Small Internet Protocol Stack using a standard serial port.
PPP-Blinky - TCP/IP Networking Over a Serial Port
Note: The source code is at the bottom of this page.
A Windows desktop showing PPP-Blinky in the network connections list.
Describe PPP-Blinky in Three Sentences
PPP-Blinky is a tiny library that enables Internet protocols (IPv4) to any mbed target hardware by using only a serial port.
The code runs on processors with as little as 8k RAM, for example the Nucleo-L053R8 board.
PPP-Blinky uses the industry-standard PPP (Point-to-Point) Protocol and a tiny "stateless" TCP/IP stack.
No Ethernet Port Required
No ethernet port is required - PPP-Blinky uses a serial port to send IP packets to your PC.
PPP-Blinky emulates a standard dial-up modem and therefore connects to Windows, Linux or Adroid machines.
The code runs on most ARM mbed platforms such as the LPC11U24 shown in the picture below:
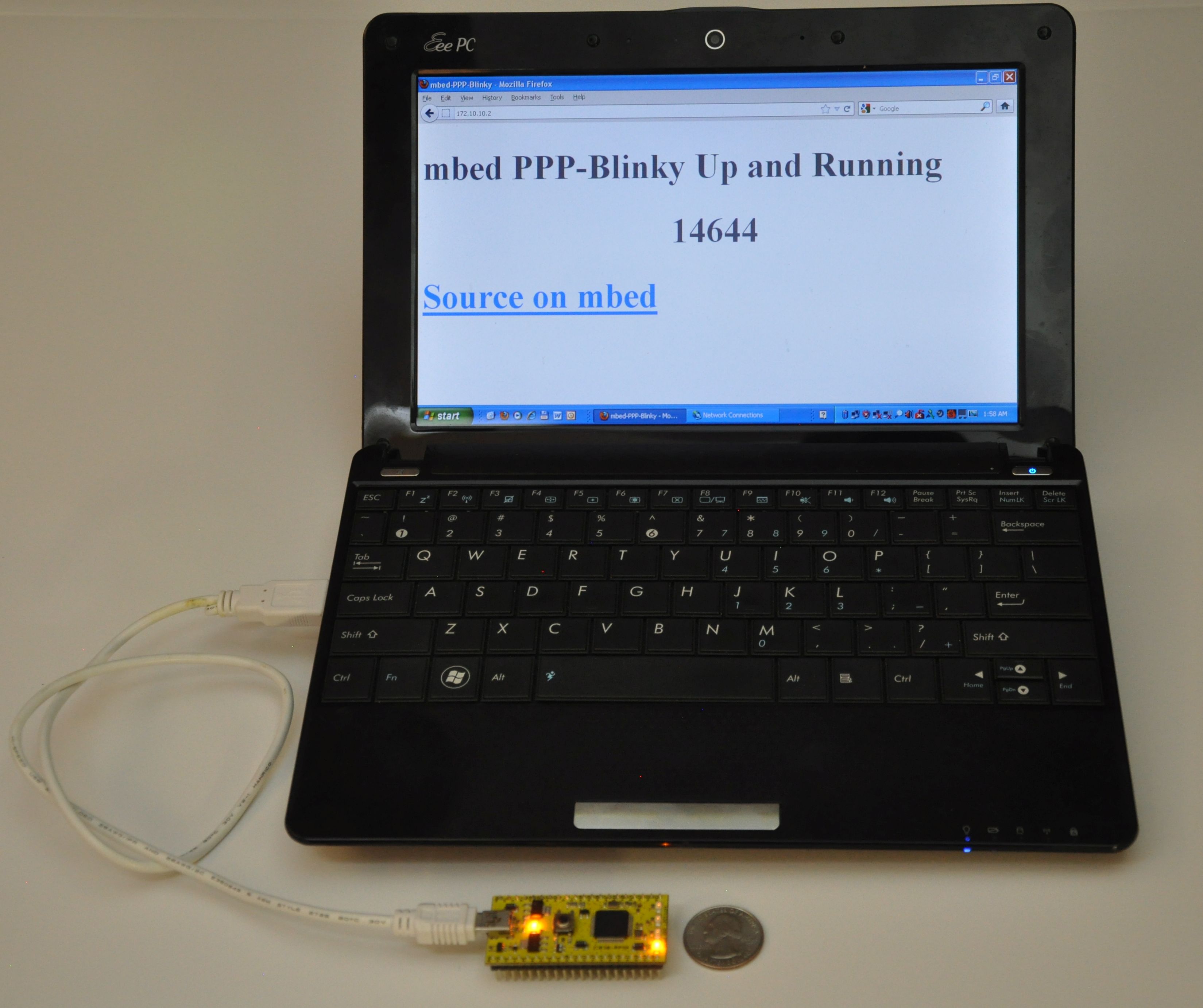 mbed LPC11u24 acting as a webserver to a Windows laptop.
mbed LPC11u24 acting as a webserver to a Windows laptop.
Webserver
The Webserver and WebSocket functions are ideal for building browser-based GUIs on mbed-enabled hardware.
PPP-Blinky's HTTP webserver works with most web clients such as Internet Explorer, Mozilla Firefox, Google Chrome, Safari, Curl, wget and Lynx as well as Microsoft Powershell Invoke-Webrequest command.
In the image below Firefox web browser displays the main web page embedded into PPP-Blinky's code:
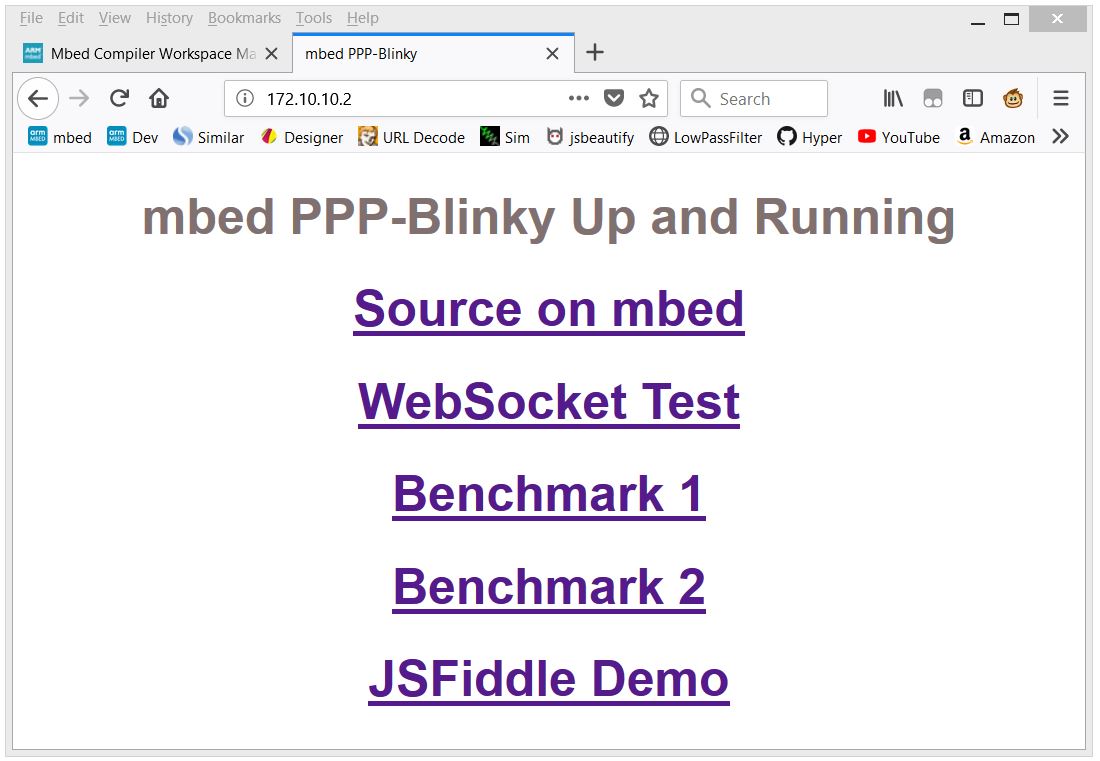 Firefox web browser displays a web page embedded into PPP-Blinky's code
Firefox web browser displays a web page embedded into PPP-Blinky's code
WebSocket Service
WebSocket is the most popular protocol standard for real-time bidirectional TCP/IP communication between clients and servers.
In the image below a small Internet Explorer script has connected to PPP-Blinky's WebSocket Service.
A websocket message was then sent by the browser and was echoed back by the WebSocket, triggering the onmessage event in the script.
The WebSocket service enables bidirectional real-time interaction between PPP-Blinky and any element in the browser DOM via JavaScript.
If you already have PPP-Blinky up and running you can test your WebSocket service using this: http://jsfiddle.net/d26cyuh2/112/embedded/result
Websockets are ideal for building browser-based GUIs for mbed hardware.
Trying PPP-Blinky on your mbed board
You will need an mbed-enabled hardware board: https://developer.mbed.org/platforms/
Establish a serial port connection between your host PC and your mbed board.
The easiest way is to use mbed hardware with a USB serial debug port. I've tried the ST-Micro Nucleo-L476RG, Nucleo-L152RE, Nucleo-F401RE, Nucleo-L432KC, Nucleo-L053R8, mbed-LPC11U24 and mbed-LPC1768 boards and they all work out of the box. Use the mbed online compiler to compile the software for your target board. Save the compiled binary to your hardware.
Before establishing a network connection, you can verify the operation of the code by opening a terminal program such as Tera Term, and setting the baud rate of the COM port on your mbed board to 115200 baud. LED1 should toggle for every two 0x7E (~) (i.e. tilde) characters you type, as 0x7E is the PPP frame start/end marker. Don't forget to close the port when your'e done testing, or else Windows Dial-up Networking will report that the COM port is in use by another program when you try to connect.
Once you are certain that the serial port and firmware is working, proceed to creating a new network connection on your PC -see below.
Creating a Dial-up Connection in Windows
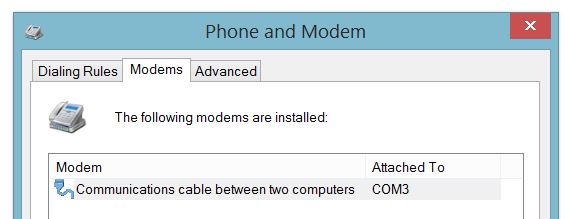
Setting up Dial-Up Networking (DUN) on your Windows 7 or 8 PC is essentially a two-step process: First, you create a new modem device, because PPP-blinky partially emulates a standard Windows serial port modem device. Second, you create a new Internet connection (in practice, a new network adapter) which is associated with your new "modem".
Step-by-step description of how to configure Windows for PPP-Blinky here:
/users/nixnax/code/PPP-Blinky/wiki/Configuring-Windows-Dial-Up-Networking
There is also a screen on how to set up Linux dial-up networking near the bottom of this page.
Connecting to PPP-Blinky from your PC
Once Windows networking is configured you can establish a dial-up connection to your mbed board over the USB virtual com port.
The IP address you manually assigned to the new dial-up network adapter (172.10.10.1) functions as a gateway to any valid IP address on that subnet. In the screen capture below, I'm sending pings from the Windows 8 command line to my ST-Micro Nucleo-L476RG board over the USB virtual serial Port. I'm also using a second serial port and Tera Term to capture the debug output from a second serial port on the hardware. The optional debug output from the board prints out the IP source and destination address and the first few bytes of the data payload. Note that the source is the adapter IP address, (172.10.10.1 in this case) and the destination is some other address on that subnet - all packets to the subnet are sent to our mbed hardware. For example, you could also ping 172.10.10.123 or, if your PPP-Blinky is running, simply click on this link: http://172.10.10.123
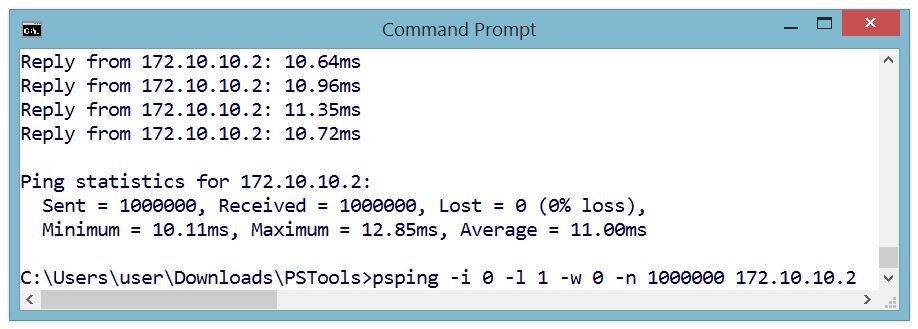
One Million Pings!
In the image below the ICMP ("ping") echo reply service was tested by sending one million pings to ppp-Blinky. This took over two hours.
The ping tool used on the Windows 8 PC was psping.exe from PsTools by Mark Russinovich - http://bit.ly/PingFast
The average reply time for a short ping (1 byte of payload data) was 11 milliseconds at 115200 baud on the $10 Nucleo-L053R8 board - barely enough time for 130 bytes to be sent over the port!
Monitoring PPP-Blinky Packets
The image below is from a Microsoft Network Monitor 3.4 capture session.
Responses from PPP-Blinky are shown in blue.
Frame 2 - Internet Explorer at IP 172.10.10.1 (the Dial-Up Adapter IP) requests a TCP connection by sending an S (SYN) flag.
Frame 3 - PPP-Blinky at IP 172.10.10.2 responds with an ACK in frame 3. One direction of the link is now established.
Frame 4 - The PC acknowledges the SYN sent by PPP-Blinky in frame 3. The TCP link is now fully established.
Frame 5 - The browser "pushes" (P flag is set) an HTTP GET request to PPP-Blinky.
Frame 6 - PPP-Blinky responds with a standard HTTP response "pushes" (P flag set) back a small web page. It also sets the A (ACK) flag to acknowledge the message sent in frame 6.
Frame 7 - The PC acknowledges reception of the HTTP payload.
Frame 8 - The PC starts to shut down the TCP connection by sending a FIN flag.
Frame 9 - PPP-Blinky acknowledges the FIN request - the connection is now closed in one direction. It also sets a FIN flag in the response to request closure of the opposite direction of the connection.
Frame 10 - The PC acknowledges the FIN request. The closing of the TCP connection is now confirmed in both directions.
Debug Output
PPP-Blinky can output handy debug information to an optional second serial port.
The image below shows the debug output (Ident, Source, Destination, TCP Flags) for a complete HTTP conversation.
The PC messages are displayed in black. PPP-Blinky messages are blue.
Notice how PPP-blinky automatically inserts a blank line after each full HTTP conversation.
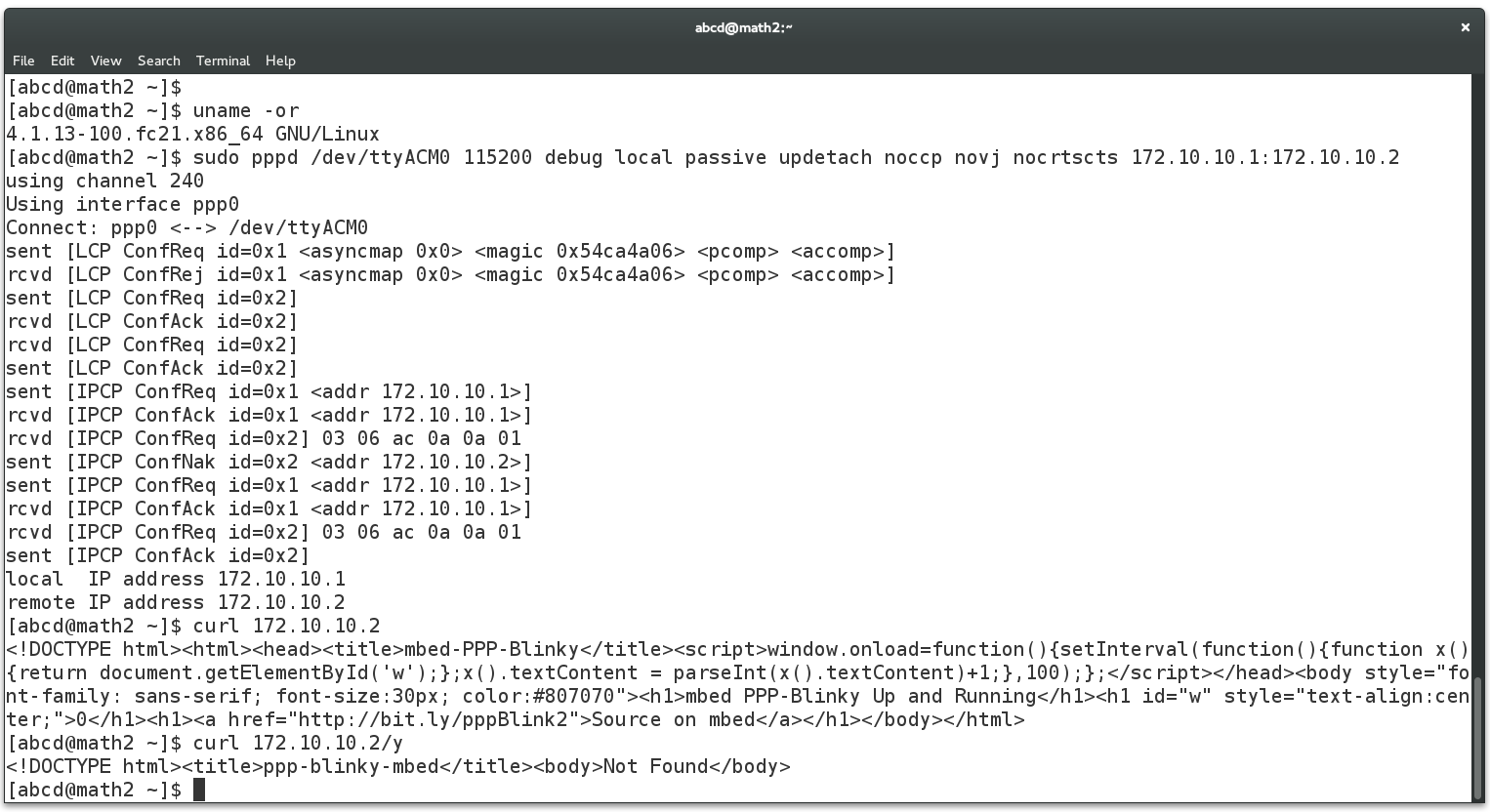
Creating a Dial-Up Connection in Linux
The screen below shows the required pppd command to connect to PPP-Blinky from a Linux machine. This was much simpler than Windows! The USB serial port of the mbed LPC1768 board registered as /dev/ttyACM0 on my Linux box. Do a websearch on pppd if you want to learn more about pppd, the Linux PPP handler. Near the bottom of the screen below, two webpages are fetched (/ and /y) by using the curl command on the command line. Gnome Webkit and Firefox work fine, too. Also try echo GET / HTTP/1.1 | nc 172.10.10.2 which uses netcat, the "Swiss army knife" of networking tools. PPP-Blinky was also tested with ApacheBench, the Apache server benchmark software. After 100000 fetches, the mean page fetch rate was reported as 6 page fetches per second for a small page.
Caveats
PPP Blinky is an extremely sparse implementation (1.5k lines) of HTTP,WebSocket,TCP, UDP, ICMP, IPCP and LCP over PPP, requiring around 8kB of RAM. The minimum functionality required to establish connectivity is implemented. These are often acceptable tradeoffs for embedded projects as well as a handy tool to learn the practical details of everyday networking implementations.
main.cpp@10:74f8233f72c0, 2016-12-31 (annotated)
- Committer:
- nixnax
- Date:
- Sat Dec 31 03:13:46 2016 +0000
- Revision:
- 10:74f8233f72c0
- Parent:
- 9:0992486d4a30
- Child:
- 11:f58998c24f0b
Can receive UDP packets.
Who changed what in which revision?
| User | Revision | Line number | New contents of line |
|---|---|---|---|
| nixnax | 0:2cf4880c312a | 1 | #include "mbed.h" |
| nixnax | 0:2cf4880c312a | 2 | |
| nixnax | 0:2cf4880c312a | 3 | // Proof-of-concept for TCP/IP using Windows 7/8/10 Dial Up Networking over MBED USB Virtual COM Port |
| nixnax | 0:2cf4880c312a | 4 | |
| nixnax | 4:a469050d5b80 | 5 | // Toggles LED1 every time the PC sends an IP packet over the PPP link |
| nixnax | 4:a469050d5b80 | 6 | |
| nixnax | 4:a469050d5b80 | 7 | // Note - turn off all authentication, passwords, compression etc. Simplest link possible. |
| nixnax | 0:2cf4880c312a | 8 | |
| nixnax | 9:0992486d4a30 | 9 | // Handy links |
| nixnax | 6:fba4c2e817b8 | 10 | // http://atari.kensclassics.org/wcomlog.htm |
| nixnax | 6:fba4c2e817b8 | 11 | // https://technet.microsoft.com/en-us/library/cc957992.aspx |
| nixnax | 6:fba4c2e817b8 | 12 | // http://www.sunshine2k.de/coding/javascript/crc/crc_js.html |
| nixnax | 9:0992486d4a30 | 13 | // https://en.wikibooks.org/wiki/Serial_Programming/IP_Over_Serial_Connections |
| nixnax | 6:fba4c2e817b8 | 14 | |
| nixnax | 6:fba4c2e817b8 | 15 | Serial pc(USBTX, USBRX); // The USB com port - Set this up as a Dial-Up Modem on your pc |
| nixnax | 4:a469050d5b80 | 16 | Serial xx(PC_10, PC_11); // debug port - use a second USB serial port to monitor |
| nixnax | 0:2cf4880c312a | 17 | |
| nixnax | 9:0992486d4a30 | 18 | #define debug(x) xx.printf( x ) |
| nixnax | 9:0992486d4a30 | 19 | |
| nixnax | 4:a469050d5b80 | 20 | DigitalOut led1(LED1); |
| nixnax | 4:a469050d5b80 | 21 | |
| nixnax | 4:a469050d5b80 | 22 | #define FRAME_7E (0x7e) |
| nixnax | 9:0992486d4a30 | 23 | #define BUFLEN (1<<12) |
| nixnax | 4:a469050d5b80 | 24 | char rxbuf[BUFLEN]; |
| nixnax | 4:a469050d5b80 | 25 | char frbuf[3000]; // buffer for ppp frame |
| nixnax | 0:2cf4880c312a | 26 | |
| nixnax | 4:a469050d5b80 | 27 | struct { |
| nixnax | 4:a469050d5b80 | 28 | int online; |
| nixnax | 4:a469050d5b80 | 29 | struct { |
| nixnax | 4:a469050d5b80 | 30 | char * buf; |
| nixnax | 4:a469050d5b80 | 31 | int head; |
| nixnax | 4:a469050d5b80 | 32 | int tail; |
| nixnax | 9:0992486d4a30 | 33 | int total; |
| nixnax | 4:a469050d5b80 | 34 | } rx; // serial port buffer |
| nixnax | 4:a469050d5b80 | 35 | struct { |
| nixnax | 6:fba4c2e817b8 | 36 | int id; |
| nixnax | 4:a469050d5b80 | 37 | int len; |
| nixnax | 4:a469050d5b80 | 38 | int crc; |
| nixnax | 4:a469050d5b80 | 39 | char * buf; |
| nixnax | 4:a469050d5b80 | 40 | } pkt; // ppp buffer |
| nixnax | 4:a469050d5b80 | 41 | } ppp; |
| nixnax | 0:2cf4880c312a | 42 | |
| nixnax | 9:0992486d4a30 | 43 | void pppInitStruct(){ ppp.online=0; ppp.rx.buf=rxbuf; ppp.rx.tail=0; ppp.rx.head=0; ppp.rx.total=0; ppp.pkt.buf=frbuf; ppp.pkt.len=0;} |
| nixnax | 4:a469050d5b80 | 44 | |
| nixnax | 4:a469050d5b80 | 45 | int crcG; // frame check sequence (CRC) holder |
| nixnax | 4:a469050d5b80 | 46 | void crcDo(int x){for (int i=0;i<8;i++){crcG=((crcG&1)^(x&1))?(crcG>>1)^0x8408:crcG>>1;x>>=1;}} // crc calculator |
| nixnax | 4:a469050d5b80 | 47 | void crcReset(){crcG=0xffff;} // crc restart |
| nixnax | 9:0992486d4a30 | 48 | int crcBuf(char * buf, int size){crcReset();for(int i=0;i<size;i++)crcDo(*buf++);return crcG;} // crc on a block of memory |
| nixnax | 0:2cf4880c312a | 49 | |
| nixnax | 0:2cf4880c312a | 50 | void rxHandler() // serial port receive interrupt handler |
| nixnax | 0:2cf4880c312a | 51 | { |
| nixnax | 4:a469050d5b80 | 52 | ppp.rx.buf[ppp.rx.head]=pc.getc(); // insert in buffer |
| nixnax | 0:2cf4880c312a | 53 | __disable_irq(); |
| nixnax | 4:a469050d5b80 | 54 | ppp.rx.head=(ppp.rx.head+1)&(BUFLEN-1); |
| nixnax | 9:0992486d4a30 | 55 | ppp.rx.total++; |
| nixnax | 0:2cf4880c312a | 56 | __enable_irq(); |
| nixnax | 0:2cf4880c312a | 57 | } |
| nixnax | 0:2cf4880c312a | 58 | |
| nixnax | 0:2cf4880c312a | 59 | int pc_readable() // check if buffer has data |
| nixnax | 0:2cf4880c312a | 60 | { |
| nixnax | 4:a469050d5b80 | 61 | return (ppp.rx.head==ppp.rx.tail) ? 0 : 1 ; |
| nixnax | 0:2cf4880c312a | 62 | } |
| nixnax | 0:2cf4880c312a | 63 | |
| nixnax | 0:2cf4880c312a | 64 | int pc_getBuf() // get one character from the buffer |
| nixnax | 0:2cf4880c312a | 65 | { |
| nixnax | 0:2cf4880c312a | 66 | if (pc_readable()) { |
| nixnax | 4:a469050d5b80 | 67 | int x = ppp.rx.buf[ ppp.rx.tail ]; |
| nixnax | 4:a469050d5b80 | 68 | ppp.rx.tail=(ppp.rx.tail+1)&(BUFLEN-1); |
| nixnax | 0:2cf4880c312a | 69 | return x; |
| nixnax | 0:2cf4880c312a | 70 | } |
| nixnax | 0:2cf4880c312a | 71 | return -1; |
| nixnax | 0:2cf4880c312a | 72 | } |
| nixnax | 0:2cf4880c312a | 73 | |
| nixnax | 4:a469050d5b80 | 74 | void scanForConnectString(); // scan for connect attempts from pc |
| nixnax | 1:9e03798d4367 | 75 | |
| nixnax | 9:0992486d4a30 | 76 | void processFrame(int start, int end) { // process received frame |
| nixnax | 9:0992486d4a30 | 77 | if(start==end) { xx.printf("Null Frame c=%d\n",ppp.rx.total); pc.putc(0x7e); return; } |
| nixnax | 9:0992486d4a30 | 78 | crcReset(); |
| nixnax | 9:0992486d4a30 | 79 | char * dest = ppp.pkt.buf; |
| nixnax | 9:0992486d4a30 | 80 | ppp.pkt.len=0; |
| nixnax | 9:0992486d4a30 | 81 | int unstuff=0; |
| nixnax | 9:0992486d4a30 | 82 | for (int i=start; i<end; i++) { |
| nixnax | 9:0992486d4a30 | 83 | if (unstuff==0) { |
| nixnax | 9:0992486d4a30 | 84 | if (rxbuf[i]==0x7d) unstuff=1; |
| nixnax | 9:0992486d4a30 | 85 | else { *dest++ = rxbuf[i]; ppp.pkt.len++; crcDo(rxbuf[i]);} |
| nixnax | 9:0992486d4a30 | 86 | } else { |
| nixnax | 9:0992486d4a30 | 87 | *dest++ = rxbuf[i]^0x20; ppp.pkt.len++; crcDo((int)rxbuf[i]^0x20); |
| nixnax | 9:0992486d4a30 | 88 | unstuff=0; |
| nixnax | 9:0992486d4a30 | 89 | } |
| nixnax | 9:0992486d4a30 | 90 | } |
| nixnax | 9:0992486d4a30 | 91 | ppp.pkt.crc = crcG & 0xffff; |
| nixnax | 9:0992486d4a30 | 92 | if (ppp.pkt.crc == 0xf0b8) { // check for good CRC |
| nixnax | 9:0992486d4a30 | 93 | void determinePacketType(); // declare early |
| nixnax | 9:0992486d4a30 | 94 | determinePacketType(); |
| nixnax | 9:0992486d4a30 | 95 | } else { |
| nixnax | 9:0992486d4a30 | 96 | xx.printf("CRC was %x \n",ppp.pkt.crc); |
| nixnax | 9:0992486d4a30 | 97 | for(int i=0;i<ppp.pkt.len;i++)xx.printf("%02x ", ppp.pkt.buf[i]); |
| nixnax | 9:0992486d4a30 | 98 | xx.printf("\nLen = %d\n", ppp.pkt.len); |
| nixnax | 9:0992486d4a30 | 99 | } |
| nixnax | 9:0992486d4a30 | 100 | } |
| nixnax | 9:0992486d4a30 | 101 | |
| nixnax | 9:0992486d4a30 | 102 | |
| nixnax | 9:0992486d4a30 | 103 | void generalFrame() { |
| nixnax | 9:0992486d4a30 | 104 | debug("== General Frame ==\n"); |
| nixnax | 9:0992486d4a30 | 105 | for(int i=0;i<ppp.pkt.len;i++) xx.printf("%02x ", ppp.pkt.buf[i]); |
| nixnax | 9:0992486d4a30 | 106 | xx.printf(" C %02x %02x L=%d\n", ppp.pkt.crc&0xff, (ppp.pkt.crc>>8)&0xff, ppp.pkt.len); |
| nixnax | 9:0992486d4a30 | 107 | } |
| nixnax | 9:0992486d4a30 | 108 | |
| nixnax | 9:0992486d4a30 | 109 | void sendFrame(){ |
| nixnax | 9:0992486d4a30 | 110 | int crc = crcBuf(ppp.pkt.buf, ppp.pkt.len-2); // get crc |
| nixnax | 9:0992486d4a30 | 111 | ppp.pkt.buf[ ppp.pkt.len-2 ] = (~crc>>0); // fcs lo |
| nixnax | 9:0992486d4a30 | 112 | ppp.pkt.buf[ ppp.pkt.len-1 ] = (~crc>>8); // fcs hi |
| nixnax | 9:0992486d4a30 | 113 | pc.putc(0x7e); // frame flag |
| nixnax | 9:0992486d4a30 | 114 | for(int i=0;i<ppp.pkt.len;i++) { |
| nixnax | 9:0992486d4a30 | 115 | unsigned int cc = (unsigned int)ppp.pkt.buf[i]; |
| nixnax | 9:0992486d4a30 | 116 | if (cc>32) pc.putc(cc); else {pc.putc(0x7d); pc.putc(cc+32);} |
| nixnax | 9:0992486d4a30 | 117 | } |
| nixnax | 9:0992486d4a30 | 118 | pc.putc(0x7e); // frame flag |
| nixnax | 9:0992486d4a30 | 119 | } |
| nixnax | 9:0992486d4a30 | 120 | |
| nixnax | 9:0992486d4a30 | 121 | void ipRequestHandler(){ |
| nixnax | 9:0992486d4a30 | 122 | debug("IPCP Conf "); |
| nixnax | 9:0992486d4a30 | 123 | if ( ppp.pkt.buf[7] != 4 ) { |
| nixnax | 9:0992486d4a30 | 124 | debug("Rej\n"); // reject if any options are requested |
| nixnax | 9:0992486d4a30 | 125 | ppp.pkt.buf[4]=4; |
| nixnax | 9:0992486d4a30 | 126 | sendFrame(); |
| nixnax | 9:0992486d4a30 | 127 | } else { |
| nixnax | 9:0992486d4a30 | 128 | debug("Ack\n"); |
| nixnax | 9:0992486d4a30 | 129 | ppp.pkt.buf[4]=2; // ack the minimum |
| nixnax | 9:0992486d4a30 | 130 | sendFrame(); // acknowledge |
| nixnax | 9:0992486d4a30 | 131 | // send our own request now |
| nixnax | 9:0992486d4a30 | 132 | debug("IPCP Ask\n"); |
| nixnax | 9:0992486d4a30 | 133 | ppp.pkt.buf[4]=1; // request the minimum |
| nixnax | 9:0992486d4a30 | 134 | ppp.pkt.buf[5]++; // next sequence |
| nixnax | 9:0992486d4a30 | 135 | sendFrame(); // this is our request |
| nixnax | 9:0992486d4a30 | 136 | } |
| nixnax | 9:0992486d4a30 | 137 | } |
| nixnax | 9:0992486d4a30 | 138 | |
| nixnax | 9:0992486d4a30 | 139 | void ipAckHandler(){ debug("IPCP Grant\n"); } |
| nixnax | 9:0992486d4a30 | 140 | |
| nixnax | 9:0992486d4a30 | 141 | void ipNackHandler(){ debug("IPCP Nack\n"); } |
| nixnax | 9:0992486d4a30 | 142 | |
| nixnax | 9:0992486d4a30 | 143 | void ipDefaultHandler(){ debug("IPCP Other\n"); } |
| nixnax | 9:0992486d4a30 | 144 | |
| nixnax | 9:0992486d4a30 | 145 | void IPCPframe() { |
| nixnax | 9:0992486d4a30 | 146 | led1 = ppp.pkt.buf[5] & 1; // This is the sequence number so the led blinks on packets |
| nixnax | 9:0992486d4a30 | 147 | //ppp.pkt.id = ppp.pkt.buf[5]; // remember the sequence number |
| nixnax | 9:0992486d4a30 | 148 | int code = ppp.pkt.buf[4]; // packet type is here |
| nixnax | 9:0992486d4a30 | 149 | switch (code) { |
| nixnax | 9:0992486d4a30 | 150 | case 1: ipRequestHandler(); break; |
| nixnax | 9:0992486d4a30 | 151 | case 2: ipAckHandler(); break; |
| nixnax | 9:0992486d4a30 | 152 | case 3: ipNackHandler(); break; |
| nixnax | 9:0992486d4a30 | 153 | default: ipDefaultHandler(); |
| nixnax | 9:0992486d4a30 | 154 | } |
| nixnax | 9:0992486d4a30 | 155 | } |
| nixnax | 9:0992486d4a30 | 156 | |
| nixnax | 10:74f8233f72c0 | 157 | void UDPpacket() { |
| nixnax | 10:74f8233f72c0 | 158 | xx.printf("UDP %d.%d.%d.%d %d.%d.%d.%d\n", ppp.pkt.buf[16],ppp.pkt.buf[17],ppp.pkt.buf[18],ppp.pkt.buf[19],ppp.pkt.buf[20],ppp.pkt.buf[21],ppp.pkt.buf[22],ppp.pkt.buf[23] ); |
| nixnax | 10:74f8233f72c0 | 159 | int idx = 4+((ppp.pkt.buf[4]&0xf)*4); |
| nixnax | 10:74f8233f72c0 | 160 | int srcPort = (ppp.pkt.buf[idx+0]<<8)|ppp.pkt.buf[idx+1]; |
| nixnax | 10:74f8233f72c0 | 161 | int destPort = (ppp.pkt.buf[idx+2]<<8)|ppp.pkt.buf[idx+3]; |
| nixnax | 10:74f8233f72c0 | 162 | xx.printf("Src %04x Dest %04x\n", srcPort, destPort); |
| nixnax | 9:0992486d4a30 | 163 | } |
| nixnax | 9:0992486d4a30 | 164 | |
| nixnax | 10:74f8233f72c0 | 165 | void ICMPpacket() { |
| nixnax | 10:74f8233f72c0 | 166 | xx.printf("ICMP\n"); |
| nixnax | 10:74f8233f72c0 | 167 | /* |
| nixnax | 10:74f8233f72c0 | 168 | xx.printf("ICMP len %4d %d.%d.%d.%d %d.%d.%d.%d\n", (ppp.pkt.buf[6]<<8)+ppp.pkt.buf[7],ppp.pkt.buf[16],ppp.pkt.buf[17],ppp.pkt.buf[18],ppp.pkt.buf[19],ppp.pkt.buf[20],ppp.pkt.buf[21],ppp.pkt.buf[22],ppp.pkt.buf[23] ); |
| nixnax | 10:74f8233f72c0 | 169 | xx.printf("Byte0 = %02x\n", ppp.pkt.buf[4]); |
| nixnax | 10:74f8233f72c0 | 170 | xx.printf("Type %x Code %d\n", ppp.pkt.buf[28], ppp.pkt.buf[29]); |
| nixnax | 10:74f8233f72c0 | 171 | xx.printf("Number of records %d %d\n", ppp.pkt.buf[34],ppp.pkt.buf[35]); |
| nixnax | 10:74f8233f72c0 | 172 | xx.printf("Group %d.%d.%d.%d\n", ppp.pkt.buf[36],ppp.pkt.buf[37],ppp.pkt.buf[38],ppp.pkt.buf[39]); |
| nixnax | 10:74f8233f72c0 | 173 | */ |
| nixnax | 10:74f8233f72c0 | 174 | |
| nixnax | 10:74f8233f72c0 | 175 | } |
| nixnax | 10:74f8233f72c0 | 176 | |
| nixnax | 10:74f8233f72c0 | 177 | void IPframe() { |
| nixnax | 10:74f8233f72c0 | 178 | int protocol = ppp.pkt.buf[13]; |
| nixnax | 10:74f8233f72c0 | 179 | switch (protocol) { |
| nixnax | 10:74f8233f72c0 | 180 | case 2: ICMPpacket(); break; |
| nixnax | 10:74f8233f72c0 | 181 | case 17: UDPpacket(); break; |
| nixnax | 10:74f8233f72c0 | 182 | case 6: debug( "TCP \n" ); break; |
| nixnax | 10:74f8233f72c0 | 183 | default: debug( "Other \n"); |
| nixnax | 10:74f8233f72c0 | 184 | } |
| nixnax | 10:74f8233f72c0 | 185 | //xx.printf("IP frame proto %3d len %4d %d.%d.%d.%d %d.%d.%d.%d\n", ppp.pkt.buf[13],(ppp.pkt.buf[6]<<8)+ppp.pkt.buf[7],ppp.pkt.buf[16],ppp.pkt.buf[17],ppp.pkt.buf[18],ppp.pkt.buf[19],ppp.pkt.buf[20],ppp.pkt.buf[21],ppp.pkt.buf[22],ppp.pkt.buf[23] ); |
| nixnax | 10:74f8233f72c0 | 186 | } |
| nixnax | 9:0992486d4a30 | 187 | |
| nixnax | 9:0992486d4a30 | 188 | |
| nixnax | 9:0992486d4a30 | 189 | void LCPconfReq() { |
| nixnax | 9:0992486d4a30 | 190 | debug("LCP Conf "); |
| nixnax | 9:0992486d4a30 | 191 | if (ppp.pkt.buf[7] != 4) { |
| nixnax | 9:0992486d4a30 | 192 | ppp.pkt.buf[4]=4; // allow only minimal requests |
| nixnax | 9:0992486d4a30 | 193 | debug("Rej\n"); |
| nixnax | 9:0992486d4a30 | 194 | sendFrame(); |
| nixnax | 9:0992486d4a30 | 195 | } else { |
| nixnax | 9:0992486d4a30 | 196 | ppp.pkt.buf[4]=2; // ack zero conf |
| nixnax | 9:0992486d4a30 | 197 | debug("Ack\n"); |
| nixnax | 9:0992486d4a30 | 198 | sendFrame(); |
| nixnax | 10:74f8233f72c0 | 199 | debug("LCP Ask\n"); |
| nixnax | 9:0992486d4a30 | 200 | ppp.pkt.buf[4]=1; // request zero conf |
| nixnax | 9:0992486d4a30 | 201 | sendFrame(); |
| nixnax | 9:0992486d4a30 | 202 | } |
| nixnax | 9:0992486d4a30 | 203 | } |
| nixnax | 9:0992486d4a30 | 204 | |
| nixnax | 9:0992486d4a30 | 205 | void LCPconfAck() { |
| nixnax | 9:0992486d4a30 | 206 | debug("LCP Ack\n"); |
| nixnax | 9:0992486d4a30 | 207 | } |
| nixnax | 9:0992486d4a30 | 208 | |
| nixnax | 9:0992486d4a30 | 209 | void LCPend(){ |
| nixnax | 9:0992486d4a30 | 210 | debug("LCP End\n"); |
| nixnax | 9:0992486d4a30 | 211 | ppp.online=0; |
| nixnax | 9:0992486d4a30 | 212 | ppp.pkt.buf[4]=6; |
| nixnax | 9:0992486d4a30 | 213 | sendFrame(); |
| nixnax | 9:0992486d4a30 | 214 | } |
| nixnax | 9:0992486d4a30 | 215 | |
| nixnax | 9:0992486d4a30 | 216 | void LCPother(){ |
| nixnax | 9:0992486d4a30 | 217 | debug("LCP Other\n"); |
| nixnax | 9:0992486d4a30 | 218 | generalFrame(); |
| nixnax | 9:0992486d4a30 | 219 | } |
| nixnax | 9:0992486d4a30 | 220 | |
| nixnax | 9:0992486d4a30 | 221 | void LCPframe(){ |
| nixnax | 9:0992486d4a30 | 222 | int code = ppp.pkt.buf[4]; |
| nixnax | 9:0992486d4a30 | 223 | switch (code) { |
| nixnax | 9:0992486d4a30 | 224 | case 1: LCPconfReq(); break; |
| nixnax | 9:0992486d4a30 | 225 | case 2: LCPconfAck(); break; |
| nixnax | 9:0992486d4a30 | 226 | case 5: LCPend(); break; |
| nixnax | 9:0992486d4a30 | 227 | default: LCPother(); |
| nixnax | 9:0992486d4a30 | 228 | } |
| nixnax | 9:0992486d4a30 | 229 | } |
| nixnax | 9:0992486d4a30 | 230 | |
| nixnax | 9:0992486d4a30 | 231 | void xx21frame() { |
| nixnax | 9:0992486d4a30 | 232 | debug("Unknown frame type ff 03 xx 21\n"); |
| nixnax | 9:0992486d4a30 | 233 | } |
| nixnax | 9:0992486d4a30 | 234 | |
| nixnax | 9:0992486d4a30 | 235 | void determinePacketType() { |
| nixnax | 9:0992486d4a30 | 236 | if ( ppp.pkt.buf[0] != 0xff ) {debug("byte0 != ff\n"); return;} |
| nixnax | 9:0992486d4a30 | 237 | if ( ppp.pkt.buf[1] != 3 ) {debug("byte1 != 3\n"); return;} |
| nixnax | 9:0992486d4a30 | 238 | if ( ppp.pkt.buf[3] != 0x21 ) {debug("byte2 != 21\n"); return;} |
| nixnax | 9:0992486d4a30 | 239 | int packetType = ppp.pkt.buf[2]; |
| nixnax | 9:0992486d4a30 | 240 | switch (packetType) { |
| nixnax | 9:0992486d4a30 | 241 | case 0xc0: LCPframe(); break; |
| nixnax | 9:0992486d4a30 | 242 | case 0x80: IPCPframe(); break; |
| nixnax | 9:0992486d4a30 | 243 | case 0x00: IPframe(); break; |
| nixnax | 9:0992486d4a30 | 244 | default: xx21frame(); break; |
| nixnax | 9:0992486d4a30 | 245 | } |
| nixnax | 9:0992486d4a30 | 246 | } |
| nixnax | 9:0992486d4a30 | 247 | |
| nixnax | 9:0992486d4a30 | 248 | void scanForConnectString() { |
| nixnax | 9:0992486d4a30 | 249 | if ( ppp.online==0 ) { |
| nixnax | 9:0992486d4a30 | 250 | char * clientFound = strstr( rxbuf, "CLIENTCLIENT" ); // look for PC string |
| nixnax | 9:0992486d4a30 | 251 | if( clientFound ) { |
| nixnax | 9:0992486d4a30 | 252 | strcpy( clientFound, "FOUND!FOUND!" ); // overwrite so we don't get fixated |
| nixnax | 9:0992486d4a30 | 253 | pc.printf("CLIENTSERVER"); // respond to PC |
| nixnax | 9:0992486d4a30 | 254 | ppp.online=1; // we can stop looking for the string |
| nixnax | 9:0992486d4a30 | 255 | debug("Connect string found\n"); |
| nixnax | 9:0992486d4a30 | 256 | } |
| nixnax | 9:0992486d4a30 | 257 | } |
| nixnax | 9:0992486d4a30 | 258 | } |
| nixnax | 9:0992486d4a30 | 259 | |
| nixnax | 0:2cf4880c312a | 260 | int main() |
| nixnax | 0:2cf4880c312a | 261 | { |
| nixnax | 9:0992486d4a30 | 262 | pc.baud(9600); |
| nixnax | 4:a469050d5b80 | 263 | xx.baud(115200); |
| nixnax | 9:0992486d4a30 | 264 | xx.puts("\x1b[2J\x1b[HReady\n"); // VT100 code for clear screen & home |
| nixnax | 4:a469050d5b80 | 265 | |
| nixnax | 9:0992486d4a30 | 266 | pppInitStruct(); // initialize all the PPP properties |
| nixnax | 4:a469050d5b80 | 267 | |
| nixnax | 9:0992486d4a30 | 268 | pc.attach(&rxHandler,Serial::RxIrq); // start the receive handler |
| nixnax | 4:a469050d5b80 | 269 | |
| nixnax | 9:0992486d4a30 | 270 | int frameStartIndex, frameEndIndex; int frameBusy=0; |
| nixnax | 4:a469050d5b80 | 271 | |
| nixnax | 0:2cf4880c312a | 272 | while(1) { |
| nixnax | 9:0992486d4a30 | 273 | if ( ppp.online==0 ) scanForConnectString(); // try to connect |
| nixnax | 0:2cf4880c312a | 274 | while ( pc_readable() ) { |
| nixnax | 1:9e03798d4367 | 275 | int rx = pc_getBuf(); |
| nixnax | 9:0992486d4a30 | 276 | wait(0.001); |
| nixnax | 4:a469050d5b80 | 277 | if (frameBusy) { |
| nixnax | 4:a469050d5b80 | 278 | if (rx==FRAME_7E) { |
| nixnax | 4:a469050d5b80 | 279 | frameBusy=0; // done gathering frame |
| nixnax | 4:a469050d5b80 | 280 | frameEndIndex=ppp.rx.tail-1; // remember where frame ends |
| nixnax | 4:a469050d5b80 | 281 | void processFrame(int start, int end); // process a received frame |
| nixnax | 4:a469050d5b80 | 282 | processFrame(frameStartIndex, frameEndIndex); |
| nixnax | 4:a469050d5b80 | 283 | } |
| nixnax | 4:a469050d5b80 | 284 | } |
| nixnax | 4:a469050d5b80 | 285 | else { |
| nixnax | 4:a469050d5b80 | 286 | if (rx==FRAME_7E) { |
| nixnax | 4:a469050d5b80 | 287 | frameBusy=1; // start gathering frame |
| nixnax | 9:0992486d4a30 | 288 | frameStartIndex=ppp.rx.tail; // remember where frame started |
| nixnax | 4:a469050d5b80 | 289 | } |
| nixnax | 0:2cf4880c312a | 290 | } |
| nixnax | 4:a469050d5b80 | 291 | } |
| nixnax | 7:ab147f5e97ac | 292 | } |
| nixnax | 7:ab147f5e97ac | 293 | } |
 Nicolas Nackel
Nicolas Nackel