SX1276 Shield based Applications
Dependencies: X_NUCLEO_IKS01A1 LoRaWAN-lib SX1276Lib mbed
LoRaWAN-SX1276-Application Demo uses SX1276MB1LAS mbed component shield on a nucleo board platform to demonstrate a Class-A LoRaWAN device in the 915MHz ISM band for North American region. It uses the LoRaWAN-lib and SX1276Lib libraries.
Comissioning.h (LoRaWAN Network Configuration)
The end-device can be activated in one of the two ways:
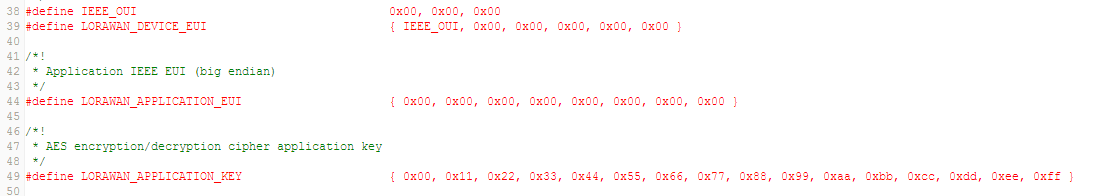
Over the Air (OTA) activation can be enabled as shown in the figure below.
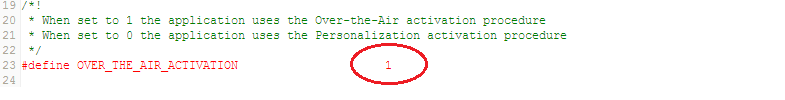
The end-device must be configured with the following parameters:
LORAWAN_DEVICE_EUI(8 Bytes) : Fist 3 Bytes is the Organizationally Unique Identifier (OUI) followed by 5 bytes of unique ID. If not defined by user, then the firmware automatically assigns one to the end-deviceLORAWAN_APPLICATION_EUI(8 Bytes)LORAWAN_APPLICATION_KEY(or DEVKEY) (16 Bytes)
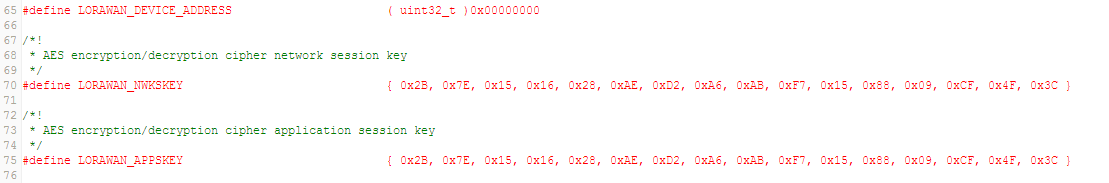
Activation by Personalization (ABP) can be enabled as shown in the figure below.
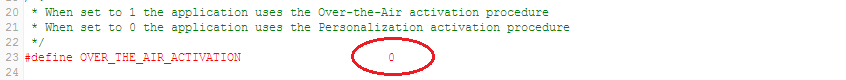
The end-device must be configured with the following parameters:
LORAWAN_DEVICE_ADDRESS(4 Bytes) : If not defined by user, then the firmware automatically assigns one to the end-deviceLORAWAN_NWKSKEY(16 Bytes)LORAWAN_APPSKEY(16 Bytes)
Config.h (LoRaWAN Communication Parameters)
- Mode of Operation : Hybrid
If the end-device needs to be configured to operate over 8-channels, then
Hybrid Modeneeds to be enabled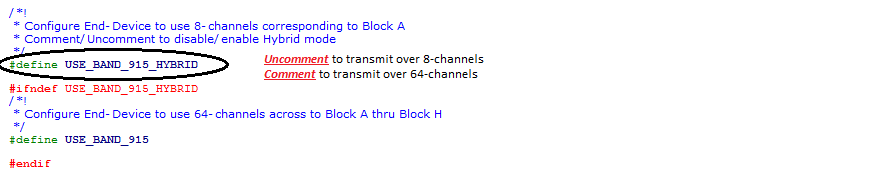
- Mode of Operation : Frequency Hop
If the end-device needs to be configured to operate over 64-channels, then
Hybrid Modeneeds to be disabled
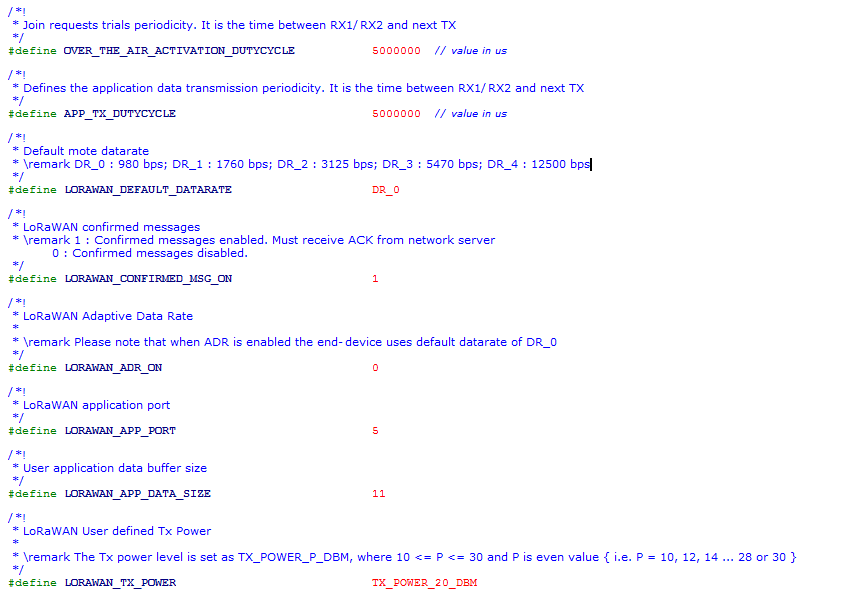
- Delay between successive JOIN REQUESTs :
The delay between successive Join Requests (until the end-device joins the network) can be configured using the parameter
OVER_THE_AIR_ACTIVATION_DUTYCYCLE
- Inter-Frame Delay :
One can change the delay between each frame transmission using
APP_TX_DUTYCYCLEIt is advisable thatAPP_TX_DUTYCYCLEis greater than or equal to 3sec.
- Data Rate :
The data rate can be configured as per LoRaWAN specification using the paramter
LORAWAN_DEFAULT_DATARATE. The range of values are DR_0, DR_1, DR_2, DR_3 and DR_4
- Confirmed/Unconfirmed Messages :
The uplink message or payload can be chosen to be confirmed or unconfirmed using the parameter
LORAWAN_CONFIRMED_MSG_ON. When set to 1, the transmitted messages need to be confirmed with anACKby the network server in the subsequent RX window. When set to 0, noACKis requested.
- ADR ON/OFF :
The ADR can be enabled or disabled using the parameter
LORAWAN_ADR_ON. When set to 1, ADR is enabled and disabled when set to 0.
- Application Port :
The application port can be set using parameter
LORAWAN_APP_PORT. A few examples are associated to specific Application Port, and are defined in Config.h
- Payload Length :
The lenght of the payload (in bytes) to be transmitted can be configured using
LORAWAN_APP_DATA_SIZE
- Transmit Power :
The transmit power can be configured using
LORAWAN_TX_POWER(LoRaMAC verifies if the set power is compliant with the LoRaWAN spec and FCC guidelines)
The baud-rate for serial terminal display is 115200
system/crypto/cmac.cpp@0:42863a11464a, 2016-08-26 (annotated)
- Committer:
- ubhat
- Date:
- Fri Aug 26 19:36:35 2016 +0000
- Revision:
- 0:42863a11464a
SX1276 Shield based Applications
Who changed what in which revision?
| User | Revision | Line number | New contents of line |
|---|---|---|---|
| ubhat | 0:42863a11464a | 1 | /************************************************************************** |
| ubhat | 0:42863a11464a | 2 | Copyright (C) 2009 Lander Casado, Philippas Tsigas |
| ubhat | 0:42863a11464a | 3 | |
| ubhat | 0:42863a11464a | 4 | All rights reserved. |
| ubhat | 0:42863a11464a | 5 | |
| ubhat | 0:42863a11464a | 6 | Permission is hereby granted, free of charge, to any person obtaining |
| ubhat | 0:42863a11464a | 7 | a copy of this software and associated documentation files |
| ubhat | 0:42863a11464a | 8 | (the "Software"), to deal with the Software without restriction, including |
| ubhat | 0:42863a11464a | 9 | without limitation the rights to use, copy, modify, merge, publish, |
| ubhat | 0:42863a11464a | 10 | distribute, sublicense, and/or sell copies of the Software, and to |
| ubhat | 0:42863a11464a | 11 | permit persons to whom the Software is furnished to do so, subject to |
| ubhat | 0:42863a11464a | 12 | the following conditions: |
| ubhat | 0:42863a11464a | 13 | |
| ubhat | 0:42863a11464a | 14 | Redistributions of source code must retain the above copyright notice, |
| ubhat | 0:42863a11464a | 15 | this list of conditions and the following disclaimers. Redistributions in |
| ubhat | 0:42863a11464a | 16 | binary form must reproduce the above copyright notice, this list of |
| ubhat | 0:42863a11464a | 17 | conditions and the following disclaimers in the documentation and/or |
| ubhat | 0:42863a11464a | 18 | other materials provided with the distribution. |
| ubhat | 0:42863a11464a | 19 | |
| ubhat | 0:42863a11464a | 20 | In no event shall the authors or copyright holders be liable for any special, |
| ubhat | 0:42863a11464a | 21 | incidental, indirect or consequential damages of any kind, or any damages |
| ubhat | 0:42863a11464a | 22 | whatsoever resulting from loss of use, data or profits, whether or not |
| ubhat | 0:42863a11464a | 23 | advised of the possibility of damage, and on any theory of liability, |
| ubhat | 0:42863a11464a | 24 | arising out of or in connection with the use or performance of this software. |
| ubhat | 0:42863a11464a | 25 | |
| ubhat | 0:42863a11464a | 26 | THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS |
| ubhat | 0:42863a11464a | 27 | OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, |
| ubhat | 0:42863a11464a | 28 | FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE |
| ubhat | 0:42863a11464a | 29 | CONTRIBUTORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER |
| ubhat | 0:42863a11464a | 30 | LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING |
| ubhat | 0:42863a11464a | 31 | FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER |
| ubhat | 0:42863a11464a | 32 | DEALINGS WITH THE SOFTWARE |
| ubhat | 0:42863a11464a | 33 | |
| ubhat | 0:42863a11464a | 34 | *****************************************************************************/ |
| ubhat | 0:42863a11464a | 35 | //#include <sys/param.h> |
| ubhat | 0:42863a11464a | 36 | //#include <sys/systm.h> |
| ubhat | 0:42863a11464a | 37 | #include <stdint.h> |
| ubhat | 0:42863a11464a | 38 | #include "aes.h" |
| ubhat | 0:42863a11464a | 39 | #include "cmac.h" |
| ubhat | 0:42863a11464a | 40 | #include "utilities.h" |
| ubhat | 0:42863a11464a | 41 | |
| ubhat | 0:42863a11464a | 42 | #define LSHIFT(v, r) do { \ |
| ubhat | 0:42863a11464a | 43 | int32_t i; \ |
| ubhat | 0:42863a11464a | 44 | for (i = 0; i < 15; i++) \ |
| ubhat | 0:42863a11464a | 45 | (r)[i] = (v)[i] << 1 | (v)[i + 1] >> 7; \ |
| ubhat | 0:42863a11464a | 46 | (r)[15] = (v)[15] << 1; \ |
| ubhat | 0:42863a11464a | 47 | } while (0) |
| ubhat | 0:42863a11464a | 48 | |
| ubhat | 0:42863a11464a | 49 | #define XOR(v, r) do { \ |
| ubhat | 0:42863a11464a | 50 | int32_t i; \ |
| ubhat | 0:42863a11464a | 51 | for (i = 0; i < 16; i++) \ |
| ubhat | 0:42863a11464a | 52 | { \ |
| ubhat | 0:42863a11464a | 53 | (r)[i] = (r)[i] ^ (v)[i]; \ |
| ubhat | 0:42863a11464a | 54 | } \ |
| ubhat | 0:42863a11464a | 55 | } while (0) \ |
| ubhat | 0:42863a11464a | 56 | |
| ubhat | 0:42863a11464a | 57 | |
| ubhat | 0:42863a11464a | 58 | void AES_CMAC_Init(AES_CMAC_CTX *ctx) |
| ubhat | 0:42863a11464a | 59 | { |
| ubhat | 0:42863a11464a | 60 | memset1(ctx->X, 0, sizeof ctx->X); |
| ubhat | 0:42863a11464a | 61 | ctx->M_n = 0; |
| ubhat | 0:42863a11464a | 62 | memset1(ctx->rijndael.ksch, '\0', 240); |
| ubhat | 0:42863a11464a | 63 | } |
| ubhat | 0:42863a11464a | 64 | |
| ubhat | 0:42863a11464a | 65 | void AES_CMAC_SetKey(AES_CMAC_CTX *ctx, const uint8_t key[AES_CMAC_KEY_LENGTH]) |
| ubhat | 0:42863a11464a | 66 | { |
| ubhat | 0:42863a11464a | 67 | //rijndael_set_key_enc_only(&ctx->rijndael, key, 128); |
| ubhat | 0:42863a11464a | 68 | aes_set_key( key, AES_CMAC_KEY_LENGTH, &ctx->rijndael); |
| ubhat | 0:42863a11464a | 69 | } |
| ubhat | 0:42863a11464a | 70 | |
| ubhat | 0:42863a11464a | 71 | void AES_CMAC_Update(AES_CMAC_CTX *ctx, const uint8_t *data, uint32_t len) |
| ubhat | 0:42863a11464a | 72 | { |
| ubhat | 0:42863a11464a | 73 | uint32_t mlen; |
| ubhat | 0:42863a11464a | 74 | uint8_t in[16]; |
| ubhat | 0:42863a11464a | 75 | |
| ubhat | 0:42863a11464a | 76 | if (ctx->M_n > 0) { |
| ubhat | 0:42863a11464a | 77 | mlen = MIN(16 - ctx->M_n, len); |
| ubhat | 0:42863a11464a | 78 | memcpy1(ctx->M_last + ctx->M_n, data, mlen); |
| ubhat | 0:42863a11464a | 79 | ctx->M_n += mlen; |
| ubhat | 0:42863a11464a | 80 | if (ctx->M_n < 16 || len == mlen) |
| ubhat | 0:42863a11464a | 81 | return; |
| ubhat | 0:42863a11464a | 82 | XOR(ctx->M_last, ctx->X); |
| ubhat | 0:42863a11464a | 83 | //rijndael_encrypt(&ctx->rijndael, ctx->X, ctx->X); |
| ubhat | 0:42863a11464a | 84 | aes_encrypt( ctx->X, ctx->X, &ctx->rijndael); |
| ubhat | 0:42863a11464a | 85 | data += mlen; |
| ubhat | 0:42863a11464a | 86 | len -= mlen; |
| ubhat | 0:42863a11464a | 87 | } |
| ubhat | 0:42863a11464a | 88 | while (len > 16) { /* not last block */ |
| ubhat | 0:42863a11464a | 89 | |
| ubhat | 0:42863a11464a | 90 | XOR(data, ctx->X); |
| ubhat | 0:42863a11464a | 91 | //rijndael_encrypt(&ctx->rijndael, ctx->X, ctx->X); |
| ubhat | 0:42863a11464a | 92 | |
| ubhat | 0:42863a11464a | 93 | memcpy1(in, &ctx->X[0], 16); //Bestela ez du ondo iten |
| ubhat | 0:42863a11464a | 94 | aes_encrypt( in, in, &ctx->rijndael); |
| ubhat | 0:42863a11464a | 95 | memcpy1(&ctx->X[0], in, 16); |
| ubhat | 0:42863a11464a | 96 | |
| ubhat | 0:42863a11464a | 97 | data += 16; |
| ubhat | 0:42863a11464a | 98 | len -= 16; |
| ubhat | 0:42863a11464a | 99 | } |
| ubhat | 0:42863a11464a | 100 | /* potential last block, save it */ |
| ubhat | 0:42863a11464a | 101 | memcpy1(ctx->M_last, data, len); |
| ubhat | 0:42863a11464a | 102 | ctx->M_n = len; |
| ubhat | 0:42863a11464a | 103 | } |
| ubhat | 0:42863a11464a | 104 | |
| ubhat | 0:42863a11464a | 105 | void AES_CMAC_Final(uint8_t digest[AES_CMAC_DIGEST_LENGTH], AES_CMAC_CTX *ctx) |
| ubhat | 0:42863a11464a | 106 | { |
| ubhat | 0:42863a11464a | 107 | uint8_t K[16]; |
| ubhat | 0:42863a11464a | 108 | uint8_t in[16]; |
| ubhat | 0:42863a11464a | 109 | /* generate subkey K1 */ |
| ubhat | 0:42863a11464a | 110 | memset1(K, '\0', 16); |
| ubhat | 0:42863a11464a | 111 | |
| ubhat | 0:42863a11464a | 112 | //rijndael_encrypt(&ctx->rijndael, K, K); |
| ubhat | 0:42863a11464a | 113 | |
| ubhat | 0:42863a11464a | 114 | aes_encrypt( K, K, &ctx->rijndael); |
| ubhat | 0:42863a11464a | 115 | |
| ubhat | 0:42863a11464a | 116 | if (K[0] & 0x80) { |
| ubhat | 0:42863a11464a | 117 | LSHIFT(K, K); |
| ubhat | 0:42863a11464a | 118 | K[15] ^= 0x87; |
| ubhat | 0:42863a11464a | 119 | } else |
| ubhat | 0:42863a11464a | 120 | LSHIFT(K, K); |
| ubhat | 0:42863a11464a | 121 | |
| ubhat | 0:42863a11464a | 122 | |
| ubhat | 0:42863a11464a | 123 | if (ctx->M_n == 16) { |
| ubhat | 0:42863a11464a | 124 | /* last block was a complete block */ |
| ubhat | 0:42863a11464a | 125 | XOR(K, ctx->M_last); |
| ubhat | 0:42863a11464a | 126 | |
| ubhat | 0:42863a11464a | 127 | } else { |
| ubhat | 0:42863a11464a | 128 | /* generate subkey K2 */ |
| ubhat | 0:42863a11464a | 129 | if (K[0] & 0x80) { |
| ubhat | 0:42863a11464a | 130 | LSHIFT(K, K); |
| ubhat | 0:42863a11464a | 131 | K[15] ^= 0x87; |
| ubhat | 0:42863a11464a | 132 | } else |
| ubhat | 0:42863a11464a | 133 | LSHIFT(K, K); |
| ubhat | 0:42863a11464a | 134 | |
| ubhat | 0:42863a11464a | 135 | /* padding(M_last) */ |
| ubhat | 0:42863a11464a | 136 | ctx->M_last[ctx->M_n] = 0x80; |
| ubhat | 0:42863a11464a | 137 | while (++ctx->M_n < 16) |
| ubhat | 0:42863a11464a | 138 | ctx->M_last[ctx->M_n] = 0; |
| ubhat | 0:42863a11464a | 139 | |
| ubhat | 0:42863a11464a | 140 | XOR(K, ctx->M_last); |
| ubhat | 0:42863a11464a | 141 | |
| ubhat | 0:42863a11464a | 142 | |
| ubhat | 0:42863a11464a | 143 | } |
| ubhat | 0:42863a11464a | 144 | XOR(ctx->M_last, ctx->X); |
| ubhat | 0:42863a11464a | 145 | |
| ubhat | 0:42863a11464a | 146 | //rijndael_encrypt(&ctx->rijndael, ctx->X, digest); |
| ubhat | 0:42863a11464a | 147 | |
| ubhat | 0:42863a11464a | 148 | memcpy1(in, &ctx->X[0], 16); //Bestela ez du ondo iten |
| ubhat | 0:42863a11464a | 149 | aes_encrypt(in, digest, &ctx->rijndael); |
| ubhat | 0:42863a11464a | 150 | memset1(K, 0, sizeof K); |
| ubhat | 0:42863a11464a | 151 | |
| ubhat | 0:42863a11464a | 152 | } |
| ubhat | 0:42863a11464a | 153 |