A Telegram BOT for this awesome all-in-one board.
Dependencies: BSP_B-L475E-IOT01 mbed es_wifi jsmn
Telegram Bot for DISCO_L475VG_IOT01
This application embeds aTelegram chatbot into the DISCO_L475VG_IOT01 board.
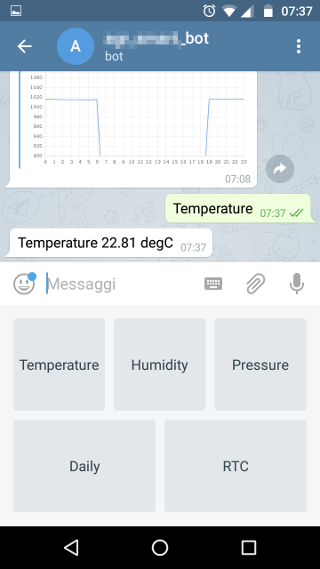
The Bot answers to the users queries about:
- Real time environmental data taken from the on board sensors.
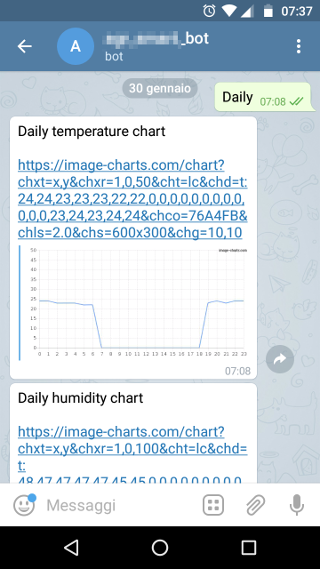
- Environmental data history of the latest 24 hours stored on board.
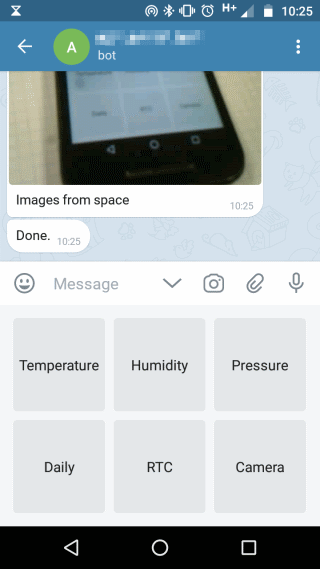
- Camera images taken from the Arducam-mini-2mp (optional).
This software uses:
- A modified version of the wifi library provided by ST in order to enable the TCP-SSL connection.
- An open source json parser jsmn (https://github.com/zserge/jsmn).
- A web service (http://now.http.org) to initialize the RTC.
- A web service (https://image-charts.com) to publish temperature,humidity and pressure charts.
- A modified version of the Arducam driver (https://os.mbed.com/users/dflet/)
Compilation
Import in your compiler and modify the following defines:
- WIFI_SSID
- WIFI_PASSWORD
- TELEGRAM_BOT_APIKEY
Please follow the Telegram bots documentation (https://core.telegram.org/bots) to better understand how the Telegram API works and how to create your bot.
In order to support the Arducam-Mini-2MP set WITH_ARDUCAM_2640 #define to 1.
Screenshots

Security
The Inventek wifi module creates the ssl connection but does not authenticate the server's certificate ( AT cmd P9=0 ).
For more details http://www.inventeksys.com/IWIN/programming-certificates-tcp-ssltls/
TCPConnector.h
- Committer:
- dvddnr
- Date:
- 2018-02-15
- Revision:
- 8:89fe332bc412
File content as of revision 8:89fe332bc412:
#pragma once
#include <mbed.h>
#include "es_wifi.h"
#define WIFI_WRITE_TIMEOUT 3000
#define WIFI_READ_TIMEOUT 25000
class TCPConnector
{
private:
ES_WIFIObject_t m_es_wifi_ctx;
public:
TCPConnector() {}
~TCPConnector(){}
bool wifi_connect(char *wifi_ssid, char* wifi_wpa_password, uint32_t max_attempts)
{
/* HW setup */
if (ES_WIFI_RegisterBusIO(&m_es_wifi_ctx,
SPI_WIFI_Init,
SPI_WIFI_DeInit,
SPI_WIFI_Delay,
SPI_WIFI_SendData,
SPI_WIFI_ReceiveData) != ES_WIFI_STATUS_OK)
return false;
if (ES_WIFI_Init(&m_es_wifi_ctx) != ES_WIFI_STATUS_OK)
return false;
ES_WIFI_ResetToFactoryDefault(&m_es_wifi_ctx);
/* JOIN AP */
for (int i = 0; i < max_attempts; i++)
{
if (ES_WIFI_Connect(&m_es_wifi_ctx, wifi_ssid, wifi_wpa_password, ES_WIFI_SEC_WPA_WPA2) == ES_WIFI_STATUS_OK)
{
return (ES_WIFI_GetNetworkSettings(&m_es_wifi_ctx) == ES_WIFI_STATUS_OK);
}
wait_ms(1000);
}
return false;
}
bool tcp_connect(uint8_t socket, char *domain_name, uint16_t remote_port, bool secure,uint32_t max_attempts)
{
ES_WIFI_Conn_t conn;
ES_WIFI_Status_t res;
conn.Number = socket;
conn.RemotePort = remote_port;
conn.LocalPort = 0;
conn.Type = (secure)?ES_WIFI_TCP_SSL_CONNECTION:ES_WIFI_TCP_CONNECTION;
strncpy((char *)conn.RemoteHost, domain_name, sizeof(conn.RemoteHost));
for(int i=0;i<max_attempts;i++)
{
res = ES_WIFI_ConnectToRemoteHost(&m_es_wifi_ctx, &conn);
if(res == ES_WIFI_STATUS_OK) return true;
}
return false;
}
bool tcp_close(uint32_t socket)
{
ES_WIFI_Conn_t conn;
conn.Number = socket;
return (ES_WIFI_StopClientConnection(&m_es_wifi_ctx, &conn)== ES_WIFI_STATUS_OK);
}
bool tcp_write(uint8_t socket, char *data, uint32_t data_len)
{
uint16_t ack;
uint16_t chunk_size;
ES_WIFI_Status_t res;
for(int i=0;i<data_len;i+=ES_WIFI_PAYLOAD_SIZE)
{
chunk_size = ((data_len-i)<ES_WIFI_PAYLOAD_SIZE)?(data_len-i):ES_WIFI_PAYLOAD_SIZE;
res = ES_WIFI_SendData(&m_es_wifi_ctx, socket, (uint8_t*)data+i, chunk_size, &ack, WIFI_WRITE_TIMEOUT);
if( res != ES_WIFI_STATUS_OK || chunk_size != ack ) return false;
}
return true;
}
bool tcp_read(uint8_t socket, char *rx_buffer, uint16_t rx_buffer_len, uint16_t *received_bytes,bool continued)
{
bool rx = false;
*received_bytes = 0;
rx = (continued)?( ES_WIFI_ReceiveData2(&m_es_wifi_ctx, (uint8_t*)rx_buffer, rx_buffer_len, received_bytes) == ES_WIFI_STATUS_OK ):
( ES_WIFI_ReceiveData(&m_es_wifi_ctx, socket, (uint8_t*)rx_buffer, rx_buffer_len, received_bytes, WIFI_READ_TIMEOUT) == ES_WIFI_STATUS_OK );
return rx;
}
};