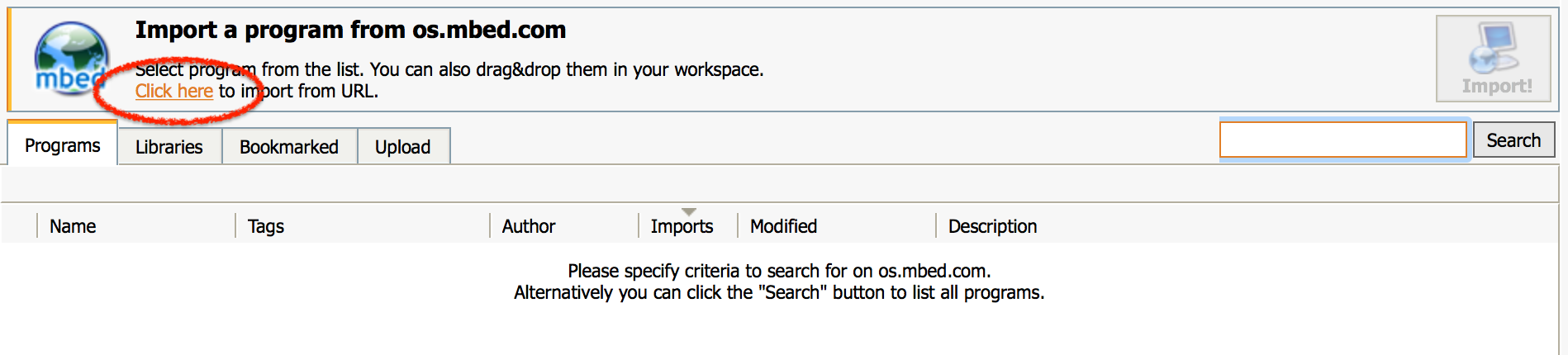
Input the repository URL https://github.com/coisme/Mbed-to-Azure-IoT-Hub into the Source URL textbox.
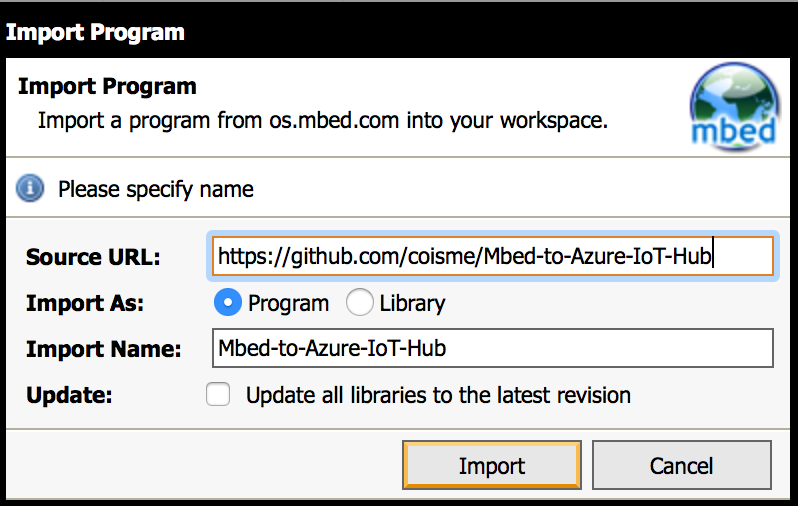
The project will be imported into your workspace.
Modify parameters
Edit MQTT_server_setting.h in the project root. Four parameters need to be changed.
DEVICE_ID- Device ID you input in the Add a new device section.MQTT_SERVER_HOST_NAME- Host name, <IoT hub name>.azure-devices.netSSL_CLIENT_CERT_PEM- Client certificate in PEM format.SSL_CLIENT_PRIVATE_KEY_PEM- Client private key in PEM format.
SSL_CLIENT_CERT_PEM
The contents of new-device-full-chain.cert.pem created in the Create certificates section. You need to add " at the head and \n" at the tail of each line of the .pem file.
Example of SSL_CLIENT_CERT_PEM
const char* SSL_CLIENT_CERT_PEM = "-----BEGIN CERTIFICATE-----\n" "MIIFszCCA5ugAwIBAgIBBDANBgkqhkiG9w0BAQsFADA0MTIwMAYDVQQDDClBenVy\n" ...
SSL_CLIENT_PRIVATE_KEY_PEM
The contents of new-device.key.pem created in the Create certifications section. Do not share this key with anyone. You need to add " at the head and \n" at the tail of each line of the .pem file.
Example of SSL_CLIENT_PRIVATE_KEY_PEM
const char* SSL_CLIENT_PRIVATE_KEY_PEM = "-----BEGIN RSA PRIVATE KEY-----\n" "MIIJKAIBAAKCAgEApiYeU3PBEdfnhpYL8UBc56iptcmD/XtjWs5qMIadDmU8TlMT\n" ...
Once you finish editing, save the file.
Compile
Click the Compile button in the top menu.
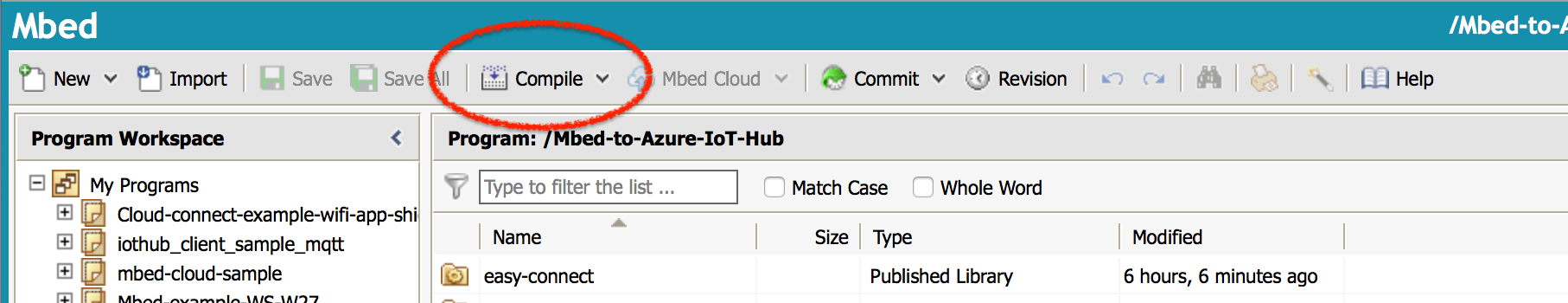
If compilation done successfully, <project name>.bin file will be downloaded. Please flash the <project name>.bin file to your target board.
Run
Let's run the application and see how it works.
Connect to your board
To see messages from your board via USB serial, run this command from the terminal:
$ mbed sterm -b 115200
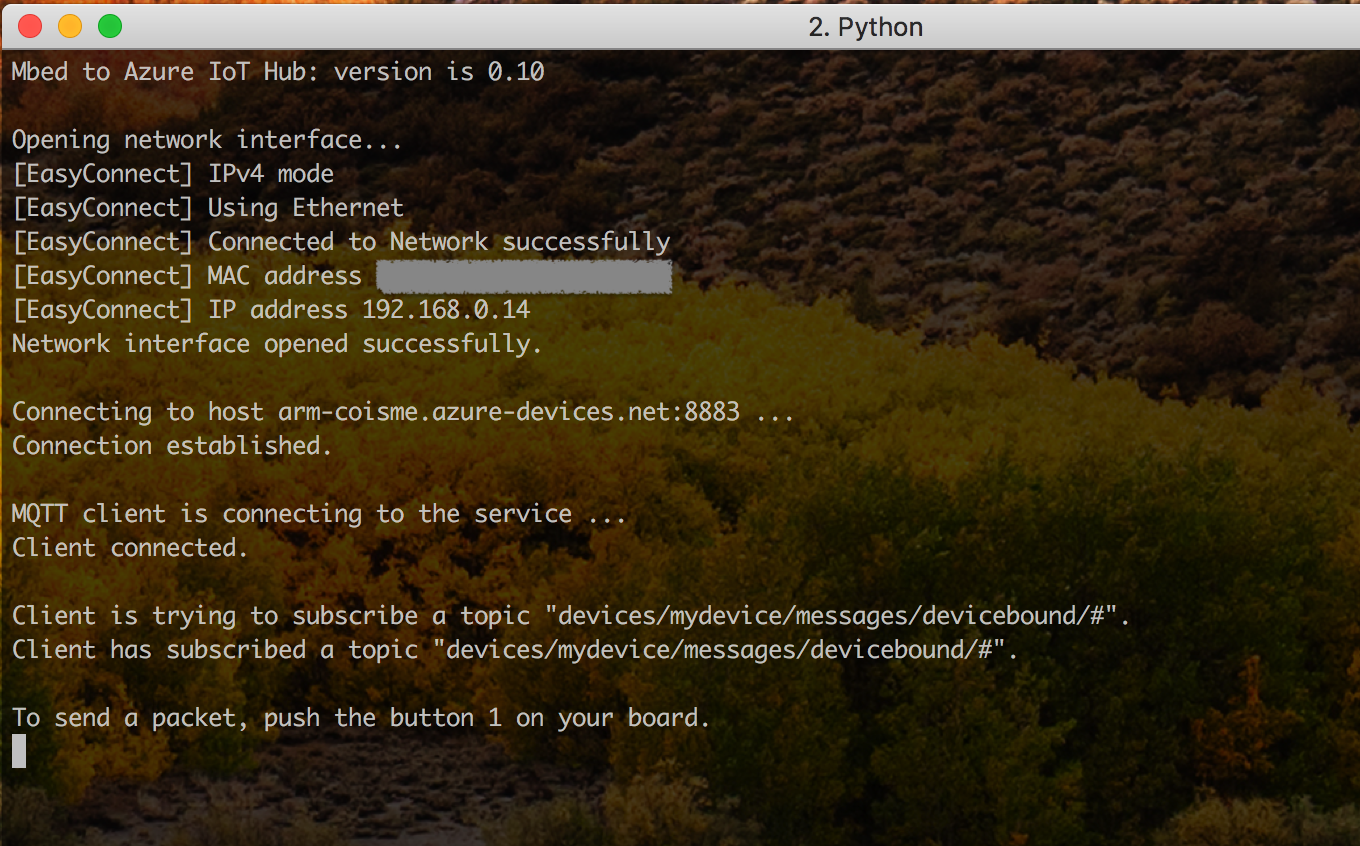
Push the reset button on your board, application will be relaunch. You'll see messages from your board like the picture below:
Set up IoT Hub Explorer
To test the communication between the device and IoT Hub, we'll use IoT Hub Explorer tool. Please install it by following the instruction on its GitHub page.
https://github.com/azure/iothub-explorer
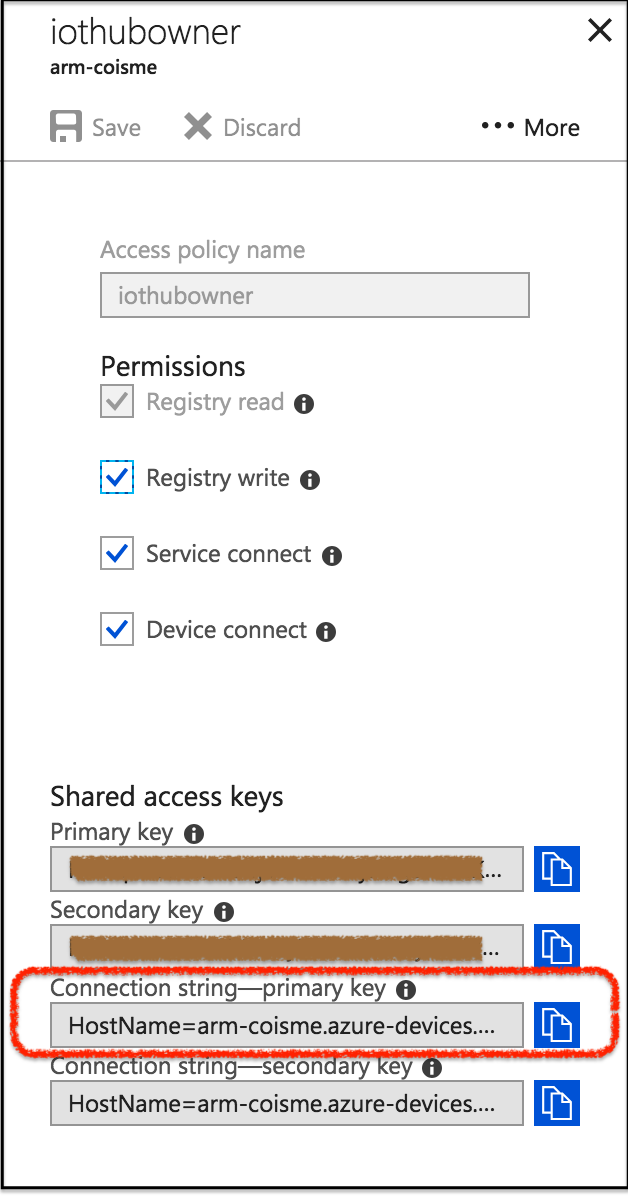
To run the test commands, we need Device ID and Connection String. Device ID is the one you used above. To get your connection string, go to IoT Hub and click Shared Access Policies. Then click iothubowner.
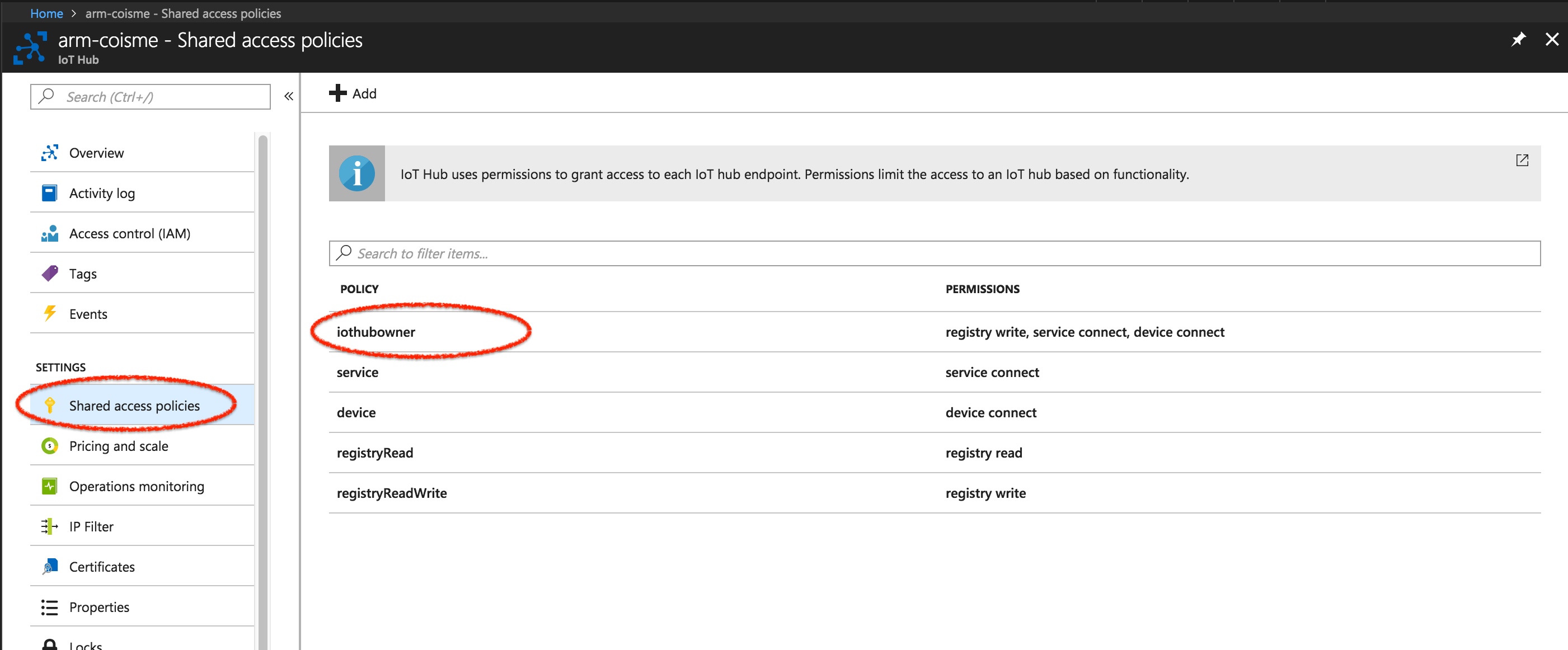
You'll find the connection string at the bottom.
Send a message from Device to Cloud (D2C)
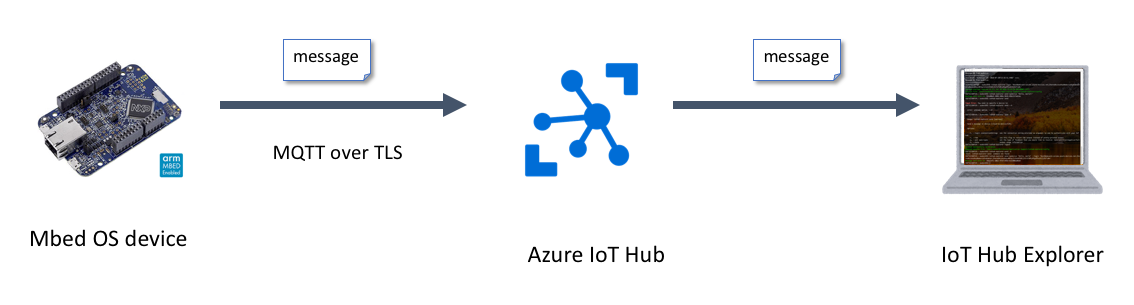
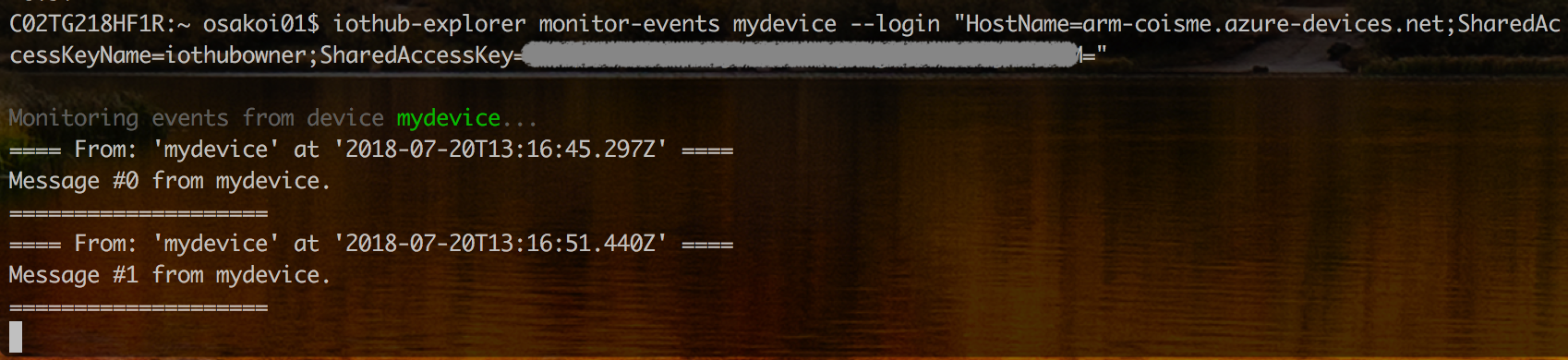
To send a message from your device to IoT Hub, push the button 1 on your board. To confirm that the message arrives at IoT Hub, run this command on the terminal:
$ iothub-explorer monitor-events <device-id> --login "<IoTHubConnectionString>"
When you push the button 1 on your board, a message is sent to your IoT Hub. You'll see that IoT Hub Explorer receives a message from your IoT Hub. Message content is "Message #<n> from <Device ID>" where <n> is a number of button count.
Send a message from Cloud to Device (C2D)
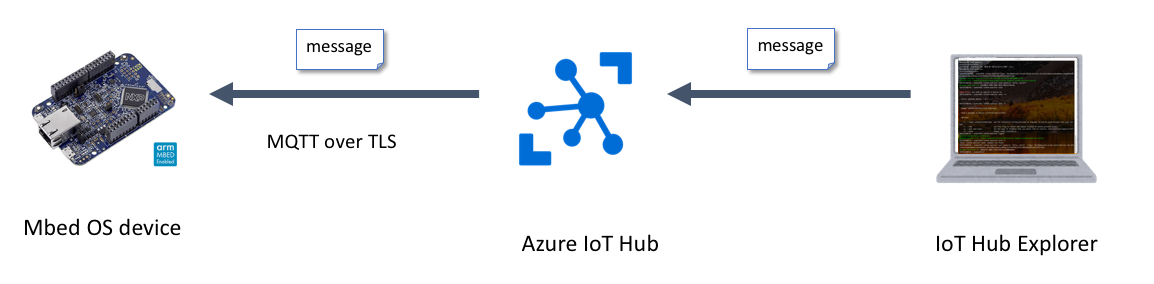
To send a message from PC to your device via IoT Hub, run this command from the terminal:
$ iothub-explorer send <device-id> "<message>" --login "<IoTHubConnectionString>"
When you run this command, a message is sent from Azure IoT Explorer running on your PC to your device via IoT Hub. You'll see the message on the device's terminal.

7 comments on Azure IoT Hub from Mbed OS device:
Please log in to post comments.

Hey,
I am trying this example on target nRF52840, It's not working on this target. Terminal Logs are not after "Connecting to host arm-iot-poc.azure-devices.net:8883 ..."
Looks like stuck in TLS constructor.
Have anyone tried this on nRF52840?
Thanks in advance.