Demonstration of Class-A LoRaWAN device using NAMote-72
Dependencies: LoRaWAN-lib mbed lib_mpl3115a2 lib_mma8451q lib_gps SX1272Lib
Dependents: LoRaWAN-NAMote72-BVS-confirmed-tester-0-7v1_copy
LoRaWAN-NAMote72 Application Demo is a Class-A device example project using LoRaWAN-lib and SX1272Lib libraries.
This project is compliant with LoRaWAN V1.0.1 specification.
Comissioning.h (LoRaWAN Network Configuration)
The end-device can be activated in one of the two ways:
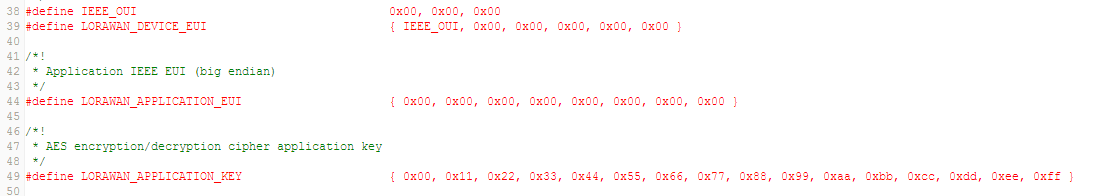
Over the Air (OTA) activation can be enabled as shown in the figure below.
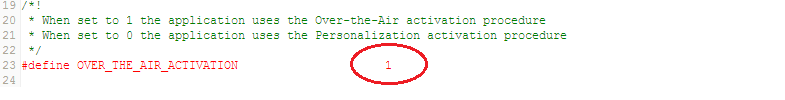
The end-device must be configured with the following parameters:
LORAWAN_DEVICE_EUI(8 Bytes) : Fist 3 Bytes is the Organizationally Unique Identifier (OUI) followed by 5 bytes of unique ID. If not defined by user, then the firmware automatically assigns one to the end-deviceLORAWAN_APPLICATION_EUI(8 Bytes)LORAWAN_APPLICATION_KEY(or DEVKEY) (16 Bytes)
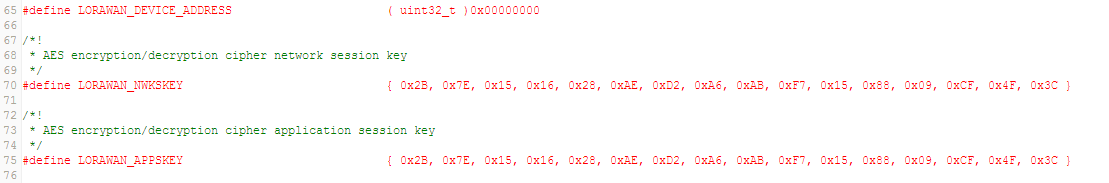
Activation by Personalization (ABP) can be enabled as shown in the figure below.
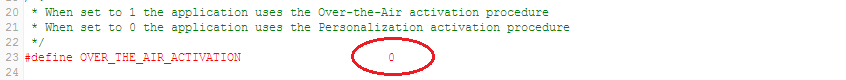
The end-device must be configured with the following parameters:
LORAWAN_DEVICE_ADDRESS(4 Bytes) : If not defined by user, then the firmware automatically assigns one to the end-deviceLORAWAN_NWKSKEY(16 Bytes)LORAWAN_APPSKEY(16 Bytes)
Config.h (LoRaWAN Communication Parameters)
- Mode of Operation : Hybrid
If the end-device needs to be configured to operate over 8-channels, then
Hybrid Modeneeds to be enabled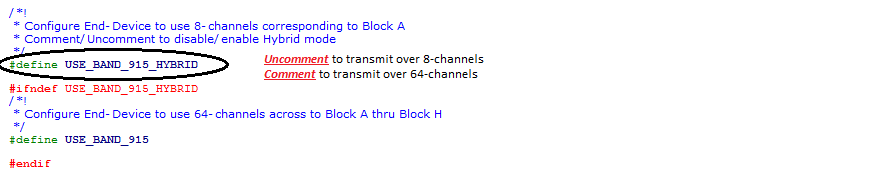
- Mode of Operation : Frequency Hop
If the end-device needs to be configured to operate over 64-channels, then
Hybrid Modeneeds to be disabled
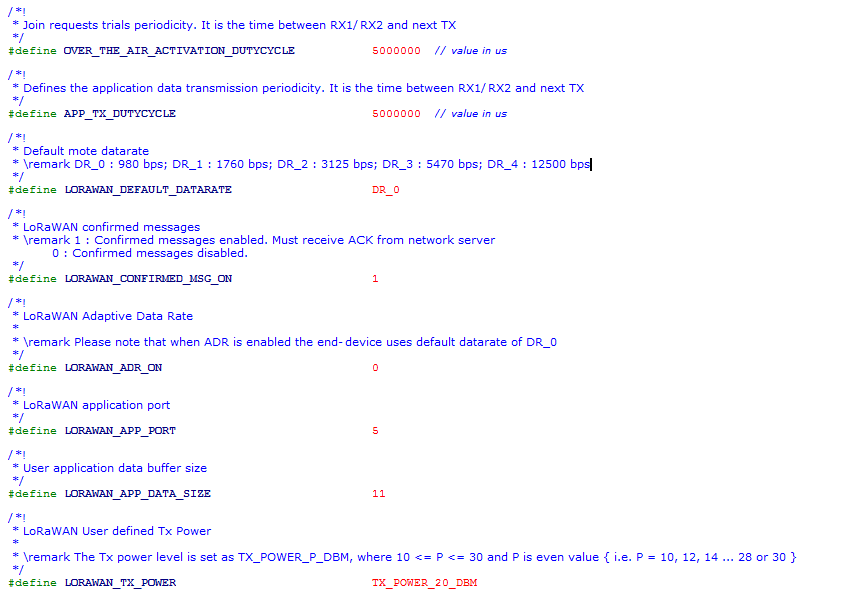
- Delay between successive JOIN REQUESTs :
The delay between successive Join Requests (until the end-device joins the network) can be configured using the parameter
OVER_THE_AIR_ACTIVATION_DUTYCYCLE
- Inter-Frame Delay :
One can change the delay between each frame transmission using
APP_TX_DUTYCYCLEIt is advisable thatAPP_TX_DUTYCYCLEis greater than or equal to 3sec.
- Data Rate :
The data rate can be configured as per LoRaWAN specification using the paramter
LORAWAN_DEFAULT_DATARATE. The range of values are DR_0, DR_1, DR_2, DR_3 and DR_4
- Confirmed/Unconfirmed Messages :
The uplink message or payload can be chosen to be confirmed or unconfirmed using the parameter
LORAWAN_CONFIRMED_MSG_ON. When set to 1, the transmitted messages need to be confirmed with anACKby the network server in the subsequent RX window. When set to 0, noACKis requested.
- ADR ON/OFF :
The ADR can be enabled or disabled using the parameter
LORAWAN_ADR_ON. When set to 1, ADR is enabled and disabled when set to 0.
- Application Port :
The application port can be set using parameter
LORAWAN_APP_PORT.
- Payload Length :
The lenght of the payload (in bytes) to be transmitted can be configured using
LORAWAN_APP_DATA_SIZE
- Transmit Power :
The transmit power can be configured using
LORAWAN_TX_POWER(LoRaMAC verifies if the set power is compliant with the LoRaWAN spec and FCC guidelines)
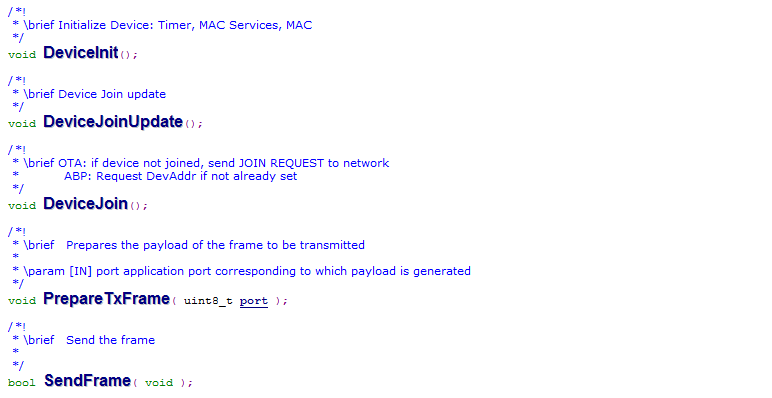
Main.cpp (Device State Machine)
The end-device state machine is defined.
- Initial State : Device is initialized.
- Join State : For OTA, Join Request is transmitted to the network until Join Accept is received by the end-device. Join event function is called that sets Red LED ON.
- Send State : Transmit payload frame is prepared. Tx event is called that blinks the Red LED indicating uplink transmission.
- Cycle State : Next packet transmission is scheduled
LoRaEventProc.cpp (Events and On-board Application)
Define events during Join, Tx & Rx. Prepare TX packet by appending with appropriate application data.
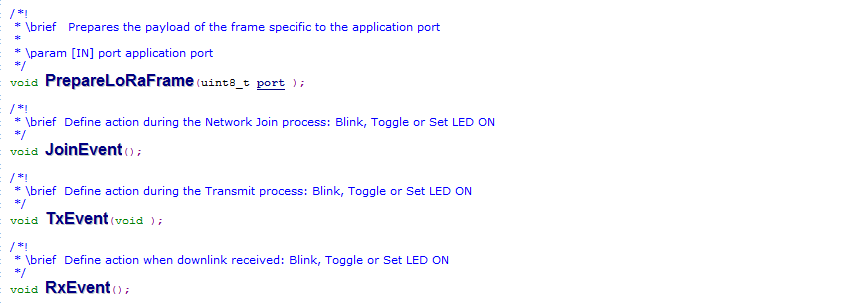
- PrepareLoRaFrame(uint8_t port ) :
Prepare LoRa payload frame with on-board application data such as GPS, Temperature, Battery, etc. LoRa.ApplicationCall(AppType ) calls application AppType defined in
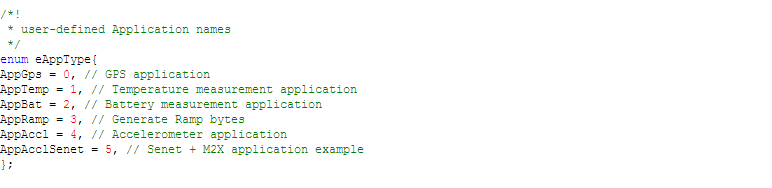
LoRaApp.cpp. AppType is defined inLoRaApp.h
LoRaApp.cpp
User-defined applications such as GPS, Temp, Accelerometer, LED indications etc. Event based actions such as LED blink on Tx, LED toggle on downlink etc
LoRaDeviceStateProc.cpp
Process function calls corresponding to different Device states
LoRaMacLayerService.cpp
Define MAC Layer Services: MLME & MCPS
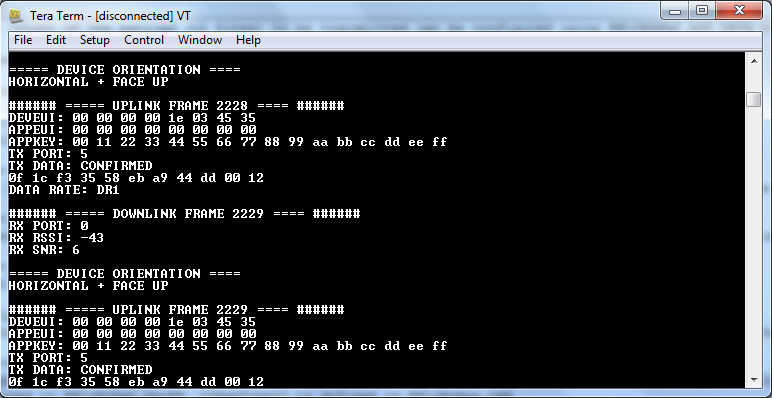
Serial Terminal Display
By using a serial port connection using applications such as teraterm or putty, one can view the status of the End-Device. Once the End-Device Joins the network, transmission parameters such as payload data, application port, message type etc. are displayed on the terminal.
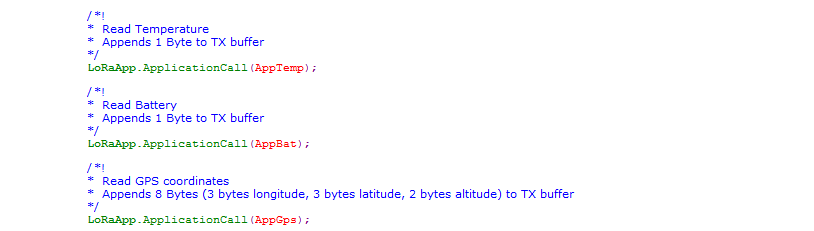
Default Application Payload
This application defaults to sending uplink data to logical port 5. The application payload consists of:
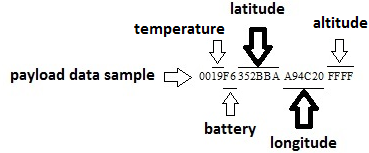
Sample Application Payload Calculation for Longitude/Latitude
Payload => 00 19 F6 352BBA A94C20 FFFF
Temperature Calculation
19H => 2510
Temp = 25/2 = 12.5 oC
Battery Level
FFH => 100 %
F6H => 96.5 %
Longitude Calculation
longitude = A94C20H => 1109507210
longitudinal coordinate = -360 + (longitude10 x 180/(223))
longitudinal coordinate = -121.93
Latitude Calculation
latitude = 352BBAH = 348460210
latitude coordinate = (latitude10 x 90/(223-1))
latitude coordinate = 37.39
system/crypto/aes.h@0:69f2e28d12c1, 2016-05-17 (annotated)
- Committer:
- ubhat
- Date:
- Tue May 17 00:21:55 2016 +0000
- Revision:
- 0:69f2e28d12c1
Project for LoRa Bootcamp
Who changed what in which revision?
| User | Revision | Line number | New contents of line |
|---|---|---|---|
| ubhat | 0:69f2e28d12c1 | 1 | /* |
| ubhat | 0:69f2e28d12c1 | 2 | --------------------------------------------------------------------------- |
| ubhat | 0:69f2e28d12c1 | 3 | Copyright (c) 1998-2008, Brian Gladman, Worcester, UK. All rights reserved. |
| ubhat | 0:69f2e28d12c1 | 4 | |
| ubhat | 0:69f2e28d12c1 | 5 | LICENSE TERMS |
| ubhat | 0:69f2e28d12c1 | 6 | |
| ubhat | 0:69f2e28d12c1 | 7 | The redistribution and use of this software (with or without changes) |
| ubhat | 0:69f2e28d12c1 | 8 | is allowed without the payment of fees or royalties provided that: |
| ubhat | 0:69f2e28d12c1 | 9 | |
| ubhat | 0:69f2e28d12c1 | 10 | 1. source code distributions include the above copyright notice, this |
| ubhat | 0:69f2e28d12c1 | 11 | list of conditions and the following disclaimer; |
| ubhat | 0:69f2e28d12c1 | 12 | |
| ubhat | 0:69f2e28d12c1 | 13 | 2. binary distributions include the above copyright notice, this list |
| ubhat | 0:69f2e28d12c1 | 14 | of conditions and the following disclaimer in their documentation; |
| ubhat | 0:69f2e28d12c1 | 15 | |
| ubhat | 0:69f2e28d12c1 | 16 | 3. the name of the copyright holder is not used to endorse products |
| ubhat | 0:69f2e28d12c1 | 17 | built using this software without specific written permission. |
| ubhat | 0:69f2e28d12c1 | 18 | |
| ubhat | 0:69f2e28d12c1 | 19 | DISCLAIMER |
| ubhat | 0:69f2e28d12c1 | 20 | |
| ubhat | 0:69f2e28d12c1 | 21 | This software is provided 'as is' with no explicit or implied warranties |
| ubhat | 0:69f2e28d12c1 | 22 | in respect of its properties, including, but not limited to, correctness |
| ubhat | 0:69f2e28d12c1 | 23 | and/or fitness for purpose. |
| ubhat | 0:69f2e28d12c1 | 24 | --------------------------------------------------------------------------- |
| ubhat | 0:69f2e28d12c1 | 25 | Issue 09/09/2006 |
| ubhat | 0:69f2e28d12c1 | 26 | |
| ubhat | 0:69f2e28d12c1 | 27 | This is an AES implementation that uses only 8-bit byte operations on the |
| ubhat | 0:69f2e28d12c1 | 28 | cipher state. |
| ubhat | 0:69f2e28d12c1 | 29 | */ |
| ubhat | 0:69f2e28d12c1 | 30 | |
| ubhat | 0:69f2e28d12c1 | 31 | #ifndef AES_H |
| ubhat | 0:69f2e28d12c1 | 32 | #define AES_H |
| ubhat | 0:69f2e28d12c1 | 33 | |
| ubhat | 0:69f2e28d12c1 | 34 | #if 1 |
| ubhat | 0:69f2e28d12c1 | 35 | # define AES_ENC_PREKEYED /* AES encryption with a precomputed key schedule */ |
| ubhat | 0:69f2e28d12c1 | 36 | #endif |
| ubhat | 0:69f2e28d12c1 | 37 | #if 0 |
| ubhat | 0:69f2e28d12c1 | 38 | # define AES_DEC_PREKEYED /* AES decryption with a precomputed key schedule */ |
| ubhat | 0:69f2e28d12c1 | 39 | #endif |
| ubhat | 0:69f2e28d12c1 | 40 | #if 0 |
| ubhat | 0:69f2e28d12c1 | 41 | # define AES_ENC_128_OTFK /* AES encryption with 'on the fly' 128 bit keying */ |
| ubhat | 0:69f2e28d12c1 | 42 | #endif |
| ubhat | 0:69f2e28d12c1 | 43 | #if 0 |
| ubhat | 0:69f2e28d12c1 | 44 | # define AES_DEC_128_OTFK /* AES decryption with 'on the fly' 128 bit keying */ |
| ubhat | 0:69f2e28d12c1 | 45 | #endif |
| ubhat | 0:69f2e28d12c1 | 46 | #if 0 |
| ubhat | 0:69f2e28d12c1 | 47 | # define AES_ENC_256_OTFK /* AES encryption with 'on the fly' 256 bit keying */ |
| ubhat | 0:69f2e28d12c1 | 48 | #endif |
| ubhat | 0:69f2e28d12c1 | 49 | #if 0 |
| ubhat | 0:69f2e28d12c1 | 50 | # define AES_DEC_256_OTFK /* AES decryption with 'on the fly' 256 bit keying */ |
| ubhat | 0:69f2e28d12c1 | 51 | #endif |
| ubhat | 0:69f2e28d12c1 | 52 | |
| ubhat | 0:69f2e28d12c1 | 53 | #define N_ROW 4 |
| ubhat | 0:69f2e28d12c1 | 54 | #define N_COL 4 |
| ubhat | 0:69f2e28d12c1 | 55 | #define N_BLOCK (N_ROW * N_COL) |
| ubhat | 0:69f2e28d12c1 | 56 | #define N_MAX_ROUNDS 14 |
| ubhat | 0:69f2e28d12c1 | 57 | |
| ubhat | 0:69f2e28d12c1 | 58 | typedef uint8_t return_type; |
| ubhat | 0:69f2e28d12c1 | 59 | |
| ubhat | 0:69f2e28d12c1 | 60 | /* Warning: The key length for 256 bit keys overflows a byte |
| ubhat | 0:69f2e28d12c1 | 61 | (see comment below) |
| ubhat | 0:69f2e28d12c1 | 62 | */ |
| ubhat | 0:69f2e28d12c1 | 63 | |
| ubhat | 0:69f2e28d12c1 | 64 | typedef uint8_t length_type; |
| ubhat | 0:69f2e28d12c1 | 65 | |
| ubhat | 0:69f2e28d12c1 | 66 | typedef struct |
| ubhat | 0:69f2e28d12c1 | 67 | { uint8_t ksch[(N_MAX_ROUNDS + 1) * N_BLOCK]; |
| ubhat | 0:69f2e28d12c1 | 68 | uint8_t rnd; |
| ubhat | 0:69f2e28d12c1 | 69 | } aes_context; |
| ubhat | 0:69f2e28d12c1 | 70 | |
| ubhat | 0:69f2e28d12c1 | 71 | /* The following calls are for a precomputed key schedule |
| ubhat | 0:69f2e28d12c1 | 72 | |
| ubhat | 0:69f2e28d12c1 | 73 | NOTE: If the length_type used for the key length is an |
| ubhat | 0:69f2e28d12c1 | 74 | unsigned 8-bit character, a key length of 256 bits must |
| ubhat | 0:69f2e28d12c1 | 75 | be entered as a length in bytes (valid inputs are hence |
| ubhat | 0:69f2e28d12c1 | 76 | 128, 192, 16, 24 and 32). |
| ubhat | 0:69f2e28d12c1 | 77 | */ |
| ubhat | 0:69f2e28d12c1 | 78 | |
| ubhat | 0:69f2e28d12c1 | 79 | #if defined( AES_ENC_PREKEYED ) || defined( AES_DEC_PREKEYED ) |
| ubhat | 0:69f2e28d12c1 | 80 | |
| ubhat | 0:69f2e28d12c1 | 81 | return_type aes_set_key( const uint8_t key[], |
| ubhat | 0:69f2e28d12c1 | 82 | length_type keylen, |
| ubhat | 0:69f2e28d12c1 | 83 | aes_context ctx[1] ); |
| ubhat | 0:69f2e28d12c1 | 84 | #endif |
| ubhat | 0:69f2e28d12c1 | 85 | |
| ubhat | 0:69f2e28d12c1 | 86 | #if defined( AES_ENC_PREKEYED ) |
| ubhat | 0:69f2e28d12c1 | 87 | |
| ubhat | 0:69f2e28d12c1 | 88 | return_type aes_encrypt( const uint8_t in[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 89 | uint8_t out[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 90 | const aes_context ctx[1] ); |
| ubhat | 0:69f2e28d12c1 | 91 | |
| ubhat | 0:69f2e28d12c1 | 92 | return_type aes_cbc_encrypt( const uint8_t *in, |
| ubhat | 0:69f2e28d12c1 | 93 | uint8_t *out, |
| ubhat | 0:69f2e28d12c1 | 94 | int32_t n_block, |
| ubhat | 0:69f2e28d12c1 | 95 | uint8_t iv[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 96 | const aes_context ctx[1] ); |
| ubhat | 0:69f2e28d12c1 | 97 | #endif |
| ubhat | 0:69f2e28d12c1 | 98 | |
| ubhat | 0:69f2e28d12c1 | 99 | #if defined( AES_DEC_PREKEYED ) |
| ubhat | 0:69f2e28d12c1 | 100 | |
| ubhat | 0:69f2e28d12c1 | 101 | return_type aes_decrypt( const uint8_t in[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 102 | uint8_t out[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 103 | const aes_context ctx[1] ); |
| ubhat | 0:69f2e28d12c1 | 104 | |
| ubhat | 0:69f2e28d12c1 | 105 | return_type aes_cbc_decrypt( const uint8_t *in, |
| ubhat | 0:69f2e28d12c1 | 106 | uint8_t *out, |
| ubhat | 0:69f2e28d12c1 | 107 | int32_t n_block, |
| ubhat | 0:69f2e28d12c1 | 108 | uint8_t iv[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 109 | const aes_context ctx[1] ); |
| ubhat | 0:69f2e28d12c1 | 110 | #endif |
| ubhat | 0:69f2e28d12c1 | 111 | |
| ubhat | 0:69f2e28d12c1 | 112 | /* The following calls are for 'on the fly' keying. In this case the |
| ubhat | 0:69f2e28d12c1 | 113 | encryption and decryption keys are different. |
| ubhat | 0:69f2e28d12c1 | 114 | |
| ubhat | 0:69f2e28d12c1 | 115 | The encryption subroutines take a key in an array of bytes in |
| ubhat | 0:69f2e28d12c1 | 116 | key[L] where L is 16, 24 or 32 bytes for key lengths of 128, |
| ubhat | 0:69f2e28d12c1 | 117 | 192, and 256 bits respectively. They then encrypts the input |
| ubhat | 0:69f2e28d12c1 | 118 | data, in[] with this key and put the reult in the output array |
| ubhat | 0:69f2e28d12c1 | 119 | out[]. In addition, the second key array, o_key[L], is used |
| ubhat | 0:69f2e28d12c1 | 120 | to output the key that is needed by the decryption subroutine |
| ubhat | 0:69f2e28d12c1 | 121 | to reverse the encryption operation. The two key arrays can |
| ubhat | 0:69f2e28d12c1 | 122 | be the same array but in this case the original key will be |
| ubhat | 0:69f2e28d12c1 | 123 | overwritten. |
| ubhat | 0:69f2e28d12c1 | 124 | |
| ubhat | 0:69f2e28d12c1 | 125 | In the same way, the decryption subroutines output keys that |
| ubhat | 0:69f2e28d12c1 | 126 | can be used to reverse their effect when used for encryption. |
| ubhat | 0:69f2e28d12c1 | 127 | |
| ubhat | 0:69f2e28d12c1 | 128 | Only 128 and 256 bit keys are supported in these 'on the fly' |
| ubhat | 0:69f2e28d12c1 | 129 | modes. |
| ubhat | 0:69f2e28d12c1 | 130 | */ |
| ubhat | 0:69f2e28d12c1 | 131 | |
| ubhat | 0:69f2e28d12c1 | 132 | #if defined( AES_ENC_128_OTFK ) |
| ubhat | 0:69f2e28d12c1 | 133 | void aes_encrypt_128( const uint8_t in[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 134 | uint8_t out[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 135 | const uint8_t key[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 136 | uint8_t o_key[N_BLOCK] ); |
| ubhat | 0:69f2e28d12c1 | 137 | #endif |
| ubhat | 0:69f2e28d12c1 | 138 | |
| ubhat | 0:69f2e28d12c1 | 139 | #if defined( AES_DEC_128_OTFK ) |
| ubhat | 0:69f2e28d12c1 | 140 | void aes_decrypt_128( const uint8_t in[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 141 | uint8_t out[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 142 | const uint8_t key[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 143 | uint8_t o_key[N_BLOCK] ); |
| ubhat | 0:69f2e28d12c1 | 144 | #endif |
| ubhat | 0:69f2e28d12c1 | 145 | |
| ubhat | 0:69f2e28d12c1 | 146 | #if defined( AES_ENC_256_OTFK ) |
| ubhat | 0:69f2e28d12c1 | 147 | void aes_encrypt_256( const uint8_t in[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 148 | uint8_t out[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 149 | const uint8_t key[2 * N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 150 | uint8_t o_key[2 * N_BLOCK] ); |
| ubhat | 0:69f2e28d12c1 | 151 | #endif |
| ubhat | 0:69f2e28d12c1 | 152 | |
| ubhat | 0:69f2e28d12c1 | 153 | #if defined( AES_DEC_256_OTFK ) |
| ubhat | 0:69f2e28d12c1 | 154 | void aes_decrypt_256( const uint8_t in[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 155 | uint8_t out[N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 156 | const uint8_t key[2 * N_BLOCK], |
| ubhat | 0:69f2e28d12c1 | 157 | uint8_t o_key[2 * N_BLOCK] ); |
| ubhat | 0:69f2e28d12c1 | 158 | #endif |
| ubhat | 0:69f2e28d12c1 | 159 | |
| ubhat | 0:69f2e28d12c1 | 160 | #endif |