Small Internet Protocol Stack using a standard serial port.
PPP-Blinky - TCP/IP Networking Over a Serial Port
Note: The source code is at the bottom of this page.
A Windows desktop showing PPP-Blinky in the network connections list.
Describe PPP-Blinky in Three Sentences
PPP-Blinky is a tiny library that enables Internet protocols (IPv4) to any mbed target hardware by using only a serial port.
The code runs on processors with as little as 8k RAM, for example the Nucleo-L053R8 board.
PPP-Blinky uses the industry-standard PPP (Point-to-Point) Protocol and a tiny "stateless" TCP/IP stack.
No Ethernet Port Required
No ethernet port is required - PPP-Blinky uses a serial port to send IP packets to your PC.
PPP-Blinky emulates a standard dial-up modem and therefore connects to Windows, Linux or Adroid machines.
The code runs on most ARM mbed platforms such as the LPC11U24 shown in the picture below:
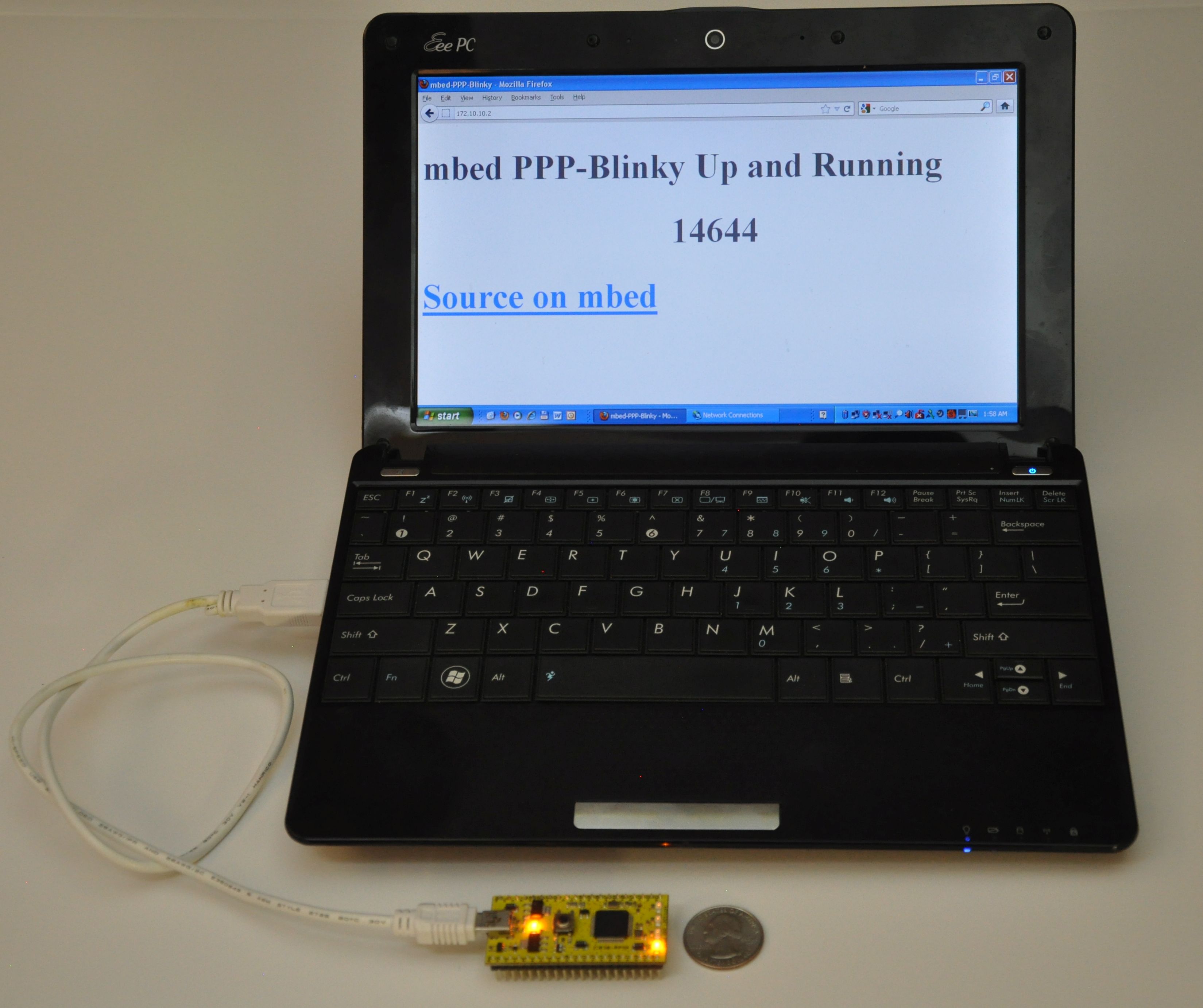 mbed LPC11u24 acting as a webserver to a Windows laptop.
mbed LPC11u24 acting as a webserver to a Windows laptop.
Webserver
The Webserver and WebSocket functions are ideal for building browser-based GUIs on mbed-enabled hardware.
PPP-Blinky's HTTP webserver works with most web clients such as Internet Explorer, Mozilla Firefox, Google Chrome, Safari, Curl, wget and Lynx as well as Microsoft Powershell Invoke-Webrequest command.
In the image below Firefox web browser displays the main web page embedded into PPP-Blinky's code:
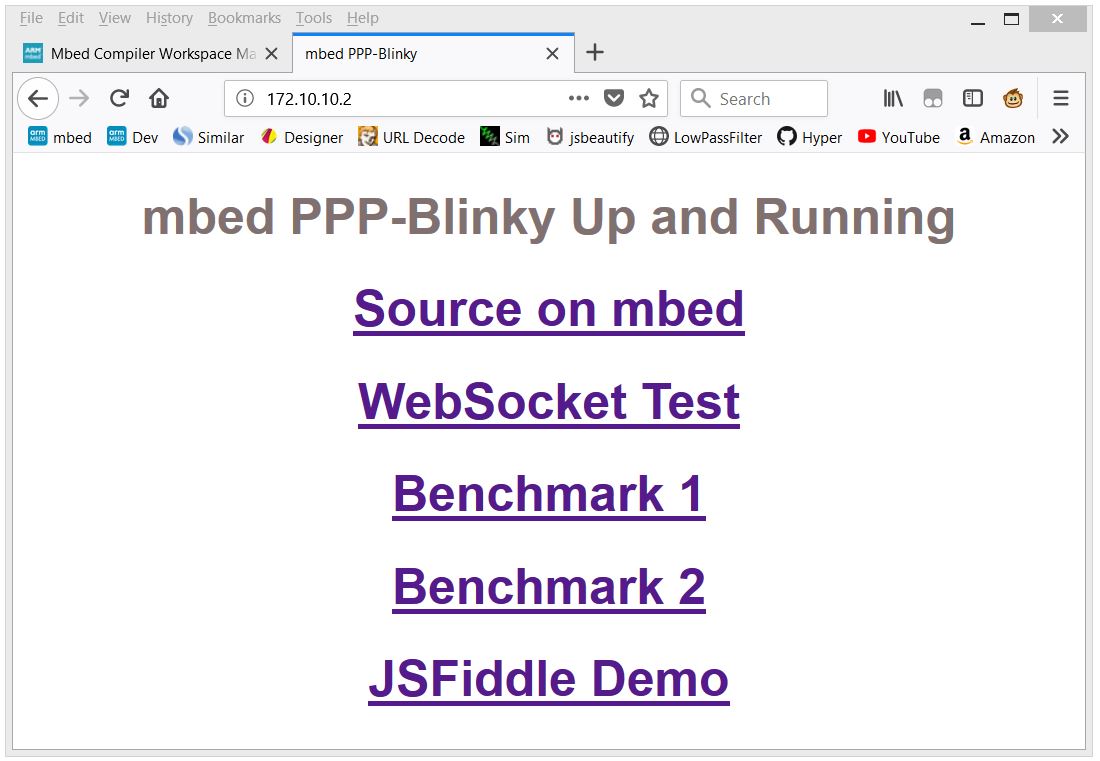 Firefox web browser displays a web page embedded into PPP-Blinky's code
Firefox web browser displays a web page embedded into PPP-Blinky's code
WebSocket Service
WebSocket is the most popular protocol standard for real-time bidirectional TCP/IP communication between clients and servers.
In the image below a small Internet Explorer script has connected to PPP-Blinky's WebSocket Service.
A websocket message was then sent by the browser and was echoed back by the WebSocket, triggering the onmessage event in the script.
The WebSocket service enables bidirectional real-time interaction between PPP-Blinky and any element in the browser DOM via JavaScript.
If you already have PPP-Blinky up and running you can test your WebSocket service using this: http://jsfiddle.net/d26cyuh2/112/embedded/result
Websockets are ideal for building browser-based GUIs for mbed hardware.
Trying PPP-Blinky on your mbed board
You will need an mbed-enabled hardware board: https://developer.mbed.org/platforms/
Establish a serial port connection between your host PC and your mbed board.
The easiest way is to use mbed hardware with a USB serial debug port. I've tried the ST-Micro Nucleo-L476RG, Nucleo-L152RE, Nucleo-F401RE, Nucleo-L432KC, Nucleo-L053R8, mbed-LPC11U24 and mbed-LPC1768 boards and they all work out of the box. Use the mbed online compiler to compile the software for your target board. Save the compiled binary to your hardware.
Before establishing a network connection, you can verify the operation of the code by opening a terminal program such as Tera Term, and setting the baud rate of the COM port on your mbed board to 115200 baud. LED1 should toggle for every two 0x7E (~) (i.e. tilde) characters you type, as 0x7E is the PPP frame start/end marker. Don't forget to close the port when your'e done testing, or else Windows Dial-up Networking will report that the COM port is in use by another program when you try to connect.
Once you are certain that the serial port and firmware is working, proceed to creating a new network connection on your PC -see below.
Creating a Dial-up Connection in Windows
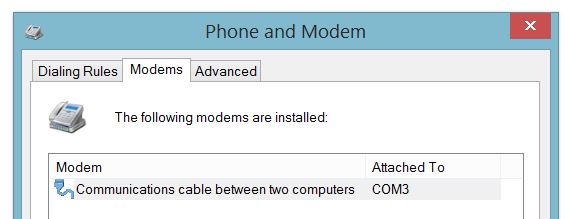
Setting up Dial-Up Networking (DUN) on your Windows 7 or 8 PC is essentially a two-step process: First, you create a new modem device, because PPP-blinky partially emulates a standard Windows serial port modem device. Second, you create a new Internet connection (in practice, a new network adapter) which is associated with your new "modem".
Step-by-step description of how to configure Windows for PPP-Blinky here:
/users/nixnax/code/PPP-Blinky/wiki/Configuring-Windows-Dial-Up-Networking
There is also a screen on how to set up Linux dial-up networking near the bottom of this page.
Connecting to PPP-Blinky from your PC
Once Windows networking is configured you can establish a dial-up connection to your mbed board over the USB virtual com port.
The IP address you manually assigned to the new dial-up network adapter (172.10.10.1) functions as a gateway to any valid IP address on that subnet. In the screen capture below, I'm sending pings from the Windows 8 command line to my ST-Micro Nucleo-L476RG board over the USB virtual serial Port. I'm also using a second serial port and Tera Term to capture the debug output from a second serial port on the hardware. The optional debug output from the board prints out the IP source and destination address and the first few bytes of the data payload. Note that the source is the adapter IP address, (172.10.10.1 in this case) and the destination is some other address on that subnet - all packets to the subnet are sent to our mbed hardware. For example, you could also ping 172.10.10.123 or, if your PPP-Blinky is running, simply click on this link: http://172.10.10.123
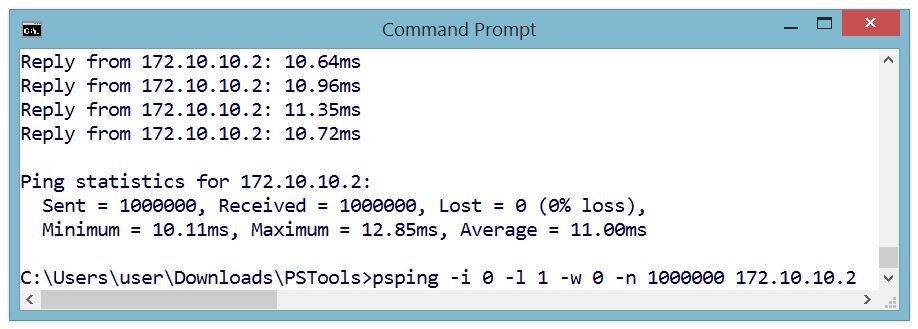
One Million Pings!
In the image below the ICMP ("ping") echo reply service was tested by sending one million pings to ppp-Blinky. This took over two hours.
The ping tool used on the Windows 8 PC was psping.exe from PsTools by Mark Russinovich - http://bit.ly/PingFast
The average reply time for a short ping (1 byte of payload data) was 11 milliseconds at 115200 baud on the $10 Nucleo-L053R8 board - barely enough time for 130 bytes to be sent over the port!
Monitoring PPP-Blinky Packets
The image below is from a Microsoft Network Monitor 3.4 capture session.
Responses from PPP-Blinky are shown in blue.
Frame 2 - Internet Explorer at IP 172.10.10.1 (the Dial-Up Adapter IP) requests a TCP connection by sending an S (SYN) flag.
Frame 3 - PPP-Blinky at IP 172.10.10.2 responds with an ACK in frame 3. One direction of the link is now established.
Frame 4 - The PC acknowledges the SYN sent by PPP-Blinky in frame 3. The TCP link is now fully established.
Frame 5 - The browser "pushes" (P flag is set) an HTTP GET request to PPP-Blinky.
Frame 6 - PPP-Blinky responds with a standard HTTP response "pushes" (P flag set) back a small web page. It also sets the A (ACK) flag to acknowledge the message sent in frame 6.
Frame 7 - The PC acknowledges reception of the HTTP payload.
Frame 8 - The PC starts to shut down the TCP connection by sending a FIN flag.
Frame 9 - PPP-Blinky acknowledges the FIN request - the connection is now closed in one direction. It also sets a FIN flag in the response to request closure of the opposite direction of the connection.
Frame 10 - The PC acknowledges the FIN request. The closing of the TCP connection is now confirmed in both directions.
Debug Output
PPP-Blinky can output handy debug information to an optional second serial port.
The image below shows the debug output (Ident, Source, Destination, TCP Flags) for a complete HTTP conversation.
The PC messages are displayed in black. PPP-Blinky messages are blue.
Notice how PPP-blinky automatically inserts a blank line after each full HTTP conversation.
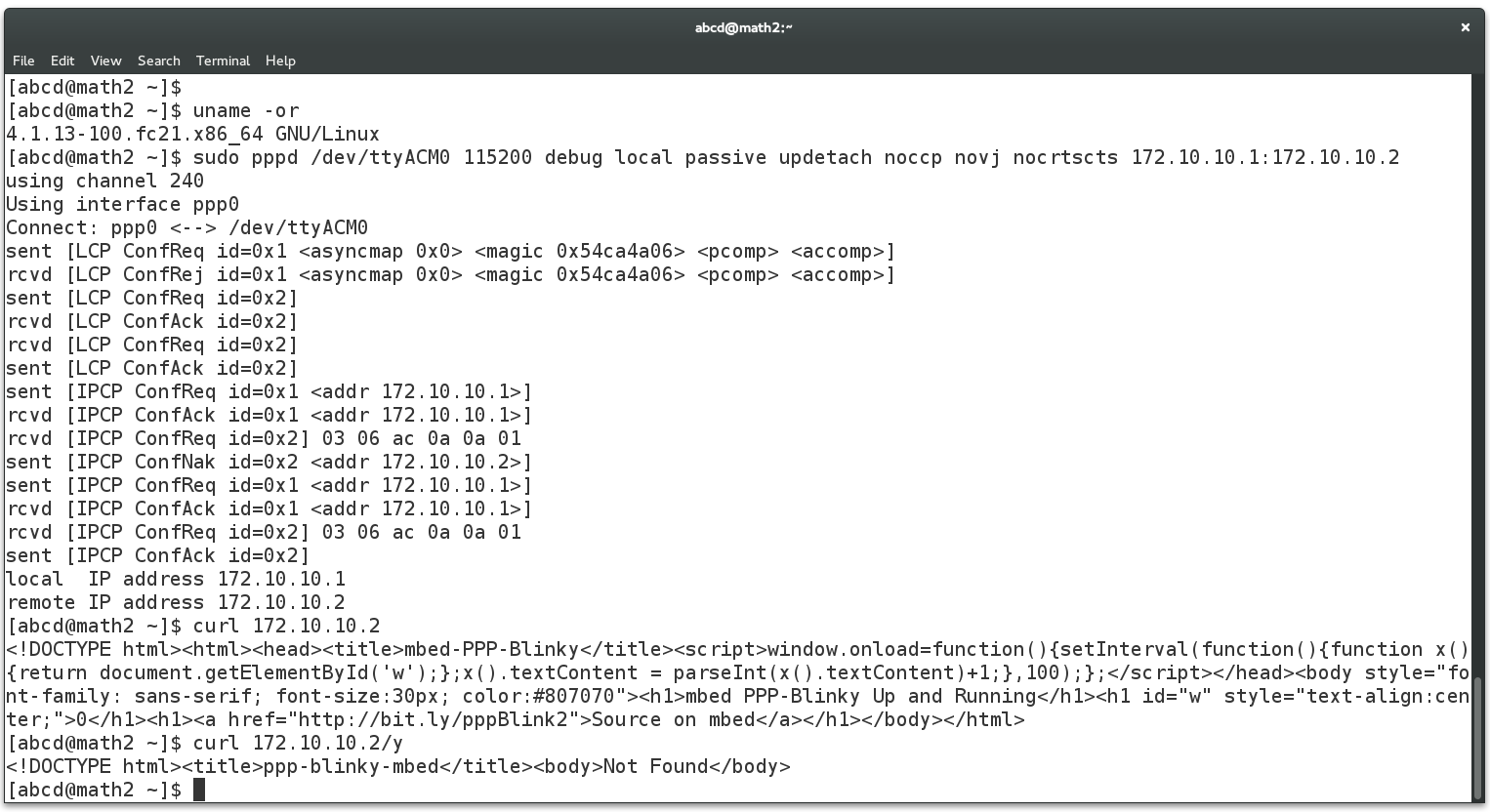
Creating a Dial-Up Connection in Linux
The screen below shows the required pppd command to connect to PPP-Blinky from a Linux machine. This was much simpler than Windows! The USB serial port of the mbed LPC1768 board registered as /dev/ttyACM0 on my Linux box. Do a websearch on pppd if you want to learn more about pppd, the Linux PPP handler. Near the bottom of the screen below, two webpages are fetched (/ and /y) by using the curl command on the command line. Gnome Webkit and Firefox work fine, too. Also try echo GET / HTTP/1.1 | nc 172.10.10.2 which uses netcat, the "Swiss army knife" of networking tools. PPP-Blinky was also tested with ApacheBench, the Apache server benchmark software. After 100000 fetches, the mean page fetch rate was reported as 6 page fetches per second for a small page.
Caveats
PPP Blinky is an extremely sparse implementation (1.5k lines) of HTTP,WebSocket,TCP, UDP, ICMP, IPCP and LCP over PPP, requiring around 8kB of RAM. The minimum functionality required to establish connectivity is implemented. These are often acceptable tradeoffs for embedded projects as well as a handy tool to learn the practical details of everyday networking implementations.
PPP-Blinky/ppp-blinky.cpp@149:969d98f6fb88, 2017-08-30 (annotated)
- Committer:
- nixnax
- Date:
- Wed Aug 30 16:13:34 2017 +0000
- Revision:
- 149:969d98f6fb88
- Parent:
- 148:4225c3608b80
- Child:
- 150:3366bf3d294e
Added swapIpPorts()
Who changed what in which revision?
| User | Revision | Line number | New contents of line |
|---|---|---|---|
| nixnax | 142:54d1543e23e5 | 1 | // PPP-Blinky - "The Most Basic Internet Of a Thing" |
| nixnax | 142:54d1543e23e5 | 2 | // A Tiny HTTP Webserver Using Windows XP/7/8/10/Linux Dial-Up Networking Over A Serial Port. |
| nixnax | 142:54d1543e23e5 | 3 | // Receives UDP packets and responds to ping (ICMP Echo requests) |
| nixnax | 142:54d1543e23e5 | 4 | // WebSocket Service - see https://en.wikipedia.org/wiki/WebSocket |
| nixnax | 142:54d1543e23e5 | 5 | |
| nixnax | 142:54d1543e23e5 | 6 | // Copyright 2016/2017 Nicolas Nackel aka Nixnax. Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions: The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software. THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE. |
| nixnax | 142:54d1543e23e5 | 7 | |
| nixnax | 142:54d1543e23e5 | 8 | // Notes and Instructions |
| nixnax | 142:54d1543e23e5 | 9 | // http://bit.ly/PPP-Blinky-Instructions |
| nixnax | 142:54d1543e23e5 | 10 | // http://bit.ly/win-rasdial-config |
| nixnax | 142:54d1543e23e5 | 11 | |
| nixnax | 142:54d1543e23e5 | 12 | // Handy reading material |
| nixnax | 142:54d1543e23e5 | 13 | // https://technet.microsoft.com/en-us/library/cc957992.aspx |
| nixnax | 142:54d1543e23e5 | 14 | // https://en.wikibooks.org/wiki/Serial_Programming/IP_Over_Serial_Connections |
| nixnax | 142:54d1543e23e5 | 15 | // http://atari.kensclassics.org/wcomlog.htm |
| nixnax | 142:54d1543e23e5 | 16 | |
| nixnax | 142:54d1543e23e5 | 17 | // Handy tools |
| nixnax | 142:54d1543e23e5 | 18 | // https://ttssh2.osdn.jp/index.html.en - Tera Term, a good terminal program to monitor the debug output from the second serial port with! |
| nixnax | 142:54d1543e23e5 | 19 | // https://www.microsoft.com/en-us/download/details.aspx?id=4865 - Microsoft network monitor - real-time monitoring of PPP packets |
| nixnax | 142:54d1543e23e5 | 20 | // http://pingtester.net/ - nice tool for high rate ping testing |
| nixnax | 142:54d1543e23e5 | 21 | // http://www.sunshine2k.de/coding/javascript/crc/crc_js.html - Correctly calculates the 16-bit FCS (crc) on our frames (Choose CRC16_CCITT_FALSE), then custom relected-in=1, reflected-out=1 |
| nixnax | 142:54d1543e23e5 | 22 | // https://technet.microsoft.com/en-us/sysinternals/pstools.aspx - psping for fast testing of ICMP ping function |
| nixnax | 142:54d1543e23e5 | 23 | // https://eternallybored.org/misc/netcat/ - use netcat -u 172.10.10.1 80 to send/receive UDP packets from PPP-Blinky |
| nixnax | 142:54d1543e23e5 | 24 | // Windows Powershell invoke-webrequest command - use it to stress test the webserver like this: while (1){ invoke-webrequest -uri 172.10.10.1/x } |
| nixnax | 142:54d1543e23e5 | 25 | |
| nixnax | 142:54d1543e23e5 | 26 | // Connecting PPP-Blinky to Linux |
| nixnax | 142:54d1543e23e5 | 27 | // PPP-Blinky can be made to talk to Linux - tested on Fedora - the following command, which uses pppd, works: |
| nixnax | 142:54d1543e23e5 | 28 | // pppd /dev/ttyACM0 115200 debug dump local passive noccp novj nodetach nocrtscts 172.10.10.1:172.10.10.2 |
| nixnax | 142:54d1543e23e5 | 29 | // in the above command 172.10.10.1 is the adapter IP, and 172.10.10.2 is the IP of PPP-Blinky. |
| nixnax | 142:54d1543e23e5 | 30 | // See also https://en.wikipedia.org/wiki/Point-to-Point_Protocol_daemon |
| nixnax | 142:54d1543e23e5 | 31 | |
| nixnax | 142:54d1543e23e5 | 32 | // Special pages when PPP-Blinky is running |
| nixnax | 142:54d1543e23e5 | 33 | // 172.10.10.2 root page |
| nixnax | 143:c5019f856a56 | 34 | // 172.10.10.2/x returns a number that increments every time you request a page - this is handy for testing |
| nixnax | 146:a45f49a2b29c | 35 | // 172.10.10.2/xb also returns a number, but issues a fast refresh meta command. This allows you to use your browser to benchmark page load speed |
| nixnax | 142:54d1543e23e5 | 36 | // 172.10.10.2/ws a simple WebSocket demo |
| nixnax | 142:54d1543e23e5 | 37 | // http://jsfiddle.net/d26cyuh2/ more complete WebSocket demo in JSFiddle |
| nixnax | 142:54d1543e23e5 | 38 | |
| nixnax | 142:54d1543e23e5 | 39 | // Ok, enough talking, time to check out some code!! |
| nixnax | 142:54d1543e23e5 | 40 | |
| nixnax | 142:54d1543e23e5 | 41 | #include "ppp-blinky.h" |
| nixnax | 142:54d1543e23e5 | 42 | |
| nixnax | 142:54d1543e23e5 | 43 | // The #define below enables/disables a second (OPTIONAL) serial port that prints out interesting diagnostic messages. |
| nixnax | 146:a45f49a2b29c | 44 | // Change to SERIAL_PORT_MONITOR_YES to enable diagnostics messages. You need to wire a second serial port to your mbed hardware to monitor the debug output. |
| nixnax | 142:54d1543e23e5 | 45 | // Using the second serial port will slow down packet response time |
| nixnax | 142:54d1543e23e5 | 46 | // Note - the LPC11U24 does NOT have a second serial port |
| nixnax | 146:a45f49a2b29c | 47 | |
| nixnax | 148:4225c3608b80 | 48 | #define SERIAL_PORT_MONITOR_NO /* change to SERIAL_PORT_MONITOR_YES for debug messages */ |
| nixnax | 142:54d1543e23e5 | 49 | |
| nixnax | 142:54d1543e23e5 | 50 | // here we define the OPTIONAL, second debug serial port for various mbed target boards |
| nixnax | 142:54d1543e23e5 | 51 | #ifdef SERIAL_PORT_MONITOR_YES |
| nixnax | 142:54d1543e23e5 | 52 | #if defined(TARGET_LPC1768) |
| nixnax | 142:54d1543e23e5 | 53 | Serial xx(p9, p10); // Second serial port on LPC1768 - not required to run, if you get compile error here, change #define SERIAL_PORT_MONITOR_YES to #define SERIAL_PORT_MONITOR_NO |
| nixnax | 142:54d1543e23e5 | 54 | #elif defined(TARGET_NUCLEO_F446RE) || defined(TARGET_NUCLEO_L152RE) || defined(TARGET_NUCLEO_L053R8) || defined(TARGET_NUCLEO_L476RG) || defined(TARGET_NUCLEO_F401RE) |
| nixnax | 142:54d1543e23e5 | 55 | Serial xx(PC_10, PC_11); // Second serial port on NUCLEO boards - not required to run, if you get compile error here, change #define SERIAL_PORT_MONITOR_YES to #define SERIAL_PORT_MONITOR_NO |
| nixnax | 142:54d1543e23e5 | 56 | #elif defined(TARGET_LPC11U24) |
| nixnax | 142:54d1543e23e5 | 57 | #error The LPC11U24 does not have a second serial port to use for debugging - change SERIAL_PORT_MONITOR_YES back to SERIAL_PORT_MONITOR_NO |
| nixnax | 142:54d1543e23e5 | 58 | #elif defined (TARGET_KL46Z) || (TARGET_KL25Z) |
| nixnax | 142:54d1543e23e5 | 59 | Serial xx(PTE0,PTE1); // Second serial port on FRDM-KL46Z board |
| nixnax | 142:54d1543e23e5 | 60 | #elif defined(YOUR_TARGET_BOARD_NAME_HERE) |
| nixnax | 142:54d1543e23e5 | 61 | // change the next line to YOUR target board's second serial port pin definition if it's not present - and if it works, please send it to me - thanks!!! |
| nixnax | 142:54d1543e23e5 | 62 | Serial xx(p9, p10); // change this to YOUR board second serial port pin definition - and please send it to me if it works!!! |
| nixnax | 142:54d1543e23e5 | 63 | #else |
| nixnax | 142:54d1543e23e5 | 64 | #error Add your target board's second serial port here if you want to use debugging - or simply change SERIAL_PORT_MONITOR_YES to SERIAL_PORT_MONITOR_NO |
| nixnax | 142:54d1543e23e5 | 65 | #endif |
| nixnax | 142:54d1543e23e5 | 66 | #define debugPrintf(x...) xx.printf (x) /* if we have a serial port we print debug messages */ |
| nixnax | 142:54d1543e23e5 | 67 | #define debugPutc(x...) xx.putc(x) |
| nixnax | 142:54d1543e23e5 | 68 | #define debugBaudRate(x...) xx.baud(x) |
| nixnax | 142:54d1543e23e5 | 69 | #else |
| nixnax | 142:54d1543e23e5 | 70 | // if we don't have a debug port the debug print functions do nothing |
| nixnax | 142:54d1543e23e5 | 71 | #define debugPrintf(x...) {} |
| nixnax | 142:54d1543e23e5 | 72 | #define debugPutc(x...) {} |
| nixnax | 142:54d1543e23e5 | 73 | #define debugBaudRate(x...) {} |
| nixnax | 142:54d1543e23e5 | 74 | #endif |
| nixnax | 142:54d1543e23e5 | 75 | |
| nixnax | 142:54d1543e23e5 | 76 | // verbosity flags used in debug printouts - change to 1 to see increasingly more detailed debug info. |
| nixnax | 142:54d1543e23e5 | 77 | #define v0 1 |
| nixnax | 142:54d1543e23e5 | 78 | #define v1 0 |
| nixnax | 142:54d1543e23e5 | 79 | #define v2 0 |
| nixnax | 142:54d1543e23e5 | 80 | #define IP_HEADER_DUMP_YES /* YES for ip header dump */ |
| nixnax | 142:54d1543e23e5 | 81 | #define TCP_HEADER_DUMP_YES /* YES for tcp header dump */ |
| nixnax | 142:54d1543e23e5 | 82 | |
| nixnax | 142:54d1543e23e5 | 83 | // this is the webpage we serve when we get an HTTP request to root (/) |
| nixnax | 142:54d1543e23e5 | 84 | // keep size under ~900 bytes to fit into a single PPP packet |
| nixnax | 142:54d1543e23e5 | 85 | |
| nixnax | 142:54d1543e23e5 | 86 | const static char rootWebPage[] = "\ |
| nixnax | 142:54d1543e23e5 | 87 | <!DOCTYPE html>\ |
| nixnax | 142:54d1543e23e5 | 88 | <html>\ |
| nixnax | 142:54d1543e23e5 | 89 | <head>\ |
| nixnax | 146:a45f49a2b29c | 90 | <title>mbed PPP-Blinky</title>\r\n\ |
| nixnax | 146:a45f49a2b29c | 91 | <script>\r\n\ |
| nixnax | 142:54d1543e23e5 | 92 | window.onload=function(){\ |
| nixnax | 142:54d1543e23e5 | 93 | setInterval(function(){function x(){return document.getElementById('w');};\ |
| nixnax | 146:a45f49a2b29c | 94 | x().textContent=parseInt(x().textContent)+1;},100);};\r\n\ |
| nixnax | 146:a45f49a2b29c | 95 | </script>\r\n\ |
| nixnax | 142:54d1543e23e5 | 96 | </head>\ |
| nixnax | 142:54d1543e23e5 | 97 | <body style=\"font-family: sans-serif; font-size:20px; text-align:center; color:#807070\">\ |
| nixnax | 142:54d1543e23e5 | 98 | <h1>mbed PPP-Blinky Up and Running</h1>\ |
| nixnax | 142:54d1543e23e5 | 99 | <h1 id=\"w\">0</h1>\ |
| nixnax | 142:54d1543e23e5 | 100 | <h1><a href=\"http://bit.ly/pppBlink2\">Source on mbed</a></h1>\ |
| nixnax | 142:54d1543e23e5 | 101 | <h1><a href=\"/ws\">WebSocket Demo</a></h1>\ |
| nixnax | 142:54d1543e23e5 | 102 | <h1><a href=\"/x\">Benchmark 1</a></h1>\ |
| nixnax | 142:54d1543e23e5 | 103 | <h1><a href=\"/xb\">Benchmark 2</a></h1>\ |
| nixnax | 142:54d1543e23e5 | 104 | <h1><a href=\"http://jsfiddle.net/d26cyuh2/\">JSFiddle Demo</a></h1>\ |
| nixnax | 142:54d1543e23e5 | 105 | </body>\ |
| nixnax | 146:a45f49a2b29c | 106 | </html>\r\n"; // size = 644 bytes plus 1 null byte = 645 bytes |
| nixnax | 142:54d1543e23e5 | 107 | |
| nixnax | 142:54d1543e23e5 | 108 | const static char webSocketPage[] = "\ |
| nixnax | 142:54d1543e23e5 | 109 | <!DOCTYPE html>\ |
| nixnax | 142:54d1543e23e5 | 110 | <html>\ |
| nixnax | 142:54d1543e23e5 | 111 | <head>\ |
| nixnax | 142:54d1543e23e5 | 112 | <title>mbed PPP-Blinky</title>\ |
| nixnax | 142:54d1543e23e5 | 113 | <script>\ |
| nixnax | 142:54d1543e23e5 | 114 | window.onload=function(){\ |
| nixnax | 142:54d1543e23e5 | 115 | var url=\"ws://172.10.10.2\";\ |
| nixnax | 142:54d1543e23e5 | 116 | var sts=document.getElementById(\"sts\");\ |
| nixnax | 142:54d1543e23e5 | 117 | var btn=document.getElementById(\"btn\");\ |
| nixnax | 142:54d1543e23e5 | 118 | var ctr=0;\ |
| nixnax | 142:54d1543e23e5 | 119 | function show(text){sts.textContent=text;}\ |
| nixnax | 142:54d1543e23e5 | 120 | btn.onclick=function(){\ |
| nixnax | 142:54d1543e23e5 | 121 | if(btn.textContent==\"Connect\"){\ |
| nixnax | 142:54d1543e23e5 | 122 | x=new WebSocket(url);\ |
| nixnax | 142:54d1543e23e5 | 123 | x.onopen=function(){\ |
| nixnax | 142:54d1543e23e5 | 124 | show(\"Connected to : \"+url);\ |
| nixnax | 142:54d1543e23e5 | 125 | btn.textContent=\"Send \\\"\"+ctr+\"\\\"\";\ |
| nixnax | 142:54d1543e23e5 | 126 | };\ |
| nixnax | 142:54d1543e23e5 | 127 | x.onclose=function(){show(\"closed\");};\ |
| nixnax | 142:54d1543e23e5 | 128 | x.onmessage=function(msg){show(\"PPP-Blinky Sent: \\\"\"+msg.data+\"\\\"\");};\ |
| nixnax | 142:54d1543e23e5 | 129 | } else {\ |
| nixnax | 142:54d1543e23e5 | 130 | x.send(ctr);\ |
| nixnax | 142:54d1543e23e5 | 131 | ctr=ctr+1;\ |
| nixnax | 142:54d1543e23e5 | 132 | btn.textContent=\"Send \\\"\"+ctr+\"\\\"\";\ |
| nixnax | 142:54d1543e23e5 | 133 | }\ |
| nixnax | 142:54d1543e23e5 | 134 | };\ |
| nixnax | 142:54d1543e23e5 | 135 | };\ |
| nixnax | 142:54d1543e23e5 | 136 | </script>\ |
| nixnax | 142:54d1543e23e5 | 137 | <body style=\"font-family: sans-serif; font-size:25px; color:#807070\">\ |
| nixnax | 142:54d1543e23e5 | 138 | <h1>PPP-Blinky WebSocket Test</h1>\ |
| nixnax | 142:54d1543e23e5 | 139 | <div id=\"sts\">Idle</div>\ |
| nixnax | 142:54d1543e23e5 | 140 | <button id=\"btn\" style=\"font-size: 100%; margin-top: 55px; margin-bottom: 55px;\">Connect</button>\ |
| nixnax | 142:54d1543e23e5 | 141 | <h4><a href=\"/\">PPP-Blinky home</a></h4>\ |
| nixnax | 142:54d1543e23e5 | 142 | </body>\ |
| nixnax | 142:54d1543e23e5 | 143 | </html>"; // size = 916 bytes + 1 null byte = 917 bytes |
| nixnax | 142:54d1543e23e5 | 144 | |
| nixnax | 142:54d1543e23e5 | 145 | // The serial port on your mbed hardware. Your PC should be configured to view this port as a standard dial-up networking modem. |
| nixnax | 142:54d1543e23e5 | 146 | // On Windows the model type of the modem should be selected as "Communications cable between two computers" |
| nixnax | 142:54d1543e23e5 | 147 | // The modem baud rate should be set to 115200 baud |
| nixnax | 142:54d1543e23e5 | 148 | // See instructions at the top. |
| nixnax | 142:54d1543e23e5 | 149 | // On a typical mbed hardware platform this serial port is a USB virtual com port (VCP) and the USB serial driver is supplied by the board vendor. |
| nixnax | 142:54d1543e23e5 | 150 | BufferedSerial pc(USBTX, USBRX, 100); // usb virtual com port for mbed hardware |
| nixnax | 142:54d1543e23e5 | 151 | |
| nixnax | 142:54d1543e23e5 | 152 | DigitalOut led1(LED1); // this led toggles when a packet is received |
| nixnax | 142:54d1543e23e5 | 153 | |
| nixnax | 142:54d1543e23e5 | 154 | // the standard hdlc frame start/end character. It's the tilde character "~" |
| nixnax | 142:54d1543e23e5 | 155 | #define FRAME_7E (0x7e) |
| nixnax | 142:54d1543e23e5 | 156 | |
| nixnax | 142:54d1543e23e5 | 157 | /// a structure to keep all our ppp globals in |
| nixnax | 142:54d1543e23e5 | 158 | struct pppType { |
| nixnax | 142:54d1543e23e5 | 159 | int online; // we hunt for a PPP connection if this is zero |
| nixnax | 143:c5019f856a56 | 160 | int hostIP; // ip address of host |
| nixnax | 145:098b6ed2f7f2 | 161 | int fcs; // PPP "frame check sequence" - a 16-bit HDLC-like checksum used in all PPP frames |
| nixnax | 142:54d1543e23e5 | 162 | int ledState; // state of LED1 |
| nixnax | 146:a45f49a2b29c | 163 | int responseCounter; |
| nixnax | 142:54d1543e23e5 | 164 | int firstFrame; // cleared after first frame |
| nixnax | 142:54d1543e23e5 | 165 | struct { |
| nixnax | 142:54d1543e23e5 | 166 | #define RXBUFLEN (1<<11) |
| nixnax | 142:54d1543e23e5 | 167 | // the serial port receive buffer and packet buffer, size is RXBUFLEN (currently 2048 bytes) |
| nixnax | 142:54d1543e23e5 | 168 | char buf[RXBUFLEN]; // RXBUFLEN MUST be a power of two because we use & operator for fast wrap-around in ring buffer |
| nixnax | 142:54d1543e23e5 | 169 | int head; |
| nixnax | 142:54d1543e23e5 | 170 | int tail; |
| nixnax | 142:54d1543e23e5 | 171 | int rtail; |
| nixnax | 142:54d1543e23e5 | 172 | int buflevel; |
| nixnax | 142:54d1543e23e5 | 173 | } rx; // serial port objects |
| nixnax | 142:54d1543e23e5 | 174 | struct { |
| nixnax | 142:54d1543e23e5 | 175 | int len; // number of bytes in buffer |
| nixnax | 142:54d1543e23e5 | 176 | int crc; // PPP CRC (frame check) |
| nixnax | 142:54d1543e23e5 | 177 | #define PPP_max_size 2500 |
| nixnax | 142:54d1543e23e5 | 178 | // we are assuming 1000 bytes more than MTU size of 1500 - due to the PPP encoding of special bytes |
| nixnax | 142:54d1543e23e5 | 179 | char buf[PPP_max_size]; // send and receive buffer large enough for raw, encoded PPP/HDLC frames |
| nixnax | 142:54d1543e23e5 | 180 | } pkt; // ppp buffer objects |
| nixnax | 142:54d1543e23e5 | 181 | struct { |
| nixnax | 142:54d1543e23e5 | 182 | int frameStartIndex; // frame start marker |
| nixnax | 142:54d1543e23e5 | 183 | int frameEndIndex; // frame end marker |
| nixnax | 142:54d1543e23e5 | 184 | } hdlc; // hdlc frame objects |
| nixnax | 142:54d1543e23e5 | 185 | struct { |
| nixnax | 142:54d1543e23e5 | 186 | unsigned int ident; // our IP ident value (outgoing frame count) |
| nixnax | 142:54d1543e23e5 | 187 | } ip; // ip related object |
| nixnax | 142:54d1543e23e5 | 188 | }; |
| nixnax | 142:54d1543e23e5 | 189 | |
| nixnax | 142:54d1543e23e5 | 190 | pppType ppp; // our global - definitely not thread safe |
| nixnax | 142:54d1543e23e5 | 191 | |
| nixnax | 142:54d1543e23e5 | 192 | /// Initialize the ppp structure and clear the receive buffer |
| nixnax | 142:54d1543e23e5 | 193 | void pppInitStruct() |
| nixnax | 142:54d1543e23e5 | 194 | { |
| nixnax | 142:54d1543e23e5 | 195 | memset( ppp.rx.buf, 0, RXBUFLEN); |
| nixnax | 142:54d1543e23e5 | 196 | ppp.online=0; |
| nixnax | 142:54d1543e23e5 | 197 | ppp.rx.tail=0; |
| nixnax | 142:54d1543e23e5 | 198 | ppp.rx.rtail=0; |
| nixnax | 142:54d1543e23e5 | 199 | ppp.rx.head=0; |
| nixnax | 142:54d1543e23e5 | 200 | ppp.rx.buflevel=0; |
| nixnax | 142:54d1543e23e5 | 201 | ppp.pkt.len=0; |
| nixnax | 142:54d1543e23e5 | 202 | ppp.ip.ident=10000; // easy to recognize in ip packet dumps |
| nixnax | 142:54d1543e23e5 | 203 | ppp.ledState=0; |
| nixnax | 142:54d1543e23e5 | 204 | ppp.hdlc.frameStartIndex=0; |
| nixnax | 146:a45f49a2b29c | 205 | ppp.responseCounter=0; |
| nixnax | 142:54d1543e23e5 | 206 | ppp.firstFrame=1; |
| nixnax | 142:54d1543e23e5 | 207 | } |
| nixnax | 142:54d1543e23e5 | 208 | |
| nixnax | 142:54d1543e23e5 | 209 | /// Toggle the LED on every second PPP packet received |
| nixnax | 142:54d1543e23e5 | 210 | void led1Toggle() |
| nixnax | 142:54d1543e23e5 | 211 | { |
| nixnax | 142:54d1543e23e5 | 212 | led1 = (ppp.ledState >> 1) & 1; // use second bit, in other words toggle LED only every second packet |
| nixnax | 143:c5019f856a56 | 213 | ppp.ledState++; |
| nixnax | 142:54d1543e23e5 | 214 | } |
| nixnax | 142:54d1543e23e5 | 215 | |
| nixnax | 142:54d1543e23e5 | 216 | /// returns 1 after a connect messasge, 0 at startup or after a disconnect message |
| nixnax | 142:54d1543e23e5 | 217 | int connected() |
| nixnax | 142:54d1543e23e5 | 218 | { |
| nixnax | 142:54d1543e23e5 | 219 | return ppp.online; |
| nixnax | 143:c5019f856a56 | 220 | } |
| nixnax | 142:54d1543e23e5 | 221 | |
| nixnax | 143:c5019f856a56 | 222 | /// Check for available characters from the PC and read them into our own circular serial receive buffer at ppp.rx.buf. |
| nixnax | 143:c5019f856a56 | 223 | /// Also, if we are offline and a 0x7e frame start character is seen, we go online immediately |
| nixnax | 142:54d1543e23e5 | 224 | void checkPc() |
| nixnax | 142:54d1543e23e5 | 225 | { |
| nixnax | 142:54d1543e23e5 | 226 | char ch; |
| nixnax | 142:54d1543e23e5 | 227 | if ( pc.readable() ) { |
| nixnax | 142:54d1543e23e5 | 228 | int hd = (ppp.rx.head+1)&(RXBUFLEN-1); // increment/wrap head index |
| nixnax | 142:54d1543e23e5 | 229 | if ( hd == ppp.rx.rtail ) { |
| nixnax | 142:54d1543e23e5 | 230 | debugPrintf("\nReceive buffer full\n"); |
| nixnax | 142:54d1543e23e5 | 231 | return; |
| nixnax | 142:54d1543e23e5 | 232 | } |
| nixnax | 142:54d1543e23e5 | 233 | ch = pc.getc(); // read new character |
| nixnax | 142:54d1543e23e5 | 234 | ppp.rx.buf[ppp.rx.head] = ch; // insert in our receive buffer |
| nixnax | 142:54d1543e23e5 | 235 | if ( ppp.online == 0 ) { |
| nixnax | 142:54d1543e23e5 | 236 | if (ch == 0x7E) { |
| nixnax | 142:54d1543e23e5 | 237 | ppp.online = 1; |
| nixnax | 142:54d1543e23e5 | 238 | } |
| nixnax | 142:54d1543e23e5 | 239 | } |
| nixnax | 142:54d1543e23e5 | 240 | ppp.rx.head = hd; // update head pointer |
| nixnax | 142:54d1543e23e5 | 241 | ppp.rx.buflevel++; |
| nixnax | 142:54d1543e23e5 | 242 | } |
| nixnax | 142:54d1543e23e5 | 243 | } |
| nixnax | 142:54d1543e23e5 | 244 | |
| nixnax | 142:54d1543e23e5 | 245 | /// print to debug port while checking for incoming characters |
| nixnax | 142:54d1543e23e5 | 246 | void putcWhileCheckingInput( char outByte ) |
| nixnax | 142:54d1543e23e5 | 247 | { |
| nixnax | 142:54d1543e23e5 | 248 | #ifdef SERIAL_PORT_MONITOR_YES |
| nixnax | 142:54d1543e23e5 | 249 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 250 | debugPutc( outByte ); |
| nixnax | 142:54d1543e23e5 | 251 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 252 | #endif |
| nixnax | 142:54d1543e23e5 | 253 | } |
| nixnax | 142:54d1543e23e5 | 254 | |
| nixnax | 142:54d1543e23e5 | 255 | /// puts to debug port while checking the PPP input stream |
| nixnax | 142:54d1543e23e5 | 256 | void putsWhileCheckingInput( char * data ) |
| nixnax | 142:54d1543e23e5 | 257 | { |
| nixnax | 142:54d1543e23e5 | 258 | #ifdef SERIAL_PORT_MONITOR_YES |
| nixnax | 142:54d1543e23e5 | 259 | char * nextChar = data; |
| nixnax | 142:54d1543e23e5 | 260 | while( *nextChar != 0 ) { |
| nixnax | 142:54d1543e23e5 | 261 | putcWhileCheckingInput( *nextChar ); // write one character to debug port while checking input |
| nixnax | 142:54d1543e23e5 | 262 | nextChar++; |
| nixnax | 142:54d1543e23e5 | 263 | } |
| nixnax | 142:54d1543e23e5 | 264 | #endif |
| nixnax | 142:54d1543e23e5 | 265 | } |
| nixnax | 142:54d1543e23e5 | 266 | |
| nixnax | 145:098b6ed2f7f2 | 267 | /// Initialize the PPP FCS (frame check sequence) total |
| nixnax | 145:098b6ed2f7f2 | 268 | void fcsReset() |
| nixnax | 142:54d1543e23e5 | 269 | { |
| nixnax | 145:098b6ed2f7f2 | 270 | ppp.fcs=0xffff; // crc restart |
| nixnax | 142:54d1543e23e5 | 271 | } |
| nixnax | 142:54d1543e23e5 | 272 | |
| nixnax | 145:098b6ed2f7f2 | 273 | /// update the cumulative PPP FCS (frame check sequence) |
| nixnax | 145:098b6ed2f7f2 | 274 | void fcsDo(int x) |
| nixnax | 142:54d1543e23e5 | 275 | { |
| nixnax | 142:54d1543e23e5 | 276 | for (int i=0; i<8; i++) { |
| nixnax | 145:098b6ed2f7f2 | 277 | ppp.fcs=((ppp.fcs&1)^(x&1))?(ppp.fcs>>1)^0x8408:ppp.fcs>>1; // crc calculator |
| nixnax | 142:54d1543e23e5 | 278 | x>>=1; |
| nixnax | 142:54d1543e23e5 | 279 | } |
| nixnax | 142:54d1543e23e5 | 280 | checkPc(); // handle input |
| nixnax | 142:54d1543e23e5 | 281 | } |
| nixnax | 142:54d1543e23e5 | 282 | |
| nixnax | 145:098b6ed2f7f2 | 283 | /// calculate the PPP FCS (frame check sequence) on an entire block of memory |
| nixnax | 145:098b6ed2f7f2 | 284 | int fcsBuf(char * buf, int size) // crc on an entire block of memory |
| nixnax | 142:54d1543e23e5 | 285 | { |
| nixnax | 145:098b6ed2f7f2 | 286 | fcsReset(); |
| nixnax | 145:098b6ed2f7f2 | 287 | for(int i=0; i<size; i++)fcsDo(*buf++); |
| nixnax | 145:098b6ed2f7f2 | 288 | return ppp.fcs; |
| nixnax | 142:54d1543e23e5 | 289 | } |
| nixnax | 142:54d1543e23e5 | 290 | |
| nixnax | 142:54d1543e23e5 | 291 | /// Get one character from our received PPP buffer |
| nixnax | 142:54d1543e23e5 | 292 | int pc_getBuf() |
| nixnax | 142:54d1543e23e5 | 293 | { |
| nixnax | 142:54d1543e23e5 | 294 | int x = ppp.rx.buf[ ppp.rx.tail ]; |
| nixnax | 142:54d1543e23e5 | 295 | ppp.rx.tail=(ppp.rx.tail+1)&(RXBUFLEN-1); |
| nixnax | 142:54d1543e23e5 | 296 | ppp.rx.buflevel--; |
| nixnax | 142:54d1543e23e5 | 297 | return x; |
| nixnax | 142:54d1543e23e5 | 298 | } |
| nixnax | 142:54d1543e23e5 | 299 | |
| nixnax | 142:54d1543e23e5 | 300 | /// Dump a PPP frame to the debug serial port |
| nixnax | 142:54d1543e23e5 | 301 | /// Note - the hex output of dumpPPPFrame() can be imported into WireShark |
| nixnax | 142:54d1543e23e5 | 302 | /// Capture the frame's hex output in your terminal program and save as a text file |
| nixnax | 142:54d1543e23e5 | 303 | /// In WireShark, use "Import Hex File". Options are: Offset=None, Protocol=PPP. |
| nixnax | 142:54d1543e23e5 | 304 | void dumpPPPFrame() |
| nixnax | 142:54d1543e23e5 | 305 | { |
| nixnax | 142:54d1543e23e5 | 306 | char pbuf[30]; |
| nixnax | 142:54d1543e23e5 | 307 | for(int i=0; i<ppp.pkt.len; i++) { |
| nixnax | 142:54d1543e23e5 | 308 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 309 | sprintf(pbuf, "%02x ", ppp.pkt.buf[i]); |
| nixnax | 142:54d1543e23e5 | 310 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 311 | putsWhileCheckingInput(pbuf); |
| nixnax | 142:54d1543e23e5 | 312 | } |
| nixnax | 142:54d1543e23e5 | 313 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 314 | sprintf(pbuf, " CRC=%04x Len=%d\n", ppp.pkt.crc, ppp.pkt.len); |
| nixnax | 142:54d1543e23e5 | 315 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 316 | putsWhileCheckingInput(pbuf); |
| nixnax | 142:54d1543e23e5 | 317 | } |
| nixnax | 142:54d1543e23e5 | 318 | |
| nixnax | 142:54d1543e23e5 | 319 | /// Process a received PPP frame |
| nixnax | 142:54d1543e23e5 | 320 | void processPPPFrame(int start, int end) |
| nixnax | 142:54d1543e23e5 | 321 | { |
| nixnax | 142:54d1543e23e5 | 322 | led1Toggle(); // change led1 state on every frame we receive |
| nixnax | 142:54d1543e23e5 | 323 | if(start==end) { |
| nixnax | 142:54d1543e23e5 | 324 | return; // empty frame |
| nixnax | 142:54d1543e23e5 | 325 | } |
| nixnax | 145:098b6ed2f7f2 | 326 | fcsReset(); |
| nixnax | 142:54d1543e23e5 | 327 | char * dest = ppp.pkt.buf; |
| nixnax | 142:54d1543e23e5 | 328 | ppp.pkt.len=0; |
| nixnax | 142:54d1543e23e5 | 329 | int unstuff=0; |
| nixnax | 142:54d1543e23e5 | 330 | int idx = start; |
| nixnax | 142:54d1543e23e5 | 331 | while(1) { |
| nixnax | 142:54d1543e23e5 | 332 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 333 | if (unstuff==0) { |
| nixnax | 142:54d1543e23e5 | 334 | if (ppp.rx.buf[idx]==0x7d) unstuff=1; |
| nixnax | 142:54d1543e23e5 | 335 | else { |
| nixnax | 142:54d1543e23e5 | 336 | *dest = ppp.rx.buf[idx]; |
| nixnax | 142:54d1543e23e5 | 337 | ppp.pkt.len++; |
| nixnax | 142:54d1543e23e5 | 338 | dest++; |
| nixnax | 145:098b6ed2f7f2 | 339 | fcsDo(ppp.rx.buf[idx]); |
| nixnax | 142:54d1543e23e5 | 340 | } |
| nixnax | 142:54d1543e23e5 | 341 | } else { // unstuff characters prefixed with 0x7d |
| nixnax | 142:54d1543e23e5 | 342 | *dest = ppp.rx.buf[idx]^0x20; |
| nixnax | 142:54d1543e23e5 | 343 | ppp.pkt.len++; |
| nixnax | 142:54d1543e23e5 | 344 | dest++; |
| nixnax | 145:098b6ed2f7f2 | 345 | fcsDo(ppp.rx.buf[idx]^0x20); |
| nixnax | 142:54d1543e23e5 | 346 | unstuff=0; |
| nixnax | 142:54d1543e23e5 | 347 | } |
| nixnax | 142:54d1543e23e5 | 348 | idx = (idx+1) & (RXBUFLEN-1); |
| nixnax | 142:54d1543e23e5 | 349 | if (idx == end) break; |
| nixnax | 142:54d1543e23e5 | 350 | } |
| nixnax | 145:098b6ed2f7f2 | 351 | ppp.pkt.crc = ppp.fcs & 0xffff; |
| nixnax | 142:54d1543e23e5 | 352 | if(0) dumpPPPFrame(); // set to 1 to dump ALL ppp frames |
| nixnax | 142:54d1543e23e5 | 353 | if (ppp.pkt.crc == 0xf0b8) { // check for good CRC |
| nixnax | 142:54d1543e23e5 | 354 | determinePacketType(); |
| nixnax | 142:54d1543e23e5 | 355 | } else { |
| nixnax | 142:54d1543e23e5 | 356 | #define REPORT_FCS_ERROR_YES |
| nixnax | 142:54d1543e23e5 | 357 | #ifdef REPORT_FCS_ERROR_YES |
| nixnax | 142:54d1543e23e5 | 358 | char pbuf[50]; // local print buffer |
| nixnax | 142:54d1543e23e5 | 359 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 360 | sprintf(pbuf, "\nPPP FCS(crc) Error CRC=%x Length = %d\n",ppp.pkt.crc,ppp.pkt.len); // print a debug line |
| nixnax | 142:54d1543e23e5 | 361 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 362 | putsWhileCheckingInput( pbuf ); |
| nixnax | 142:54d1543e23e5 | 363 | if(0) dumpPPPFrame(); // set to 1 to dump frames with errors in them |
| nixnax | 142:54d1543e23e5 | 364 | #endif |
| nixnax | 142:54d1543e23e5 | 365 | } |
| nixnax | 142:54d1543e23e5 | 366 | } |
| nixnax | 142:54d1543e23e5 | 367 | |
| nixnax | 142:54d1543e23e5 | 368 | /// output a character to the PPP port while checking for incoming characters |
| nixnax | 142:54d1543e23e5 | 369 | void pcPutcWhileCheckingInput(int ch) |
| nixnax | 142:54d1543e23e5 | 370 | { |
| nixnax | 142:54d1543e23e5 | 371 | checkPc(); // check input |
| nixnax | 142:54d1543e23e5 | 372 | pc.putc(ch); |
| nixnax | 142:54d1543e23e5 | 373 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 374 | } |
| nixnax | 142:54d1543e23e5 | 375 | |
| nixnax | 142:54d1543e23e5 | 376 | /// do PPP HDLC-like handling of special (flag) characters |
| nixnax | 143:c5019f856a56 | 377 | void hdlcPut(int ch) |
| nixnax | 142:54d1543e23e5 | 378 | { |
| nixnax | 142:54d1543e23e5 | 379 | if ( (ch<0x20) || (ch==0x7d) || (ch==0x7e) ) { |
| nixnax | 142:54d1543e23e5 | 380 | pcPutcWhileCheckingInput(0x7d); |
| nixnax | 142:54d1543e23e5 | 381 | pcPutcWhileCheckingInput(ch^0x20); // these characters need special handling |
| nixnax | 142:54d1543e23e5 | 382 | } else { |
| nixnax | 142:54d1543e23e5 | 383 | pcPutcWhileCheckingInput(ch); |
| nixnax | 142:54d1543e23e5 | 384 | } |
| nixnax | 142:54d1543e23e5 | 385 | } |
| nixnax | 142:54d1543e23e5 | 386 | |
| nixnax | 142:54d1543e23e5 | 387 | /// send a PPP frame in HDLC format |
| nixnax | 144:01d98cf7738e | 388 | void sendPppFrame() |
| nixnax | 143:c5019f856a56 | 389 | { |
| nixnax | 145:098b6ed2f7f2 | 390 | int crc = fcsBuf(ppp.pkt.buf, ppp.pkt.len-2); // update crc |
| nixnax | 142:54d1543e23e5 | 391 | ppp.pkt.buf[ ppp.pkt.len-2 ] = (~crc>>0); // fcs lo (crc) |
| nixnax | 142:54d1543e23e5 | 392 | ppp.pkt.buf[ ppp.pkt.len-1 ] = (~crc>>8); // fcs hi (crc) |
| nixnax | 142:54d1543e23e5 | 393 | pcPutcWhileCheckingInput(0x7e); // hdlc start-of-frame "flag" |
| nixnax | 142:54d1543e23e5 | 394 | for(int i=0; i<ppp.pkt.len; i++) { |
| nixnax | 142:54d1543e23e5 | 395 | wait_us(86); // wait one character time |
| nixnax | 142:54d1543e23e5 | 396 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 397 | hdlcPut( ppp.pkt.buf[i] ); // send a character |
| nixnax | 142:54d1543e23e5 | 398 | } |
| nixnax | 142:54d1543e23e5 | 399 | pcPutcWhileCheckingInput(0x7e); // hdlc end-of-frame "flag" |
| nixnax | 142:54d1543e23e5 | 400 | } |
| nixnax | 142:54d1543e23e5 | 401 | |
| nixnax | 143:c5019f856a56 | 402 | /// convert a network ip address in the buffer to an integer (IP adresses are big-endian, i.e most significant byte first) |
| nixnax | 143:c5019f856a56 | 403 | int bufferToIP(char * buffer) |
| nixnax | 143:c5019f856a56 | 404 | { |
| nixnax | 143:c5019f856a56 | 405 | int result=0; |
| nixnax | 143:c5019f856a56 | 406 | for(int i=0; i<4; i++) result = (result<<8)|(*buffer++ & 0xff); |
| nixnax | 143:c5019f856a56 | 407 | return result; |
| nixnax | 143:c5019f856a56 | 408 | } |
| nixnax | 143:c5019f856a56 | 409 | |
| nixnax | 142:54d1543e23e5 | 410 | /// handle IPCP configuration requests |
| nixnax | 142:54d1543e23e5 | 411 | void ipcpConfigRequestHandler() |
| nixnax | 142:54d1543e23e5 | 412 | { |
| nixnax | 142:54d1543e23e5 | 413 | debugPrintf("Their IPCP Config Req, Our Ack\n"); |
| nixnax | 143:c5019f856a56 | 414 | if(ppp.pkt.buf[8]==3) { |
| nixnax | 143:c5019f856a56 | 415 | ppp.hostIP = bufferToIP(ppp.pkt.buf+10); |
| nixnax | 143:c5019f856a56 | 416 | debugPrintf("Host IP = %d.%d.%d.%d (%08x)\n", ppp.pkt.buf[10],ppp.pkt.buf[11],ppp.pkt.buf[12],ppp.pkt.buf[13],ppp.hostIP); |
| nixnax | 143:c5019f856a56 | 417 | } |
| nixnax | 143:c5019f856a56 | 418 | |
| nixnax | 142:54d1543e23e5 | 419 | ppp.pkt.buf[4]=2; // change code to ack |
| nixnax | 144:01d98cf7738e | 420 | sendPppFrame(); // acknowledge everything they ask for - assume it's IP addresses |
| nixnax | 142:54d1543e23e5 | 421 | |
| nixnax | 142:54d1543e23e5 | 422 | debugPrintf("Our IPCP Ask (no options)\n"); |
| nixnax | 142:54d1543e23e5 | 423 | ppp.pkt.buf[4]=1; // change code to request |
| nixnax | 142:54d1543e23e5 | 424 | ppp.pkt.buf[7]=4; // no options in this request |
| nixnax | 142:54d1543e23e5 | 425 | ppp.pkt.len=10; // no options in this request shortest ipcp packet possible (4 ppp + 4 ipcp + 2 crc) |
| nixnax | 144:01d98cf7738e | 426 | sendPppFrame(); // send our request |
| nixnax | 142:54d1543e23e5 | 427 | } |
| nixnax | 142:54d1543e23e5 | 428 | |
| nixnax | 142:54d1543e23e5 | 429 | /// handle IPCP acknowledge (do nothing) |
| nixnax | 142:54d1543e23e5 | 430 | void ipcpAckHandler() |
| nixnax | 142:54d1543e23e5 | 431 | { |
| nixnax | 142:54d1543e23e5 | 432 | debugPrintf("Their IPCP Grant\n"); |
| nixnax | 142:54d1543e23e5 | 433 | } |
| nixnax | 142:54d1543e23e5 | 434 | |
| nixnax | 143:c5019f856a56 | 435 | /// Handle IPCP NACK by sending our suggested IP address if there is an IP involved. |
| nixnax | 143:c5019f856a56 | 436 | /// This is how Linux responds to an IPCP request with no options - Windows assumes any IP address on the submnet is OK. |
| nixnax | 142:54d1543e23e5 | 437 | void ipcpNackHandler() |
| nixnax | 142:54d1543e23e5 | 438 | { |
| nixnax | 146:a45f49a2b29c | 439 | debugPrintf("Their IPCP Nack\n"); |
| nixnax | 142:54d1543e23e5 | 440 | if (ppp.pkt.buf[8]==3) { // check if the NACK contains an IP address parameter |
| nixnax | 142:54d1543e23e5 | 441 | ppp.pkt.buf[4]=1; // assume the NACK contains our "suggested" IP address |
| nixnax | 144:01d98cf7738e | 442 | sendPppFrame(); // let's request this IP address as ours |
| nixnax | 143:c5019f856a56 | 443 | debugPrintf("Our IPCP ACK (received an IP)\n"); |
| nixnax | 146:a45f49a2b29c | 444 | } else { // if it's not an IP nack we ignore it |
| nixnax | 146:a45f49a2b29c | 445 | debugPrintf("IPCP Nack Ignored\n"); |
| nixnax | 146:a45f49a2b29c | 446 | } |
| nixnax | 142:54d1543e23e5 | 447 | } |
| nixnax | 142:54d1543e23e5 | 448 | |
| nixnax | 142:54d1543e23e5 | 449 | /// handle all other IPCP requests (by ignoring them) |
| nixnax | 142:54d1543e23e5 | 450 | void ipcpDefaultHandler() |
| nixnax | 142:54d1543e23e5 | 451 | { |
| nixnax | 142:54d1543e23e5 | 452 | debugPrintf("Their IPCP Other\n"); |
| nixnax | 142:54d1543e23e5 | 453 | } |
| nixnax | 142:54d1543e23e5 | 454 | |
| nixnax | 142:54d1543e23e5 | 455 | /// process an incoming IPCP packet |
| nixnax | 142:54d1543e23e5 | 456 | void IPCPframe() |
| nixnax | 142:54d1543e23e5 | 457 | { |
| nixnax | 142:54d1543e23e5 | 458 | int code = ppp.pkt.buf[4]; // packet type is here |
| nixnax | 142:54d1543e23e5 | 459 | switch (code) { |
| nixnax | 142:54d1543e23e5 | 460 | case 1: |
| nixnax | 142:54d1543e23e5 | 461 | ipcpConfigRequestHandler(); |
| nixnax | 142:54d1543e23e5 | 462 | break; |
| nixnax | 142:54d1543e23e5 | 463 | case 2: |
| nixnax | 142:54d1543e23e5 | 464 | ipcpAckHandler(); |
| nixnax | 142:54d1543e23e5 | 465 | break; |
| nixnax | 142:54d1543e23e5 | 466 | case 3: |
| nixnax | 142:54d1543e23e5 | 467 | ipcpNackHandler(); |
| nixnax | 142:54d1543e23e5 | 468 | break; |
| nixnax | 142:54d1543e23e5 | 469 | default: |
| nixnax | 142:54d1543e23e5 | 470 | ipcpDefaultHandler(); |
| nixnax | 142:54d1543e23e5 | 471 | } |
| nixnax | 142:54d1543e23e5 | 472 | } |
| nixnax | 142:54d1543e23e5 | 473 | |
| nixnax | 142:54d1543e23e5 | 474 | /// perform a 16-bit checksum. if the byte count is odd, stuff in an extra zero byte. |
| nixnax | 142:54d1543e23e5 | 475 | unsigned int dataCheckSum(unsigned char * ptr, int len) |
| nixnax | 142:54d1543e23e5 | 476 | { |
| nixnax | 142:54d1543e23e5 | 477 | unsigned int i,hi,lo,sum; |
| nixnax | 142:54d1543e23e5 | 478 | unsigned char placeHolder; |
| nixnax | 142:54d1543e23e5 | 479 | if (len&1) { |
| nixnax | 142:54d1543e23e5 | 480 | placeHolder = ptr[len]; |
| nixnax | 142:54d1543e23e5 | 481 | ptr[len]=0; // if the byte count is odd, insert one extra zero byte is after the last real byte because we sum byte PAIRS |
| nixnax | 142:54d1543e23e5 | 482 | } |
| nixnax | 142:54d1543e23e5 | 483 | sum=0; |
| nixnax | 142:54d1543e23e5 | 484 | i=0; |
| nixnax | 142:54d1543e23e5 | 485 | while ( i<len ) { |
| nixnax | 142:54d1543e23e5 | 486 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 487 | hi = ptr[i++]; |
| nixnax | 142:54d1543e23e5 | 488 | lo = ptr[i++]; |
| nixnax | 142:54d1543e23e5 | 489 | sum = sum + ( (hi<<8) | lo ); |
| nixnax | 142:54d1543e23e5 | 490 | } |
| nixnax | 142:54d1543e23e5 | 491 | if (len&1) { |
| nixnax | 142:54d1543e23e5 | 492 | ptr[len] = placeHolder; // restore the extra byte we made zero |
| nixnax | 142:54d1543e23e5 | 493 | } |
| nixnax | 142:54d1543e23e5 | 494 | sum = (sum & 0xffff) + (sum>>16); |
| nixnax | 142:54d1543e23e5 | 495 | sum = (sum & 0xffff) + (sum>>16); // sum one more time to catch any carry from the carry |
| nixnax | 142:54d1543e23e5 | 496 | return ~sum; |
| nixnax | 142:54d1543e23e5 | 497 | } |
| nixnax | 142:54d1543e23e5 | 498 | |
| nixnax | 142:54d1543e23e5 | 499 | /// perform the checksum on an IP header |
| nixnax | 146:a45f49a2b29c | 500 | void IpHeaderCheckSum() |
| nixnax | 142:54d1543e23e5 | 501 | { |
| nixnax | 146:a45f49a2b29c | 502 | ppp.pkt.buf[4+10]=0; // zero the checsum in the IP header |
| nixnax | 146:a45f49a2b29c | 503 | ppp.pkt.buf[4+11]=0; // zero the checksum in the IP header |
| nixnax | 146:a45f49a2b29c | 504 | int len =(ppp.pkt.buf[4]&0xf)*4; // length of IP header in bytes |
| nixnax | 146:a45f49a2b29c | 505 | char * ptr = ppp.pkt.buf+4; // start of IP packet |
| nixnax | 142:54d1543e23e5 | 506 | int sum=0; |
| nixnax | 142:54d1543e23e5 | 507 | for (int i=0; i<len/2; i++) { |
| nixnax | 142:54d1543e23e5 | 508 | int hi = *ptr; |
| nixnax | 142:54d1543e23e5 | 509 | ptr++; |
| nixnax | 142:54d1543e23e5 | 510 | int lo = *ptr; |
| nixnax | 142:54d1543e23e5 | 511 | ptr++; |
| nixnax | 142:54d1543e23e5 | 512 | int val = ( lo & 0xff ) | ( (hi<<8) & 0xff00 ); |
| nixnax | 142:54d1543e23e5 | 513 | sum = sum + val; |
| nixnax | 142:54d1543e23e5 | 514 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 515 | } |
| nixnax | 142:54d1543e23e5 | 516 | sum = sum + (sum>>16); |
| nixnax | 142:54d1543e23e5 | 517 | sum = ~sum; |
| nixnax | 146:a45f49a2b29c | 518 | ppp.pkt.buf[4+10]= (sum>>8); |
| nixnax | 146:a45f49a2b29c | 519 | ppp.pkt.buf[4+11]= (sum ); |
| nixnax | 146:a45f49a2b29c | 520 | } |
| nixnax | 146:a45f49a2b29c | 521 | |
| nixnax | 147:0f40005cbc5f | 522 | /// swap the IP source and destination addresses |
| nixnax | 147:0f40005cbc5f | 523 | void swapIpAddresses() |
| nixnax | 147:0f40005cbc5f | 524 | { |
| nixnax | 147:0f40005cbc5f | 525 | char tempHold[4]; |
| nixnax | 147:0f40005cbc5f | 526 | memcpy(tempHold, ppp.pkt.buf+16,4); // tempHold <- source IP |
| nixnax | 147:0f40005cbc5f | 527 | memcpy(ppp.pkt.buf+16, ppp.pkt.buf+20,4); // source <- dest |
| nixnax | 147:0f40005cbc5f | 528 | memcpy(ppp.pkt.buf+20, tempHold,4); // dest <- tempHold |
| nixnax | 147:0f40005cbc5f | 529 | } |
| nixnax | 147:0f40005cbc5f | 530 | |
| nixnax | 149:969d98f6fb88 | 531 | /// swap the IP source and destination ports |
| nixnax | 149:969d98f6fb88 | 532 | void swapIpPorts() |
| nixnax | 149:969d98f6fb88 | 533 | { |
| nixnax | 149:969d98f6fb88 | 534 | int headerSizeIP = 4*(ppp.pkt.buf[4]&0xf); // calculate size of IP header |
| nixnax | 149:969d98f6fb88 | 535 | char * ipSrcPort = 4 + ppp.pkt.buf + headerSizeIP + 0; // ip source port location |
| nixnax | 149:969d98f6fb88 | 536 | char * ipDstPort = 4 + ppp.pkt.buf + headerSizeIP + 2; // ip destin port location |
| nixnax | 149:969d98f6fb88 | 537 | char tempHold[2]; |
| nixnax | 149:969d98f6fb88 | 538 | memcpy(tempHold, ipSrcPort,2); // tempHold <- source |
| nixnax | 149:969d98f6fb88 | 539 | memcpy(ipSrcPort,ipDstPort,2); // source <- dest |
| nixnax | 149:969d98f6fb88 | 540 | memcpy(ipDstPort,tempHold, 2); // dest <- tempHold |
| nixnax | 149:969d98f6fb88 | 541 | } |
| nixnax | 149:969d98f6fb88 | 542 | |
| nixnax | 146:a45f49a2b29c | 543 | /// Process an incoming UDP packet. |
| nixnax | 146:a45f49a2b29c | 544 | /// If the packet starts with the string "echo " or "test" we echo back a special packet |
| nixnax | 146:a45f49a2b29c | 545 | void UDPpacket() |
| nixnax | 146:a45f49a2b29c | 546 | { |
| nixnax | 146:a45f49a2b29c | 547 | char * ipHeader = ppp.pkt.buf+4; // udp packet start |
| nixnax | 146:a45f49a2b29c | 548 | char * ipSizeBuf = ipHeader+2; // size of IP packet |
| nixnax | 146:a45f49a2b29c | 549 | int headerSizeIP = 4*(ipHeader[0]&0xf); // size of IP header |
| nixnax | 146:a45f49a2b29c | 550 | char * udpHeader = ipHeader + headerSizeIP; // udp info start |
| nixnax | 146:a45f49a2b29c | 551 | char * udpLen = udpHeader+4; // udp data length |
| nixnax | 146:a45f49a2b29c | 552 | char * udpCheckSum = udpHeader+6; // udp checksum |
| nixnax | 146:a45f49a2b29c | 553 | char * udpData = udpHeader+8; // start of UDP data |
| nixnax | 146:a45f49a2b29c | 554 | int udpLength = ((udpLen[0]<<8) | udpLen[1]); // size of udp packet |
| nixnax | 146:a45f49a2b29c | 555 | int udpDataSize = udpLength - 8; // size of udp data |
| nixnax | 147:0f40005cbc5f | 556 | |
| nixnax | 146:a45f49a2b29c | 557 | #ifdef SERIAL_PORT_MONITOR_YES |
| nixnax | 147:0f40005cbc5f | 558 | char * srcIP = ipHeader+12; // IP source |
| nixnax | 147:0f40005cbc5f | 559 | char * dstIP = ipHeader+16; // IP destination |
| nixnax | 149:969d98f6fb88 | 560 | char * udpSrcPort = udpHeader+0; // source port |
| nixnax | 149:969d98f6fb88 | 561 | char * udpDstPort = udpHeader+2; // destination port |
| nixnax | 146:a45f49a2b29c | 562 | int udpSrc = (udpSrcPort[0]<<8)|udpSrcPort[1]; // integer of UDP source port |
| nixnax | 146:a45f49a2b29c | 563 | int udpDst = (udpDstPort[0]<<8)|udpDstPort[1]; // integer of UDP dest port |
| nixnax | 146:a45f49a2b29c | 564 | if(v0) debugPrintf("UDP %d.%d.%d.%d:%d ", srcIP[0],srcIP[1],srcIP[2],srcIP[3],udpSrc); |
| nixnax | 146:a45f49a2b29c | 565 | if(v0) debugPrintf("%d.%d.%d.%d:%d ", dstIP[0],dstIP[1],dstIP[2],dstIP[3],udpDst); |
| nixnax | 146:a45f49a2b29c | 566 | if(v0) debugPrintf("Len %03d", udpLength); |
| nixnax | 146:a45f49a2b29c | 567 | if (v1) { |
| nixnax | 146:a45f49a2b29c | 568 | int printSize = udpLength-8; |
| nixnax | 146:a45f49a2b29c | 569 | if (printSize > 20) printSize = 20; // print only first 20 characters |
| nixnax | 146:a45f49a2b29c | 570 | for (int i=0; i<printSize; i++) { |
| nixnax | 146:a45f49a2b29c | 571 | char ch = udpData[i]; |
| nixnax | 146:a45f49a2b29c | 572 | if (ch>31 && ch<127) { |
| nixnax | 146:a45f49a2b29c | 573 | debugPrintf("%c", ch); |
| nixnax | 146:a45f49a2b29c | 574 | } else { |
| nixnax | 146:a45f49a2b29c | 575 | debugPrintf("_"); |
| nixnax | 146:a45f49a2b29c | 576 | } |
| nixnax | 146:a45f49a2b29c | 577 | } |
| nixnax | 146:a45f49a2b29c | 578 | } |
| nixnax | 146:a45f49a2b29c | 579 | if (v0) debugPrintf("\n"); |
| nixnax | 146:a45f49a2b29c | 580 | #endif |
| nixnax | 146:a45f49a2b29c | 581 | int echoFound = !strncmp(udpData,"echo ",5); // true if UDP message starts with "echo " |
| nixnax | 146:a45f49a2b29c | 582 | int testFound = !strncmp(udpData,"test" ,4); // true if UDP message starts with "test" |
| nixnax | 146:a45f49a2b29c | 583 | if ( (echoFound) || (testFound)) { // if the UDP message starts with "echo " or "test" we answer back |
| nixnax | 147:0f40005cbc5f | 584 | swapIpAddresses(); // swap IP source and destination |
| nixnax | 149:969d98f6fb88 | 585 | swapIpPorts(); // swap IP source and destination ports |
| nixnax | 146:a45f49a2b29c | 586 | if (echoFound) { |
| nixnax | 146:a45f49a2b29c | 587 | memcpy(udpData,"Got{",4); // in the UDP data modify "echo" to "Got:" |
| nixnax | 146:a45f49a2b29c | 588 | char endString[] = "} UDP Server: PPP-Blinky\n"; // an appendix |
| nixnax | 146:a45f49a2b29c | 589 | memcpy(udpData+udpLength-8,endString,sizeof(endString)-1); // add endstring size to the UDP message |
| nixnax | 146:a45f49a2b29c | 590 | udpDataSize = udpDataSize + sizeof(endString)-1; // update udp data size with the size of the appendix |
| nixnax | 146:a45f49a2b29c | 591 | } |
| nixnax | 146:a45f49a2b29c | 592 | if (testFound) { |
| nixnax | 146:a45f49a2b29c | 593 | char udpResponse[50]; |
| nixnax | 146:a45f49a2b29c | 594 | int n = 0; |
| nixnax | 146:a45f49a2b29c | 595 | n = n+sprintf(udpResponse+n,"Response count %d\n",ppp.responseCounter++); |
| nixnax | 146:a45f49a2b29c | 596 | memcpy(udpData,udpResponse,n); // copy response to the UDP data area |
| nixnax | 146:a45f49a2b29c | 597 | udpDataSize = n; // new udp data size |
| nixnax | 146:a45f49a2b29c | 598 | } |
| nixnax | 146:a45f49a2b29c | 599 | udpLength = udpDataSize+8; // update udp packet length |
| nixnax | 146:a45f49a2b29c | 600 | int ipSize = headerSizeIP + udpLength; // update ip packet length |
| nixnax | 146:a45f49a2b29c | 601 | ppp.pkt.len = ipSize+2+4; // update ppp packet length |
| nixnax | 146:a45f49a2b29c | 602 | udpLen[0] = udpLength>>8; |
| nixnax | 146:a45f49a2b29c | 603 | udpLen[1] = udpLength; // update UDP length |
| nixnax | 146:a45f49a2b29c | 604 | ipSizeBuf[0] = ipSize>>8; |
| nixnax | 146:a45f49a2b29c | 605 | ipSizeBuf[1] = ipSize; // update IP length |
| nixnax | 146:a45f49a2b29c | 606 | IpHeaderCheckSum(); // update IP header checksum |
| nixnax | 146:a45f49a2b29c | 607 | memset(udpCheckSum,0,2); // we don't yet recompute the checksum (it's optional), so have to zero it |
| nixnax | 146:a45f49a2b29c | 608 | sendPppFrame(); // send the UDP message back |
| nixnax | 146:a45f49a2b29c | 609 | } |
| nixnax | 142:54d1543e23e5 | 610 | } |
| nixnax | 142:54d1543e23e5 | 611 | |
| nixnax | 142:54d1543e23e5 | 612 | /// handle a PING ICMP (internet control message protocol) packet |
| nixnax | 142:54d1543e23e5 | 613 | void ICMPpacket() // internet control message protocol |
| nixnax | 142:54d1543e23e5 | 614 | { |
| nixnax | 142:54d1543e23e5 | 615 | char * ipPkt = ppp.pkt.buf+4; // ip packet start |
| nixnax | 142:54d1543e23e5 | 616 | char * pktLen = ipPkt+2; |
| nixnax | 142:54d1543e23e5 | 617 | int packetLength = (pktLen[0]<<8) | pktLen[1]; // icmp packet length |
| nixnax | 142:54d1543e23e5 | 618 | int headerSizeIP = (( ipPkt[0]&0xf)*4); |
| nixnax | 142:54d1543e23e5 | 619 | char * icmpType = ipPkt + headerSizeIP; // icmp data start |
| nixnax | 142:54d1543e23e5 | 620 | char * icmpSum = icmpType+2; // icmp checksum |
| nixnax | 142:54d1543e23e5 | 621 | #define ICMP_TYPE_PING_REQUEST 8 |
| nixnax | 142:54d1543e23e5 | 622 | if ( icmpType[0] == ICMP_TYPE_PING_REQUEST ) { |
| nixnax | 142:54d1543e23e5 | 623 | char * ipTTL = ipPkt+8; // time to live |
| nixnax | 147:0f40005cbc5f | 624 | ipTTL[0]--; // decrement time to live (so we have to update header checksum) |
| nixnax | 147:0f40005cbc5f | 625 | #ifdef SERIAL_PORT_MONITOR_YES |
| nixnax | 142:54d1543e23e5 | 626 | char * srcAdr = ipPkt+12; |
| nixnax | 142:54d1543e23e5 | 627 | char * dstAdr = ipPkt+16; |
| nixnax | 142:54d1543e23e5 | 628 | int icmpIdent = (icmpType[4]<<8)|icmpType[5]; |
| nixnax | 142:54d1543e23e5 | 629 | int icmpSequence = (icmpType[6]<<8)|icmpType[7]; |
| nixnax | 142:54d1543e23e5 | 630 | if(1) { |
| nixnax | 142:54d1543e23e5 | 631 | char pbuf[50]; |
| nixnax | 142:54d1543e23e5 | 632 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 633 | sprintf(pbuf, "ICMP PING %d.%d.%d.%d %d.%d.%d.%d ", srcAdr[0],srcAdr[1],srcAdr[2],srcAdr[3],dstAdr[0],dstAdr[1],dstAdr[2],dstAdr[3]); |
| nixnax | 142:54d1543e23e5 | 634 | putsWhileCheckingInput( pbuf ); |
| nixnax | 142:54d1543e23e5 | 635 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 636 | sprintf(pbuf, "Ident %04x Sequence %04d \n",icmpIdent,icmpSequence); |
| nixnax | 142:54d1543e23e5 | 637 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 638 | putsWhileCheckingInput( pbuf ); |
| nixnax | 142:54d1543e23e5 | 639 | } |
| nixnax | 142:54d1543e23e5 | 640 | #endif |
| nixnax | 147:0f40005cbc5f | 641 | swapIpAddresses(); // swap the IP source and destination addresses |
| nixnax | 147:0f40005cbc5f | 642 | IpHeaderCheckSum(); // new ip header checksum (required because we changed TTL) |
| nixnax | 142:54d1543e23e5 | 643 | #define ICMP_TYPE_ECHO_REPLY 0 |
| nixnax | 142:54d1543e23e5 | 644 | icmpType[0]=ICMP_TYPE_ECHO_REPLY; // icmp echo reply |
| nixnax | 142:54d1543e23e5 | 645 | icmpSum[0]=0; |
| nixnax | 142:54d1543e23e5 | 646 | icmpSum[1]=0; // zero the checksum for recalculation |
| nixnax | 142:54d1543e23e5 | 647 | int icmpLength = packetLength - headerSizeIP; // length of ICMP data portion |
| nixnax | 142:54d1543e23e5 | 648 | unsigned int sum = dataCheckSum( (unsigned char *)icmpType, icmpLength); // this checksum on icmp data portion |
| nixnax | 142:54d1543e23e5 | 649 | icmpSum[0]=(sum>>8)&0xff; |
| nixnax | 142:54d1543e23e5 | 650 | icmpSum[1]=(sum )&0xff; // new checksum for ICMP data portion |
| nixnax | 142:54d1543e23e5 | 651 | |
| nixnax | 142:54d1543e23e5 | 652 | int printSize = icmpLength-8; // exclude size of icmp header |
| nixnax | 142:54d1543e23e5 | 653 | char * icmpData = icmpType+8; // the actual payload data is after the header |
| nixnax | 142:54d1543e23e5 | 654 | if (printSize > 10) printSize = 10; // print up to 20 characters |
| nixnax | 142:54d1543e23e5 | 655 | if (0) { |
| nixnax | 142:54d1543e23e5 | 656 | for (int i=0; i<printSize; i++) { |
| nixnax | 142:54d1543e23e5 | 657 | char ch = icmpData[i]; |
| nixnax | 142:54d1543e23e5 | 658 | if (ch>31 && ch<127) { |
| nixnax | 142:54d1543e23e5 | 659 | putcWhileCheckingInput(ch); |
| nixnax | 142:54d1543e23e5 | 660 | } else { |
| nixnax | 142:54d1543e23e5 | 661 | putcWhileCheckingInput('_'); |
| nixnax | 142:54d1543e23e5 | 662 | } |
| nixnax | 142:54d1543e23e5 | 663 | } |
| nixnax | 142:54d1543e23e5 | 664 | putcWhileCheckingInput('\n'); |
| nixnax | 142:54d1543e23e5 | 665 | } |
| nixnax | 144:01d98cf7738e | 666 | sendPppFrame(); // reply to the ping |
| nixnax | 142:54d1543e23e5 | 667 | } else { |
| nixnax | 142:54d1543e23e5 | 668 | if (v0) { |
| nixnax | 142:54d1543e23e5 | 669 | debugPrintf("ICMP type=%d \n", icmpType[0]); |
| nixnax | 142:54d1543e23e5 | 670 | } |
| nixnax | 142:54d1543e23e5 | 671 | } |
| nixnax | 142:54d1543e23e5 | 672 | } |
| nixnax | 142:54d1543e23e5 | 673 | |
| nixnax | 142:54d1543e23e5 | 674 | /// handle an IGMP (internet group managment protocol) packet (by ignoring it) |
| nixnax | 142:54d1543e23e5 | 675 | void IGMPpacket() |
| nixnax | 142:54d1543e23e5 | 676 | { |
| nixnax | 142:54d1543e23e5 | 677 | if (v0) debugPrintf("IGMP type=%d \n", ppp.pkt.buf[28]); |
| nixnax | 142:54d1543e23e5 | 678 | } |
| nixnax | 142:54d1543e23e5 | 679 | |
| nixnax | 142:54d1543e23e5 | 680 | /// dump the header of an IP pakcet on the (optional) debug serial port |
| nixnax | 142:54d1543e23e5 | 681 | void dumpHeaderIP (int outGoing) |
| nixnax | 142:54d1543e23e5 | 682 | { |
| nixnax | 142:54d1543e23e5 | 683 | #if defined(IP_HEADER_DUMP_YES) && defined(SERIAL_PORT_MONITOR_YES) |
| nixnax | 142:54d1543e23e5 | 684 | checkPc(); // we are expecting the first character of the next packet |
| nixnax | 142:54d1543e23e5 | 685 | char * ipPkt = ppp.pkt.buf+4; // ip packet start |
| nixnax | 142:54d1543e23e5 | 686 | char * ident = ipPkt+4; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 687 | #ifdef UNUSED_IP_VARIABLES |
| nixnax | 142:54d1543e23e5 | 688 | char * srcAdr = ipPkt+12; // 4 bytes |
| nixnax | 142:54d1543e23e5 | 689 | char * dstAdr = ipPkt+16; // 4 bytes = total of 20 bytes |
| nixnax | 142:54d1543e23e5 | 690 | char * version = ipPkt; // top 4 bits |
| nixnax | 142:54d1543e23e5 | 691 | char * ihl = ipPkt; // bottom 4 bits |
| nixnax | 142:54d1543e23e5 | 692 | char * dscp = ipPkt+1; // top 6 bits |
| nixnax | 142:54d1543e23e5 | 693 | char * ecn = ipPkt+1; // lower 2 bits |
| nixnax | 142:54d1543e23e5 | 694 | char * pktLen = ipPkt+2; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 695 | char * flags = ipPkt+6; // 2 bits |
| nixnax | 142:54d1543e23e5 | 696 | char * ttl = ipPkt+8; // 1 byte |
| nixnax | 142:54d1543e23e5 | 697 | char * protocol = ipPkt+9; // 1 byte |
| nixnax | 142:54d1543e23e5 | 698 | char * headercheck= ipPkt+10; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 699 | int versionIP = (version[0]>>4)&0xf; |
| nixnax | 142:54d1543e23e5 | 700 | int headerSizeIP = (ihl[0]&0xf)*4; |
| nixnax | 142:54d1543e23e5 | 701 | int dscpIP = (dscp[0]>>2)&0x3f; |
| nixnax | 142:54d1543e23e5 | 702 | int ecnIP = ecn[0]&3; |
| nixnax | 142:54d1543e23e5 | 703 | int packetLength = (pktLen[0]<<8)|pktLen[1]; // ip total packet length |
| nixnax | 142:54d1543e23e5 | 704 | int flagsIP = flags[0]>>14&3; |
| nixnax | 142:54d1543e23e5 | 705 | int ttlIP = ttl[0]; |
| nixnax | 142:54d1543e23e5 | 706 | int protocolIP = protocol[0]; |
| nixnax | 142:54d1543e23e5 | 707 | unsigned int checksumIP = (headercheck[0]<<8)|headercheck[1]; |
| nixnax | 142:54d1543e23e5 | 708 | #endif |
| nixnax | 142:54d1543e23e5 | 709 | int IPv4Id = (ident[0]<<8)|ident[1]; |
| nixnax | 142:54d1543e23e5 | 710 | char pbuf[50]; // local print buffer |
| nixnax | 142:54d1543e23e5 | 711 | int n=0; |
| nixnax | 142:54d1543e23e5 | 712 | n=n+sprintf(pbuf+n, outGoing ? "\x1b[34m" : "\x1b[30m" ); // VT100 color code, print black for incoming, blue for outgoing headers |
| nixnax | 142:54d1543e23e5 | 713 | n=n+sprintf(pbuf+n, "%05d ",IPv4Id); // IPv4Id is a good way to correlate our dumps with net monitor or wireshark traces |
| nixnax | 142:54d1543e23e5 | 714 | #define DUMP_FULL_IP_ADDRESS_YES |
| nixnax | 142:54d1543e23e5 | 715 | #ifdef DUMP_FULL_IP_ADDRESS_YES |
| nixnax | 142:54d1543e23e5 | 716 | char * srcAdr = ipPkt+12; // 4 bytes |
| nixnax | 142:54d1543e23e5 | 717 | char * dstAdr = ipPkt+16; // 4 bytes = total of 20 bytes |
| nixnax | 142:54d1543e23e5 | 718 | n=n+sprintf(pbuf+n, " %d.%d.%d.%d %d.%d.%d.%d ",srcAdr[0],srcAdr[1],srcAdr[2],srcAdr[3], dstAdr[0],dstAdr[1],dstAdr[2],dstAdr[3]); // full ip addresses |
| nixnax | 142:54d1543e23e5 | 719 | #endif |
| nixnax | 142:54d1543e23e5 | 720 | putsWhileCheckingInput( pbuf ); |
| nixnax | 142:54d1543e23e5 | 721 | #ifndef TCP_HEADER_DUMP_YES |
| nixnax | 142:54d1543e23e5 | 722 | putsWhileCheckingInput('\x1b[30m\n'); // there is no TCP header dump, so terminate the line with \n and VT100 code for black |
| nixnax | 142:54d1543e23e5 | 723 | #endif |
| nixnax | 142:54d1543e23e5 | 724 | #endif |
| nixnax | 142:54d1543e23e5 | 725 | } |
| nixnax | 142:54d1543e23e5 | 726 | |
| nixnax | 142:54d1543e23e5 | 727 | /// dump a TCP header on the optional debug serial port |
| nixnax | 142:54d1543e23e5 | 728 | void dumpHeaderTCP(int outGoing) |
| nixnax | 142:54d1543e23e5 | 729 | { |
| nixnax | 142:54d1543e23e5 | 730 | #if defined(TCP_HEADER_DUMP_YES) && defined(SERIAL_PORT_MONITOR_YES) |
| nixnax | 142:54d1543e23e5 | 731 | int headerSizeIP = (ppp.pkt.buf[4]&0xf)*4; // header size of ip portion |
| nixnax | 142:54d1543e23e5 | 732 | char * tcpStart = ppp.pkt.buf+4+headerSizeIP; // start of tcp packet |
| nixnax | 142:54d1543e23e5 | 733 | char * seqtcp = tcpStart + 4; // 4 bytes |
| nixnax | 142:54d1543e23e5 | 734 | char * acktcp = tcpStart + 8; // 4 bytes |
| nixnax | 142:54d1543e23e5 | 735 | char * flagbitstcp = tcpStart + 12; // 9 bits |
| nixnax | 142:54d1543e23e5 | 736 | unsigned int seq = (seqtcp[0]<<24)|(seqtcp[1]<<16)|(seqtcp[2]<<8)|(seqtcp[3]); |
| nixnax | 142:54d1543e23e5 | 737 | unsigned int ack = (acktcp[0]<<24)|(acktcp[1]<<16)|(acktcp[2]<<8)|(acktcp[3]); |
| nixnax | 142:54d1543e23e5 | 738 | if (seq && ack) {} // shut up the compiler about unused variables |
| nixnax | 142:54d1543e23e5 | 739 | int flags = ((flagbitstcp[0]&1)<<8)|flagbitstcp[1]; |
| nixnax | 142:54d1543e23e5 | 740 | char flagInfo[9]; // text string presenting the 8 most important TCP flags |
| nixnax | 142:54d1543e23e5 | 741 | #define PRINT_ALL_TCP_FLAGS_YES |
| nixnax | 142:54d1543e23e5 | 742 | #ifdef PRINT_ALL_TCP_FLAGS_YES |
| nixnax | 142:54d1543e23e5 | 743 | memset(flagInfo,'.', 8); // fill string with "........" |
| nixnax | 142:54d1543e23e5 | 744 | flagInfo[8]=0; // null terminate string |
| nixnax | 142:54d1543e23e5 | 745 | if (flags & (1<<0)) flagInfo[7]='F'; |
| nixnax | 142:54d1543e23e5 | 746 | if (flags & (1<<1)) flagInfo[6]='S'; |
| nixnax | 142:54d1543e23e5 | 747 | if (flags & (1<<2)) flagInfo[5]='R'; |
| nixnax | 142:54d1543e23e5 | 748 | if (flags & (1<<3)) flagInfo[4]='P'; |
| nixnax | 142:54d1543e23e5 | 749 | if (flags & (1<<4)) flagInfo[3]='A'; |
| nixnax | 142:54d1543e23e5 | 750 | if (flags & (1<<5)) flagInfo[2]='U'; |
| nixnax | 142:54d1543e23e5 | 751 | if (flags & (1<<6)) flagInfo[1]='E'; |
| nixnax | 142:54d1543e23e5 | 752 | if (flags & (1<<7)) flagInfo[0]='C'; |
| nixnax | 142:54d1543e23e5 | 753 | #else |
| nixnax | 142:54d1543e23e5 | 754 | if (flags & (1<<4)) flagInfo[0]='A'; // choose the most important flag to print |
| nixnax | 142:54d1543e23e5 | 755 | if (flags & (1<<1)) flagInfo[0]='S'; |
| nixnax | 142:54d1543e23e5 | 756 | if (flags & (1<<0)) flagInfo[0]='F'; |
| nixnax | 142:54d1543e23e5 | 757 | if (flags & (1<<3)) flagInfo[0]='P'; |
| nixnax | 142:54d1543e23e5 | 758 | if (flags & (1<<2)) flagInfo[0]='R'; |
| nixnax | 142:54d1543e23e5 | 759 | flagInfo[1]=0; // ' ' |
| nixnax | 142:54d1543e23e5 | 760 | flagInfo[2]=0; |
| nixnax | 142:54d1543e23e5 | 761 | #endif |
| nixnax | 142:54d1543e23e5 | 762 | putsWhileCheckingInput( flagInfo ); |
| nixnax | 142:54d1543e23e5 | 763 | #define EVERY_PACKET_ON_A_NEW_LINE_YES |
| nixnax | 142:54d1543e23e5 | 764 | #ifdef EVERY_PACKET_ON_A_NEW_LINE_YES |
| nixnax | 142:54d1543e23e5 | 765 | putsWhileCheckingInput("\x1b[30m\n"); // write a black color and newline after every packet |
| nixnax | 142:54d1543e23e5 | 766 | #endif |
| nixnax | 142:54d1543e23e5 | 767 | if( outGoing && ( flags == 0x11 ) ) { // ACK/FIN - if this is an outgoing ACK/FIN its the end of a tcp conversation |
| nixnax | 142:54d1543e23e5 | 768 | putcWhileCheckingInput('\n'); // insert an extra new line to mark the end of an HTTP the conversation |
| nixnax | 142:54d1543e23e5 | 769 | } |
| nixnax | 142:54d1543e23e5 | 770 | #endif |
| nixnax | 142:54d1543e23e5 | 771 | } |
| nixnax | 142:54d1543e23e5 | 772 | |
| nixnax | 143:c5019f856a56 | 773 | /// Encode a buffer in base-64 |
| nixnax | 142:54d1543e23e5 | 774 | void enc64(char * in, char * out, int len) |
| nixnax | 142:54d1543e23e5 | 775 | { |
| nixnax | 142:54d1543e23e5 | 776 | const static char lut [] = "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/="; |
| nixnax | 142:54d1543e23e5 | 777 | int i,j,a,b,c; |
| nixnax | 142:54d1543e23e5 | 778 | i=0; |
| nixnax | 142:54d1543e23e5 | 779 | j=0; |
| nixnax | 142:54d1543e23e5 | 780 | while(1) { |
| nixnax | 142:54d1543e23e5 | 781 | if (i<len) { |
| nixnax | 142:54d1543e23e5 | 782 | a = in[i++]; |
| nixnax | 142:54d1543e23e5 | 783 | out[j++] = lut[ ( (a >> 2) & 0x3f) ]; |
| nixnax | 142:54d1543e23e5 | 784 | } else break; |
| nixnax | 142:54d1543e23e5 | 785 | if (i<len) { |
| nixnax | 142:54d1543e23e5 | 786 | b = in[i++]; |
| nixnax | 142:54d1543e23e5 | 787 | out[j++] = lut[ ( (a << 4) & 0x30) | ( (b >> 4) & 0x0f) ]; |
| nixnax | 142:54d1543e23e5 | 788 | out[j++] = lut[ ( (b << 2) & 0x3c) ]; |
| nixnax | 142:54d1543e23e5 | 789 | } else out[j++] = '='; |
| nixnax | 142:54d1543e23e5 | 790 | if (i<len) { |
| nixnax | 142:54d1543e23e5 | 791 | c = in[i++]; |
| nixnax | 142:54d1543e23e5 | 792 | j--; |
| nixnax | 142:54d1543e23e5 | 793 | out[j++] = lut[ ( (b << 2) & 0x3c) | ( (c >> 6) & 0x03) ]; |
| nixnax | 142:54d1543e23e5 | 794 | out[j++] = lut[ ( (c >> 0) & 0x3f) ]; |
| nixnax | 142:54d1543e23e5 | 795 | } else out[j++] = '='; |
| nixnax | 142:54d1543e23e5 | 796 | } |
| nixnax | 142:54d1543e23e5 | 797 | out[j]=0; |
| nixnax | 142:54d1543e23e5 | 798 | } |
| nixnax | 142:54d1543e23e5 | 799 | |
| nixnax | 142:54d1543e23e5 | 800 | /// handle a request for an http websocket |
| nixnax | 142:54d1543e23e5 | 801 | /// we end up here if we enter the following javascript in a web browser console: x = new WebSocket("ws://172.10.10.2"); |
| nixnax | 142:54d1543e23e5 | 802 | int webSocketHandler(char * dataStart) |
| nixnax | 142:54d1543e23e5 | 803 | { |
| nixnax | 142:54d1543e23e5 | 804 | int n=0; // byte counter |
| nixnax | 142:54d1543e23e5 | 805 | char * key = strstr(dataStart, "Sec-WebSocket-Key: "); // search for the key in the payload |
| nixnax | 142:54d1543e23e5 | 806 | if (key != NULL) { |
| nixnax | 142:54d1543e23e5 | 807 | if (v0) putsWhileCheckingInput("WebSocket Request\n"); |
| nixnax | 142:54d1543e23e5 | 808 | char challenge [70]; |
| nixnax | 142:54d1543e23e5 | 809 | strncpy(challenge,key+19,70); // a local buffer |
| nixnax | 142:54d1543e23e5 | 810 | *strchr(challenge,'\r')=0; // insert null so we can use sprintf |
| nixnax | 142:54d1543e23e5 | 811 | strncat(challenge,"258EAFA5-E914-47DA-95CA-C5AB0DC85B11",70); // append websocket gui code |
| nixnax | 142:54d1543e23e5 | 812 | char shaOutput [20]; // sha1 output |
| nixnax | 142:54d1543e23e5 | 813 | sha1( shaOutput, challenge, strlen(challenge)); |
| nixnax | 142:54d1543e23e5 | 814 | char encOut[50]; |
| nixnax | 142:54d1543e23e5 | 815 | enc64( shaOutput, encOut, 20); |
| nixnax | 142:54d1543e23e5 | 816 | char * versionstring = strstr(dataStart, "Sec-WebSocket-Version:"); |
| nixnax | 142:54d1543e23e5 | 817 | char * version = challenge; |
| nixnax | 142:54d1543e23e5 | 818 | strncpy(version, versionstring,70); // copy version string |
| nixnax | 142:54d1543e23e5 | 819 | *strchr(version,'\r')=0; // null terminate so we can sprintf it |
| nixnax | 142:54d1543e23e5 | 820 | memset(dataStart,0,500); // blank out old data befor send the websocket response header |
| nixnax | 142:54d1543e23e5 | 821 | n=n+sprintf(dataStart+n, "HTTP/1.1 101 Switching Protocols\r\n"); |
| nixnax | 142:54d1543e23e5 | 822 | n=n+sprintf(dataStart+n, "Upgrade: websocket\r\n"); |
| nixnax | 142:54d1543e23e5 | 823 | n=n+sprintf(dataStart+n, "Connection: Upgrade\r\n"); |
| nixnax | 142:54d1543e23e5 | 824 | n=n+sprintf(dataStart+n, "Sec-WebSocket-Accept: %s\r\n",encOut); |
| nixnax | 142:54d1543e23e5 | 825 | n=n+sprintf(dataStart+n, "%s\r\n",version); |
| nixnax | 142:54d1543e23e5 | 826 | n=n+sprintf(dataStart+n, "mbed-Code: PPP-Blinky\r\n"); |
| nixnax | 142:54d1543e23e5 | 827 | n=n+sprintf(dataStart+n, "\r\n"); // websocket response header ending |
| nixnax | 142:54d1543e23e5 | 828 | } |
| nixnax | 142:54d1543e23e5 | 829 | return n; // this response should satisfy a web browser's websocket protocol request |
| nixnax | 142:54d1543e23e5 | 830 | } |
| nixnax | 142:54d1543e23e5 | 831 | |
| nixnax | 142:54d1543e23e5 | 832 | #define TCP_FLAG_ACK (1<<4) |
| nixnax | 142:54d1543e23e5 | 833 | #define TCP_FLAG_SYN (1<<1) |
| nixnax | 142:54d1543e23e5 | 834 | #define TCP_FLAG_PSH (1<<3) |
| nixnax | 142:54d1543e23e5 | 835 | #define TCP_FLAG_RST (1<<2) |
| nixnax | 142:54d1543e23e5 | 836 | #define TCP_FLAG_FIN (1<<0) |
| nixnax | 142:54d1543e23e5 | 837 | |
| nixnax | 142:54d1543e23e5 | 838 | /// respond to an HTTP request |
| nixnax | 142:54d1543e23e5 | 839 | int httpResponse(char * dataStart) |
| nixnax | 142:54d1543e23e5 | 840 | { |
| nixnax | 142:54d1543e23e5 | 841 | int n=0; // number of bytes we have printed so far |
| nixnax | 142:54d1543e23e5 | 842 | n = webSocketHandler( dataStart ); // test for and handle WebSocket upgrade requests |
| nixnax | 142:54d1543e23e5 | 843 | if (n>0) return n; // if it's a WebSocket we already have the response, so return |
| nixnax | 142:54d1543e23e5 | 844 | |
| nixnax | 142:54d1543e23e5 | 845 | int nHeader; // byte size of HTTP header |
| nixnax | 142:54d1543e23e5 | 846 | int contentLengthStart; // index where HTML starts |
| nixnax | 142:54d1543e23e5 | 847 | int httpGet5,httpGet6,httpGetx, httpGetRoot; // temporary storage of strncmp results |
| nixnax | 142:54d1543e23e5 | 848 | |
| nixnax | 146:a45f49a2b29c | 849 | ppp.responseCounter++; // increment the number of frames we have made |
| nixnax | 142:54d1543e23e5 | 850 | |
| nixnax | 142:54d1543e23e5 | 851 | httpGetRoot = strncmp(dataStart, "GET / HTTP/1.", 13); // found a GET to the root directory |
| nixnax | 142:54d1543e23e5 | 852 | httpGetx = strncmp(dataStart, "GET /x", 6); // found a GET to /x which we will treat special (anything starting with /x, e.g. /x, /xyz, /xABC?pqr=123 |
| nixnax | 142:54d1543e23e5 | 853 | httpGet5 = dataStart[5]; // the first character in the path name, we use it for special functions later on |
| nixnax | 142:54d1543e23e5 | 854 | httpGet6 = dataStart[6]; // the second character in the path name, we use it for special functions later on |
| nixnax | 142:54d1543e23e5 | 855 | // for example, you could try this using netcat (nc): echo "GET /x" | nc 172.10.10.2 |
| nixnax | 142:54d1543e23e5 | 856 | if( (httpGetRoot==0) || (httpGetx==0) ) { |
| nixnax | 142:54d1543e23e5 | 857 | n=n+sprintf(n+dataStart,"HTTP/1.1 200 OK\r\nServer: mbed-PPP-Blinky-v1\r\n"); // 200 OK header |
| nixnax | 142:54d1543e23e5 | 858 | } else { |
| nixnax | 142:54d1543e23e5 | 859 | n=n+sprintf(n+dataStart,"HTTP/1.1 404 Not Found\r\nServer: mbed-PPP-Blinky\r\n"); // 404 header |
| nixnax | 142:54d1543e23e5 | 860 | } |
| nixnax | 142:54d1543e23e5 | 861 | n=n+sprintf(n+dataStart,"Content-Length: "); // http header |
| nixnax | 142:54d1543e23e5 | 862 | contentLengthStart = n; // remember where Content-Length is in buffer |
| nixnax | 142:54d1543e23e5 | 863 | n=n+sprintf(n+dataStart,"?????\r\n"); // leave five spaces for content length - will be updated later |
| nixnax | 142:54d1543e23e5 | 864 | n=n+sprintf(n+dataStart,"Connection: close\r\n"); // close connection immediately |
| nixnax | 142:54d1543e23e5 | 865 | n=n+sprintf(n+dataStart,"Content-Type: text/html; charset=us-ascii\r\n\r\n"); // http header must end with empty line (\r\n) |
| nixnax | 142:54d1543e23e5 | 866 | nHeader=n; // size of HTTP header |
| nixnax | 142:54d1543e23e5 | 867 | if( httpGetRoot == 0 ) { |
| nixnax | 142:54d1543e23e5 | 868 | // this is where we insert our web page into the buffer |
| nixnax | 142:54d1543e23e5 | 869 | memcpy(n+dataStart,rootWebPage,sizeof(rootWebPage)); |
| nixnax | 142:54d1543e23e5 | 870 | n = n + sizeof(rootWebPage)-1; // one less than sizeof because we don't count the null byte at the end |
| nixnax | 142:54d1543e23e5 | 871 | } else if ( (httpGet5 == 'w') && (httpGet6 == 's') ) { // "ws" is a special page for websocket demo |
| nixnax | 142:54d1543e23e5 | 872 | memcpy(n+dataStart,webSocketPage,sizeof(webSocketPage)); |
| nixnax | 142:54d1543e23e5 | 873 | n = n + sizeof(webSocketPage)-1; // one less than size |
| nixnax | 142:54d1543e23e5 | 874 | } else { |
| nixnax | 142:54d1543e23e5 | 875 | if (httpGetx == 0) { // the page request started with "GET /x" - here we treat anything starting with /x special: |
| nixnax | 142:54d1543e23e5 | 876 | |
| nixnax | 142:54d1543e23e5 | 877 | #define W3C_COMPLIANT_RESPONSE_NO |
| nixnax | 142:54d1543e23e5 | 878 | // change the above to W3C_COMPLIANT_RESPONSE_YES if you want a W3C.org compliant HTTP response |
| nixnax | 142:54d1543e23e5 | 879 | #ifdef W3C_COMPLIANT_RESPONSE_YES |
| nixnax | 142:54d1543e23e5 | 880 | n=n+sprintf(n+dataStart,"<!DOCTYPE html><title>mbed PPP-Blinky</title>"); // html title (W3C.org required elements) |
| nixnax | 146:a45f49a2b29c | 881 | n=n+sprintf(n+dataStart,"<body>%d</body>",ppp.responseCounter); // body = the http frame count |
| nixnax | 142:54d1543e23e5 | 882 | #else |
| nixnax | 142:54d1543e23e5 | 883 | if( httpGet6 == 'b' ) { // if the fetched page is "xb" send a meta command to let the browser continuously reload |
| nixnax | 142:54d1543e23e5 | 884 | n=n+sprintf(n+dataStart, "<meta http-equiv=\"refresh\" content=\"0\">"); // reload loop - handy for benchmarking |
| nixnax | 142:54d1543e23e5 | 885 | } |
| nixnax | 142:54d1543e23e5 | 886 | // /x is a very short page, in fact, it is only a decimal number showing the http Page count |
| nixnax | 146:a45f49a2b29c | 887 | n=n+sprintf(n+dataStart,"%d ",ppp.responseCounter); // not really valid html but most browsers and curl are ok with it |
| nixnax | 142:54d1543e23e5 | 888 | #endif |
| nixnax | 142:54d1543e23e5 | 889 | } else { |
| nixnax | 142:54d1543e23e5 | 890 | // all other requests get 404 Not Found response with a http frame count - nice for debugging |
| nixnax | 142:54d1543e23e5 | 891 | n=n+sprintf(n+dataStart,"<!DOCTYPE html><title>mbed PPP-Blinky</title>"); // html title (required element) |
| nixnax | 142:54d1543e23e5 | 892 | n=n+sprintf(n+dataStart,"<body>Not Found</body>"); // not found message |
| nixnax | 142:54d1543e23e5 | 893 | } |
| nixnax | 142:54d1543e23e5 | 894 | } |
| nixnax | 142:54d1543e23e5 | 895 | #define CONTENTLENGTHSIZE 5 |
| nixnax | 142:54d1543e23e5 | 896 | char contentLengthString[CONTENTLENGTHSIZE+1]; |
| nixnax | 142:54d1543e23e5 | 897 | snprintf(contentLengthString,CONTENTLENGTHSIZE+1,"%*d",CONTENTLENGTHSIZE,n-nHeader); // print Content-Length with leading spaces and fixed width equal to csize |
| nixnax | 142:54d1543e23e5 | 898 | memcpy(dataStart+contentLengthStart, contentLengthString, CONTENTLENGTHSIZE); // copy Content-Length to it's place in the send buffer |
| nixnax | 142:54d1543e23e5 | 899 | return n; // total byte size of our response |
| nixnax | 142:54d1543e23e5 | 900 | } |
| nixnax | 142:54d1543e23e5 | 901 | |
| nixnax | 142:54d1543e23e5 | 902 | /// handle TCP data that is not an HTTP get |
| nixnax | 142:54d1543e23e5 | 903 | /// this is the response if we have TCP data but it's not an HTTP GET |
| nixnax | 142:54d1543e23e5 | 904 | /// this is handy when you for example want to use netcat (nc.exe) to talk to PPP-Blinky |
| nixnax | 142:54d1543e23e5 | 905 | /// this could also be a websocket receive event - especially if the first byte is 0x81 (websocket data push) |
| nixnax | 142:54d1543e23e5 | 906 | int tcpResponse(char * dataStart, int len, int * outFlags) |
| nixnax | 142:54d1543e23e5 | 907 | { |
| nixnax | 142:54d1543e23e5 | 908 | int n=0; // number of bytes we have printed so far |
| nixnax | 142:54d1543e23e5 | 909 | if (dataStart[0] == 0x81) { // check if this is a websocket push message |
| nixnax | 142:54d1543e23e5 | 910 | // this is most likely a websocket push message. you get this when you enter this in your browser console: x.send("my message"); |
| nixnax | 142:54d1543e23e5 | 911 | if (0) putsWhileCheckingInput( "Got data from websocket send()\n" ); |
| nixnax | 142:54d1543e23e5 | 912 | |
| nixnax | 142:54d1543e23e5 | 913 | // for now we simply echo the websocket data back to the client - the client should therefore see an onmessage event |
| nixnax | 142:54d1543e23e5 | 914 | // to display the echoed data in your browser, enter the following into the browser console: x.onmessage = function(msg){ console.log( msg.data ); } |
| nixnax | 142:54d1543e23e5 | 915 | if (1) { |
| nixnax | 142:54d1543e23e5 | 916 | char mask [4]; |
| nixnax | 142:54d1543e23e5 | 917 | memcpy ( mask, dataStart+2, 4); // websocket messages are "masked", so first we obtain the 4-byte mask |
| nixnax | 142:54d1543e23e5 | 918 | int websocketMessageSize = len - 6; // 1 byte prefix (0x81), 1 byte, 4 bytes mask = 6 bytes |
| nixnax | 142:54d1543e23e5 | 919 | if((dataStart[1]&0x80)==0x80) // test if the mask bit is set, which means all data is xor'ed with the mask |
| nixnax | 142:54d1543e23e5 | 920 | for (int i=0; i<websocketMessageSize; i++) dataStart[i+6]^= mask[i%4]; // unmask each byte with one of the mask bytes |
| nixnax | 142:54d1543e23e5 | 921 | dataStart[1] = len-2; // add four extra bytes to the message length because we don't use mask bytes for the send |
| nixnax | 142:54d1543e23e5 | 922 | memcpy(dataStart+2, "Got:",4); // insert our own text into the four mask bytes |
| nixnax | 142:54d1543e23e5 | 923 | n = len; // our response size remains exactly the same length as what we received |
| nixnax | 142:54d1543e23e5 | 924 | } |
| nixnax | 142:54d1543e23e5 | 925 | } else if ( (dataStart[0]==0x88) && (dataStart[1]==0x80) && (len == 6) ) { // test for a websocket close request |
| nixnax | 142:54d1543e23e5 | 926 | n=2; // our close command is only two bytes long because we don't use the four mask bytes |
| nixnax | 142:54d1543e23e5 | 927 | dataStart[1]=0; // we don't have mask bytes on |
| nixnax | 142:54d1543e23e5 | 928 | } else if (v1) putsWhileCheckingInput("TCP data received\n"); |
| nixnax | 142:54d1543e23e5 | 929 | return n; // total byte size of our response |
| nixnax | 142:54d1543e23e5 | 930 | } |
| nixnax | 142:54d1543e23e5 | 931 | |
| nixnax | 142:54d1543e23e5 | 932 | /// handle an incoming TCP packet |
| nixnax | 142:54d1543e23e5 | 933 | /// use the first few bytes to figure out if it's a websocket, an http request or just pure incoming TCP data |
| nixnax | 142:54d1543e23e5 | 934 | void tcpHandler() |
| nixnax | 142:54d1543e23e5 | 935 | { |
| nixnax | 142:54d1543e23e5 | 936 | // IP header |
| nixnax | 142:54d1543e23e5 | 937 | char * ipPkt = ppp.pkt.buf+4; // ip packet start |
| nixnax | 142:54d1543e23e5 | 938 | char * ihl = ipPkt; // bottom 4 bits |
| nixnax | 142:54d1543e23e5 | 939 | char * pktLen = ipPkt+2; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 940 | char * ident = ipPkt+4; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 941 | char * protocol = ipPkt+9; // 1 byte |
| nixnax | 149:969d98f6fb88 | 942 | //char * headercheck= ipPkt+10; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 943 | char * srcAdr = ipPkt+12; // 4 bytes |
| nixnax | 149:969d98f6fb88 | 944 | //char * dstAdr = ipPkt+16; // 4 bytes = total of 20 bytes |
| nixnax | 142:54d1543e23e5 | 945 | int headerSizeIP = (ihl[0]&0xf)*4; |
| nixnax | 142:54d1543e23e5 | 946 | int packetLength = (pktLen[0]<<8)|pktLen[1]; // ip total packet length |
| nixnax | 142:54d1543e23e5 | 947 | |
| nixnax | 142:54d1543e23e5 | 948 | // TCP header |
| nixnax | 142:54d1543e23e5 | 949 | char * tcp = ppp.pkt.buf+4+headerSizeIP; // start of tcp packet |
| nixnax | 149:969d98f6fb88 | 950 | //char * srctcp = tcp + 0; // 2 bytes |
| nixnax | 149:969d98f6fb88 | 951 | //char * dsttcp = tcp + 2; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 952 | char * seqtcp = tcp + 4; // 4 bytes |
| nixnax | 142:54d1543e23e5 | 953 | char * acktcp = tcp + 8; // 4 bytes |
| nixnax | 142:54d1543e23e5 | 954 | char * offset = tcp + 12; // 4 bits |
| nixnax | 142:54d1543e23e5 | 955 | char * flagbitstcp = tcp + 12; // 9 bits |
| nixnax | 142:54d1543e23e5 | 956 | char * windowsizetcp = tcp + 14; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 957 | char * checksumtcp = tcp + 16; // 2 bytes |
| nixnax | 142:54d1543e23e5 | 958 | |
| nixnax | 142:54d1543e23e5 | 959 | if(ident) {}; // shut up unused variable reference warning |
| nixnax | 142:54d1543e23e5 | 960 | int tcpSize = packetLength - headerSizeIP; |
| nixnax | 142:54d1543e23e5 | 961 | int headerSizeTCP = ((offset[0]>>4)&0x0f)*4; // size of tcp header only |
| nixnax | 142:54d1543e23e5 | 962 | int protocolIP = protocol[0]; |
| nixnax | 142:54d1543e23e5 | 963 | char * tcpDataIn = tcp + headerSizeTCP; // start of data block after TCP header |
| nixnax | 142:54d1543e23e5 | 964 | int tcpDataSize = tcpSize - headerSizeTCP; // size of data block after TCP header |
| nixnax | 142:54d1543e23e5 | 965 | char * tcpDataOut = tcp + 20; // start of outgoing data |
| nixnax | 142:54d1543e23e5 | 966 | unsigned int seq_in = (seqtcp[0]<<24)|(seqtcp[1]<<16)|(seqtcp[2]<<8)|(seqtcp[3]); |
| nixnax | 142:54d1543e23e5 | 967 | unsigned int ack_in = (acktcp[0]<<24)|(acktcp[1]<<16)|(acktcp[2]<<8)|(acktcp[3]); |
| nixnax | 142:54d1543e23e5 | 968 | unsigned int ack_out = seq_in + tcpDataSize; |
| nixnax | 142:54d1543e23e5 | 969 | unsigned int seq_out = ack_in; // use their version of our current sequence number |
| nixnax | 142:54d1543e23e5 | 970 | |
| nixnax | 142:54d1543e23e5 | 971 | // first we shorten the TCP response header to only 20 bytes. This means we ignore all TCP option requests |
| nixnax | 142:54d1543e23e5 | 972 | tcpSize = 20; // shorten total TCP packet size to 20 bytes (no data) |
| nixnax | 142:54d1543e23e5 | 973 | headerSizeTCP = 20; // shorten outgoing TCP header size 20 bytes |
| nixnax | 149:969d98f6fb88 | 974 | ipPkt[0] = 0x45; // short IP packet size to 45 |
| nixnax | 142:54d1543e23e5 | 975 | offset[0] = (headerSizeTCP/4)<<4; // shorten tcp header size to 20 bytes |
| nixnax | 142:54d1543e23e5 | 976 | packetLength = 40; // shorten total packet size to 40 bytes (20 ip + 20 tcp) |
| nixnax | 142:54d1543e23e5 | 977 | pktLen[1] = 40; // set total packet size to 40 bytes (20 ip + 20 tcp) |
| nixnax | 142:54d1543e23e5 | 978 | pktLen[0] = 0; // set total packet size to 40 bytes (20 ip + 20 tcp) |
| nixnax | 142:54d1543e23e5 | 979 | |
| nixnax | 142:54d1543e23e5 | 980 | int dataLen = 0; // most of our responses will have zero TCP data, only a header |
| nixnax | 142:54d1543e23e5 | 981 | int flagsOut = TCP_FLAG_ACK; // the default case is an ACK packet |
| nixnax | 142:54d1543e23e5 | 982 | int flagsTCP = ((flagbitstcp[0]&1)<<8)|flagbitstcp[1]; // the tcp flags we received |
| nixnax | 142:54d1543e23e5 | 983 | windowsizetcp[0] = (700 >> 8 ); // tcp window size hi byte |
| nixnax | 142:54d1543e23e5 | 984 | windowsizetcp[1] = (700 & 0xff); // tcp window size lo byte |
| nixnax | 142:54d1543e23e5 | 985 | |
| nixnax | 142:54d1543e23e5 | 986 | // A sparse TCP flag interpreter that implements stateless TCP connections |
| nixnax | 142:54d1543e23e5 | 987 | |
| nixnax | 142:54d1543e23e5 | 988 | switch ( flagsTCP ) { |
| nixnax | 142:54d1543e23e5 | 989 | case TCP_FLAG_ACK: |
| nixnax | 142:54d1543e23e5 | 990 | return; |
| nixnax | 142:54d1543e23e5 | 991 | case TCP_FLAG_SYN: |
| nixnax | 142:54d1543e23e5 | 992 | flagsOut = TCP_FLAG_SYN | TCP_FLAG_ACK; // something wants to connect - acknowledge it |
| nixnax | 142:54d1543e23e5 | 993 | seq_out = seq_in+0x10000000U; // create a new sequence number using their sequence as a starting point, increase the highest digit |
| nixnax | 142:54d1543e23e5 | 994 | ack_out++; // for SYN flag we have to increase the sequence by 1 |
| nixnax | 142:54d1543e23e5 | 995 | break; |
| nixnax | 142:54d1543e23e5 | 996 | case TCP_FLAG_ACK | TCP_FLAG_PSH: |
| nixnax | 142:54d1543e23e5 | 997 | if ( (strncmp(tcpDataIn, "GET /", 5) == 0) ) { // check for an http GET command |
| nixnax | 142:54d1543e23e5 | 998 | flagsOut = TCP_FLAG_ACK | TCP_FLAG_PSH; // set outgoing FIN flag to ask them to close from their side |
| nixnax | 142:54d1543e23e5 | 999 | dataLen = httpResponse(tcpDataOut); // send an http response |
| nixnax | 142:54d1543e23e5 | 1000 | } else { |
| nixnax | 142:54d1543e23e5 | 1001 | dataLen = tcpResponse(tcpDataOut,tcpDataSize, &flagsOut); // not a web request, send a packet reporting number of received bytes |
| nixnax | 142:54d1543e23e5 | 1002 | } |
| nixnax | 142:54d1543e23e5 | 1003 | break; |
| nixnax | 142:54d1543e23e5 | 1004 | case TCP_FLAG_FIN: |
| nixnax | 142:54d1543e23e5 | 1005 | case TCP_FLAG_FIN | TCP_FLAG_ACK: |
| nixnax | 142:54d1543e23e5 | 1006 | case TCP_FLAG_FIN | TCP_FLAG_PSH | TCP_FLAG_ACK: |
| nixnax | 142:54d1543e23e5 | 1007 | flagsOut = TCP_FLAG_ACK | TCP_FLAG_FIN; // set outgoing FIN flag to ask them to close from their side |
| nixnax | 142:54d1543e23e5 | 1008 | ack_out++; // for FIN flag we have to increase the sequence by 1 |
| nixnax | 142:54d1543e23e5 | 1009 | break; |
| nixnax | 142:54d1543e23e5 | 1010 | default: |
| nixnax | 142:54d1543e23e5 | 1011 | return; // ignore remaining packets |
| nixnax | 142:54d1543e23e5 | 1012 | } // switch |
| nixnax | 142:54d1543e23e5 | 1013 | |
| nixnax | 142:54d1543e23e5 | 1014 | // The TCP flag handling is now done |
| nixnax | 142:54d1543e23e5 | 1015 | // first we swap source and destination TCP addresses and insert the new ack and seq numbers |
| nixnax | 147:0f40005cbc5f | 1016 | swapIpAddresses(); // swap IP source and destination addresses |
| nixnax | 149:969d98f6fb88 | 1017 | swapIpPorts(); // swap IP source and destination ports |
| nixnax | 142:54d1543e23e5 | 1018 | |
| nixnax | 142:54d1543e23e5 | 1019 | acktcp[0]=ack_out>>24; |
| nixnax | 142:54d1543e23e5 | 1020 | acktcp[1]=ack_out>>16; |
| nixnax | 142:54d1543e23e5 | 1021 | acktcp[2]=ack_out>>8; |
| nixnax | 142:54d1543e23e5 | 1022 | acktcp[3]=ack_out>>0; // save ack 32-bit integer |
| nixnax | 142:54d1543e23e5 | 1023 | seqtcp[0]=seq_out>>24; |
| nixnax | 142:54d1543e23e5 | 1024 | seqtcp[1]=seq_out>>16; |
| nixnax | 142:54d1543e23e5 | 1025 | seqtcp[2]=seq_out>>8; |
| nixnax | 142:54d1543e23e5 | 1026 | seqtcp[3]=seq_out>>0; // save seq 32-bit integer |
| nixnax | 142:54d1543e23e5 | 1027 | |
| nixnax | 142:54d1543e23e5 | 1028 | flagbitstcp[1] = flagsOut; // update the TCP flags |
| nixnax | 142:54d1543e23e5 | 1029 | |
| nixnax | 142:54d1543e23e5 | 1030 | // increment our outgoing ip packet counter |
| nixnax | 142:54d1543e23e5 | 1031 | ppp.ip.ident++; // get next ident number for our packet |
| nixnax | 142:54d1543e23e5 | 1032 | |
| nixnax | 142:54d1543e23e5 | 1033 | // Now we recalculate all the header sizes |
| nixnax | 142:54d1543e23e5 | 1034 | tcpSize = headerSizeTCP + dataLen; // tcp packet size |
| nixnax | 142:54d1543e23e5 | 1035 | int newPacketSize = headerSizeIP + tcpSize; // calculate size of the outgoing packet |
| nixnax | 142:54d1543e23e5 | 1036 | pktLen[0] = (newPacketSize>>8); |
| nixnax | 142:54d1543e23e5 | 1037 | pktLen[1]=newPacketSize; // ip total packet size |
| nixnax | 142:54d1543e23e5 | 1038 | ppp.pkt.len = newPacketSize+4+2; // ip packet length + 4-byte ppp prefix (ff 03 00 21) + 2 fcs (crc) bytes bytes at the end of the packet |
| nixnax | 142:54d1543e23e5 | 1039 | |
| nixnax | 142:54d1543e23e5 | 1040 | // the header is all set up, now do the IP and TCP checksums |
| nixnax | 146:a45f49a2b29c | 1041 | IpHeaderCheckSum(); // calculate new IP header checksum |
| nixnax | 142:54d1543e23e5 | 1042 | |
| nixnax | 142:54d1543e23e5 | 1043 | // now we have to build the so-called 12-byte TCP "pseudo-header" in front of the TCP header (containing some IP header values) in order to correctly calculate the TCP checksum |
| nixnax | 142:54d1543e23e5 | 1044 | // this header contains the most important parts of the IP header, i.e. source and destination address, protocol number and data length. |
| nixnax | 149:969d98f6fb88 | 1045 | char tempHold[12]; // it's 12 long because we later reuse it when building the TCP pseudo-header |
| nixnax | 142:54d1543e23e5 | 1046 | char * pseudoHeader = tcp-12; // mark the start of the TCP pseudo-header |
| nixnax | 142:54d1543e23e5 | 1047 | memcpy(tempHold, pseudoHeader, 12); // preserve the 12 bytes of the IP header where the TCP pseudo-Header will be built |
| nixnax | 142:54d1543e23e5 | 1048 | memcpy( pseudoHeader+0, srcAdr, 8); // IP source and destination addresses from IP header |
| nixnax | 142:54d1543e23e5 | 1049 | memset( pseudoHeader+8, 0, 1); // reserved, set to zero |
| nixnax | 142:54d1543e23e5 | 1050 | memset( pseudoHeader+9, protocolIP, 1); // protocol from IP header |
| nixnax | 142:54d1543e23e5 | 1051 | memset( pseudoHeader+10, tcpSize>>8, 1); // size of IP data (TCP packet size) |
| nixnax | 142:54d1543e23e5 | 1052 | memset( pseudoHeader+11, tcpSize, 1); // size of IP data (TCP packet size) |
| nixnax | 142:54d1543e23e5 | 1053 | // pseudo-header built, now we can calculate TCP checksum |
| nixnax | 142:54d1543e23e5 | 1054 | checksumtcp[0]=0; |
| nixnax | 142:54d1543e23e5 | 1055 | checksumtcp[1]=0; |
| nixnax | 142:54d1543e23e5 | 1056 | unsigned int pseudoHeaderSum=dataCheckSum((unsigned char *)pseudoHeader,tcpSize+12); // calculate the TCP checksum starting at the pseudo-header |
| nixnax | 142:54d1543e23e5 | 1057 | checksumtcp[0]=pseudoHeaderSum>>8; |
| nixnax | 142:54d1543e23e5 | 1058 | checksumtcp[1]=pseudoHeaderSum; |
| nixnax | 142:54d1543e23e5 | 1059 | memcpy( tcp-12, tempHold, 12); // restore the 12 bytes that the pseudo-header overwrote |
| nixnax | 147:0f40005cbc5f | 1060 | // IP and TCP checksums done |
| nixnax | 142:54d1543e23e5 | 1061 | dumpHeaderIP(1); // dump outgoing IP header |
| nixnax | 142:54d1543e23e5 | 1062 | dumpHeaderTCP(1); // dump outgoing TCP header |
| nixnax | 142:54d1543e23e5 | 1063 | for (int i=0; i<45*1000/10; i++) { // 45 ms delay before sending frame - a typical internet delay time |
| nixnax | 142:54d1543e23e5 | 1064 | checkPc(); // catch any incoming characters |
| nixnax | 142:54d1543e23e5 | 1065 | wait_us(10); // wait less than 1 character duration at 115200 |
| nixnax | 142:54d1543e23e5 | 1066 | } |
| nixnax | 144:01d98cf7738e | 1067 | sendPppFrame(); // All preparation complete - send the TCP response |
| nixnax | 142:54d1543e23e5 | 1068 | if(0) dumpPPPFrame(); // set to 1 to dump transmitted ppp frame |
| nixnax | 142:54d1543e23e5 | 1069 | memset(ppp.pkt.buf+44,0,500); // flush out traces of previous data that we may scan for |
| nixnax | 142:54d1543e23e5 | 1070 | } |
| nixnax | 142:54d1543e23e5 | 1071 | |
| nixnax | 142:54d1543e23e5 | 1072 | |
| nixnax | 142:54d1543e23e5 | 1073 | /// dump the TCP data to the debug serial port |
| nixnax | 142:54d1543e23e5 | 1074 | void dumpDataTCP() |
| nixnax | 142:54d1543e23e5 | 1075 | { |
| nixnax | 142:54d1543e23e5 | 1076 | int ipPktLen = (ppp.pkt.buf[6]<<8)|ppp.pkt.buf[7]; // overall length of ip packet |
| nixnax | 142:54d1543e23e5 | 1077 | int ipHeaderLen = (ppp.pkt.buf[4]&0xf)*4; // length of ip header |
| nixnax | 142:54d1543e23e5 | 1078 | int headerSizeTCP = ((ppp.pkt.buf[4+ipHeaderLen+12]>>4)&0xf)*4;; // length of tcp header |
| nixnax | 142:54d1543e23e5 | 1079 | int dataLen = ipPktLen - ipHeaderLen - headerSizeTCP; // data is what's left after the two headers |
| nixnax | 142:54d1543e23e5 | 1080 | if (v1) { |
| nixnax | 142:54d1543e23e5 | 1081 | char pbuf[50]; // local print buffer |
| nixnax | 142:54d1543e23e5 | 1082 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 1083 | sprintf(pbuf, "TCP %d ipHeader %d tcpHeader %d Data %d\n", ipPktLen, ipHeaderLen, headerSizeTCP, dataLen); // 1 for more verbose |
| nixnax | 142:54d1543e23e5 | 1084 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 1085 | putsWhileCheckingInput( pbuf ); |
| nixnax | 142:54d1543e23e5 | 1086 | } |
| nixnax | 142:54d1543e23e5 | 1087 | if (dataLen > 0) { |
| nixnax | 142:54d1543e23e5 | 1088 | ppp.pkt.buf[4+ipHeaderLen+headerSizeTCP+dataLen]=0; // insert a null after the data so debug printf stops printing after the data |
| nixnax | 142:54d1543e23e5 | 1089 | putsWhileCheckingInput( ppp.pkt.buf+4+ipHeaderLen+headerSizeTCP ); // print the tcp payload data |
| nixnax | 142:54d1543e23e5 | 1090 | putsWhileCheckingInput("\n"); |
| nixnax | 142:54d1543e23e5 | 1091 | } |
| nixnax | 142:54d1543e23e5 | 1092 | } |
| nixnax | 142:54d1543e23e5 | 1093 | |
| nixnax | 142:54d1543e23e5 | 1094 | /// handle an incoming TCP packet |
| nixnax | 142:54d1543e23e5 | 1095 | void TCPpacket() |
| nixnax | 142:54d1543e23e5 | 1096 | { |
| nixnax | 142:54d1543e23e5 | 1097 | dumpHeaderIP(0); // dump incoming packet header |
| nixnax | 142:54d1543e23e5 | 1098 | dumpHeaderTCP(0); // dump incoming packet header |
| nixnax | 142:54d1543e23e5 | 1099 | if (v2) dumpDataTCP(); |
| nixnax | 142:54d1543e23e5 | 1100 | tcpHandler(); |
| nixnax | 142:54d1543e23e5 | 1101 | } |
| nixnax | 142:54d1543e23e5 | 1102 | |
| nixnax | 142:54d1543e23e5 | 1103 | /// handle the remaining IP protocols by ignoring them |
| nixnax | 142:54d1543e23e5 | 1104 | void otherProtocol() |
| nixnax | 142:54d1543e23e5 | 1105 | { |
| nixnax | 142:54d1543e23e5 | 1106 | debugPrintf("Other IP protocol"); |
| nixnax | 142:54d1543e23e5 | 1107 | } |
| nixnax | 142:54d1543e23e5 | 1108 | |
| nixnax | 142:54d1543e23e5 | 1109 | /// process an incoming IP packet |
| nixnax | 142:54d1543e23e5 | 1110 | void IPframe() |
| nixnax | 142:54d1543e23e5 | 1111 | { |
| nixnax | 142:54d1543e23e5 | 1112 | int protocol = ppp.pkt.buf[13]; |
| nixnax | 142:54d1543e23e5 | 1113 | switch (protocol) { |
| nixnax | 142:54d1543e23e5 | 1114 | case 1: |
| nixnax | 142:54d1543e23e5 | 1115 | ICMPpacket(); |
| nixnax | 142:54d1543e23e5 | 1116 | break; |
| nixnax | 142:54d1543e23e5 | 1117 | case 2: |
| nixnax | 142:54d1543e23e5 | 1118 | IGMPpacket(); |
| nixnax | 142:54d1543e23e5 | 1119 | break; |
| nixnax | 142:54d1543e23e5 | 1120 | case 17: |
| nixnax | 142:54d1543e23e5 | 1121 | UDPpacket(); |
| nixnax | 142:54d1543e23e5 | 1122 | break; |
| nixnax | 142:54d1543e23e5 | 1123 | case 6: |
| nixnax | 142:54d1543e23e5 | 1124 | TCPpacket(); |
| nixnax | 142:54d1543e23e5 | 1125 | break; |
| nixnax | 142:54d1543e23e5 | 1126 | default: |
| nixnax | 142:54d1543e23e5 | 1127 | otherProtocol(); |
| nixnax | 142:54d1543e23e5 | 1128 | } |
| nixnax | 142:54d1543e23e5 | 1129 | } |
| nixnax | 142:54d1543e23e5 | 1130 | |
| nixnax | 142:54d1543e23e5 | 1131 | /// respond to LCP (line configuration protocol) configuration request) by allowing no options |
| nixnax | 142:54d1543e23e5 | 1132 | void LCPconfReq() |
| nixnax | 142:54d1543e23e5 | 1133 | { |
| nixnax | 142:54d1543e23e5 | 1134 | debugPrintf("LCP Config "); |
| nixnax | 142:54d1543e23e5 | 1135 | if (ppp.pkt.buf[7] != 4) { |
| nixnax | 142:54d1543e23e5 | 1136 | ppp.pkt.buf[4]=4; // allow only "no options" which means Maximum Receive Unit (MRU) is default 1500 bytes |
| nixnax | 142:54d1543e23e5 | 1137 | debugPrintf("Reject\n"); |
| nixnax | 144:01d98cf7738e | 1138 | sendPppFrame(); |
| nixnax | 142:54d1543e23e5 | 1139 | } else { |
| nixnax | 142:54d1543e23e5 | 1140 | ppp.pkt.buf[4]=2; // ack zero conf |
| nixnax | 142:54d1543e23e5 | 1141 | debugPrintf("Ack\n"); |
| nixnax | 144:01d98cf7738e | 1142 | sendPppFrame(); |
| nixnax | 142:54d1543e23e5 | 1143 | debugPrintf("LCP Ask\n"); |
| nixnax | 142:54d1543e23e5 | 1144 | ppp.pkt.buf[4]=1; // request no options |
| nixnax | 144:01d98cf7738e | 1145 | sendPppFrame(); |
| nixnax | 142:54d1543e23e5 | 1146 | } |
| nixnax | 142:54d1543e23e5 | 1147 | } |
| nixnax | 142:54d1543e23e5 | 1148 | |
| nixnax | 142:54d1543e23e5 | 1149 | /// handle LCP acknowledge packets by ignoring them |
| nixnax | 142:54d1543e23e5 | 1150 | void LCPconfAck() |
| nixnax | 142:54d1543e23e5 | 1151 | { |
| nixnax | 142:54d1543e23e5 | 1152 | debugPrintf("LCP Ack\n"); |
| nixnax | 142:54d1543e23e5 | 1153 | } |
| nixnax | 142:54d1543e23e5 | 1154 | |
| nixnax | 143:c5019f856a56 | 1155 | /// handle LCP end (disconnect) packets by acknowledging them and by setting ppp.online to false |
| nixnax | 142:54d1543e23e5 | 1156 | void LCPend() |
| nixnax | 142:54d1543e23e5 | 1157 | { |
| nixnax | 142:54d1543e23e5 | 1158 | ppp.pkt.buf[4]=6; |
| nixnax | 144:01d98cf7738e | 1159 | sendPppFrame(); // acknowledge |
| nixnax | 142:54d1543e23e5 | 1160 | ppp.online=0; // start hunting for connect string again |
| nixnax | 142:54d1543e23e5 | 1161 | pppInitStruct(); // flush the receive buffer |
| nixnax | 143:c5019f856a56 | 1162 | debugPrintf("LCP End (Disconnect from host)\n"); |
| nixnax | 142:54d1543e23e5 | 1163 | } |
| nixnax | 142:54d1543e23e5 | 1164 | |
| nixnax | 142:54d1543e23e5 | 1165 | /// respond to other LCP requests by ignoring them |
| nixnax | 142:54d1543e23e5 | 1166 | void LCPother() |
| nixnax | 142:54d1543e23e5 | 1167 | { |
| nixnax | 142:54d1543e23e5 | 1168 | debugPrintf("LCP Other\n"); |
| nixnax | 142:54d1543e23e5 | 1169 | dumpPPPFrame(); |
| nixnax | 142:54d1543e23e5 | 1170 | } |
| nixnax | 142:54d1543e23e5 | 1171 | |
| nixnax | 142:54d1543e23e5 | 1172 | /// process incoming LCP packets |
| nixnax | 142:54d1543e23e5 | 1173 | void LCPframe() |
| nixnax | 142:54d1543e23e5 | 1174 | { |
| nixnax | 142:54d1543e23e5 | 1175 | int code = ppp.pkt.buf[4]; |
| nixnax | 142:54d1543e23e5 | 1176 | switch (code) { |
| nixnax | 142:54d1543e23e5 | 1177 | case 1: |
| nixnax | 142:54d1543e23e5 | 1178 | LCPconfReq(); |
| nixnax | 142:54d1543e23e5 | 1179 | break; // config request |
| nixnax | 142:54d1543e23e5 | 1180 | case 2: |
| nixnax | 142:54d1543e23e5 | 1181 | LCPconfAck(); |
| nixnax | 142:54d1543e23e5 | 1182 | break; // config ack |
| nixnax | 142:54d1543e23e5 | 1183 | case 5: |
| nixnax | 142:54d1543e23e5 | 1184 | LCPend(); |
| nixnax | 142:54d1543e23e5 | 1185 | break; // end connection |
| nixnax | 142:54d1543e23e5 | 1186 | default: |
| nixnax | 142:54d1543e23e5 | 1187 | LCPother(); |
| nixnax | 142:54d1543e23e5 | 1188 | } |
| nixnax | 142:54d1543e23e5 | 1189 | } |
| nixnax | 142:54d1543e23e5 | 1190 | |
| nixnax | 142:54d1543e23e5 | 1191 | /// discard packets that are not IP, IPCP, or LCP |
| nixnax | 142:54d1543e23e5 | 1192 | void discardedFrame() |
| nixnax | 142:54d1543e23e5 | 1193 | { |
| nixnax | 142:54d1543e23e5 | 1194 | if (v0) debugPrintf("Frame is not IP, IPCP or LCP: %02x %02x %02x %02x\n", ppp.pkt.buf[0],ppp.pkt.buf[1],ppp.pkt.buf[2],ppp.pkt.buf[3]); |
| nixnax | 142:54d1543e23e5 | 1195 | } |
| nixnax | 142:54d1543e23e5 | 1196 | |
| nixnax | 142:54d1543e23e5 | 1197 | /// determine the packet type (IP, IPCP or LCP) of incoming packets |
| nixnax | 142:54d1543e23e5 | 1198 | void determinePacketType() |
| nixnax | 142:54d1543e23e5 | 1199 | { |
| nixnax | 142:54d1543e23e5 | 1200 | if ( ppp.pkt.buf[0] != 0xff ) { |
| nixnax | 142:54d1543e23e5 | 1201 | debugPrintf("byte0 != ff\n"); |
| nixnax | 142:54d1543e23e5 | 1202 | return; |
| nixnax | 142:54d1543e23e5 | 1203 | } |
| nixnax | 142:54d1543e23e5 | 1204 | if ( ppp.pkt.buf[1] != 3 ) { |
| nixnax | 142:54d1543e23e5 | 1205 | debugPrintf("byte1 != 3\n"); |
| nixnax | 142:54d1543e23e5 | 1206 | return; |
| nixnax | 142:54d1543e23e5 | 1207 | } |
| nixnax | 142:54d1543e23e5 | 1208 | if ( ppp.pkt.buf[3] != 0x21 ) { |
| nixnax | 142:54d1543e23e5 | 1209 | debugPrintf("byte2 != 21\n"); |
| nixnax | 142:54d1543e23e5 | 1210 | return; |
| nixnax | 142:54d1543e23e5 | 1211 | } |
| nixnax | 142:54d1543e23e5 | 1212 | int packetType = ppp.pkt.buf[2]; |
| nixnax | 142:54d1543e23e5 | 1213 | switch (packetType) { |
| nixnax | 142:54d1543e23e5 | 1214 | case 0xc0: |
| nixnax | 142:54d1543e23e5 | 1215 | LCPframe(); |
| nixnax | 142:54d1543e23e5 | 1216 | break; // link control |
| nixnax | 142:54d1543e23e5 | 1217 | case 0x80: |
| nixnax | 142:54d1543e23e5 | 1218 | IPCPframe(); |
| nixnax | 142:54d1543e23e5 | 1219 | break; // IP control |
| nixnax | 142:54d1543e23e5 | 1220 | case 0x00: |
| nixnax | 142:54d1543e23e5 | 1221 | IPframe(); |
| nixnax | 142:54d1543e23e5 | 1222 | break; // IP itself |
| nixnax | 142:54d1543e23e5 | 1223 | default: |
| nixnax | 142:54d1543e23e5 | 1224 | discardedFrame(); |
| nixnax | 142:54d1543e23e5 | 1225 | } |
| nixnax | 142:54d1543e23e5 | 1226 | } |
| nixnax | 142:54d1543e23e5 | 1227 | |
| nixnax | 146:a45f49a2b29c | 1228 | /// a sniffer tool to assist in figuring out where in the code we are having characters in the input buffer |
| nixnax | 146:a45f49a2b29c | 1229 | void sniff() |
| nixnax | 146:a45f49a2b29c | 1230 | { |
| nixnax | 146:a45f49a2b29c | 1231 | if ( pc.readable() ) putsWhileCheckingInput( "Sniff - Char available!\n" ); // if this prints anything it means there is a character in the serial receive buffer |
| nixnax | 146:a45f49a2b29c | 1232 | } |
| nixnax | 146:a45f49a2b29c | 1233 | |
| nixnax | 142:54d1543e23e5 | 1234 | /// scan the PPP serial input stream for frame start markers |
| nixnax | 143:c5019f856a56 | 1235 | void waitForPppFrame() |
| nixnax | 142:54d1543e23e5 | 1236 | { |
| nixnax | 142:54d1543e23e5 | 1237 | while(1) { |
| nixnax | 142:54d1543e23e5 | 1238 | checkPc(); // handle received characters |
| nixnax | 142:54d1543e23e5 | 1239 | if ( ppp.rx.head != ppp.rx.tail ) { |
| nixnax | 142:54d1543e23e5 | 1240 | int oldTail = ppp.rx.tail; // remember where the character is located in the buffer |
| nixnax | 142:54d1543e23e5 | 1241 | int rx = pc_getBuf(); // get the character |
| nixnax | 142:54d1543e23e5 | 1242 | if (rx==FRAME_7E) { |
| nixnax | 142:54d1543e23e5 | 1243 | if (ppp.firstFrame) { // is this the start of the first frame start |
| nixnax | 142:54d1543e23e5 | 1244 | ppp.firstFrame=0; |
| nixnax | 142:54d1543e23e5 | 1245 | ppp.rx.rtail = ppp.rx.tail; // update real-time tail with the virtual tail |
| nixnax | 142:54d1543e23e5 | 1246 | ppp.hdlc.frameStartIndex = ppp.rx.tail; // remember where first frame started |
| nixnax | 142:54d1543e23e5 | 1247 | } else { |
| nixnax | 142:54d1543e23e5 | 1248 | ppp.hdlc.frameEndIndex=oldTail; // mark the frame end character |
| nixnax | 142:54d1543e23e5 | 1249 | processPPPFrame(ppp.hdlc.frameStartIndex, ppp.hdlc.frameEndIndex); // process the frame |
| nixnax | 142:54d1543e23e5 | 1250 | ppp.rx.rtail = ppp.rx.tail; // update real-time tail with the virtual tail |
| nixnax | 142:54d1543e23e5 | 1251 | ppp.hdlc.frameStartIndex = ppp.rx.tail; // remember where next frame started |
| nixnax | 142:54d1543e23e5 | 1252 | break; |
| nixnax | 142:54d1543e23e5 | 1253 | } |
| nixnax | 142:54d1543e23e5 | 1254 | } |
| nixnax | 142:54d1543e23e5 | 1255 | } |
| nixnax | 142:54d1543e23e5 | 1256 | } |
| nixnax | 142:54d1543e23e5 | 1257 | } |
| nixnax | 142:54d1543e23e5 | 1258 | |
| nixnax | 142:54d1543e23e5 | 1259 | /// scan for a connect string ("CLIENT") from the host PC, if found, we set ppp.oline to true, which will the IP packet scanner |
| nixnax | 142:54d1543e23e5 | 1260 | void scanForConnectString() |
| nixnax | 142:54d1543e23e5 | 1261 | { |
| nixnax | 142:54d1543e23e5 | 1262 | while(ppp.online == 0) { |
| nixnax | 142:54d1543e23e5 | 1263 | checkPc(); // gather received characters |
| nixnax | 142:54d1543e23e5 | 1264 | // search for Windows Dialup Networking "Direct Connection Between Two Computers" expected connect string |
| nixnax | 142:54d1543e23e5 | 1265 | char * found1 = strstr( (char *)ppp.rx.buf, "CLIENT" ); |
| nixnax | 142:54d1543e23e5 | 1266 | if (found1 != NULL) { |
| nixnax | 142:54d1543e23e5 | 1267 | // respond with Windows Dialup networking expected "Direct Connection Between Two Computers" response string |
| nixnax | 143:c5019f856a56 | 1268 | if (v0) debugPrintf("Connected: Found connect string \"CLIENT\", sent \"CLIENTSERVER\"\n"); |
| nixnax | 142:54d1543e23e5 | 1269 | pc.puts("CLIENTSERVER"); |
| nixnax | 142:54d1543e23e5 | 1270 | ppp.online=1; // we are connected - set flag so we stop looking for the connect string |
| nixnax | 142:54d1543e23e5 | 1271 | checkPc(); |
| nixnax | 142:54d1543e23e5 | 1272 | } |
| nixnax | 142:54d1543e23e5 | 1273 | } |
| nixnax | 142:54d1543e23e5 | 1274 | } |
| nixnax | 142:54d1543e23e5 | 1275 | |
| nixnax | 144:01d98cf7738e | 1276 | /// Initialize PPP data structure and set serial port(s) baud rate(s) |
| nixnax | 144:01d98cf7738e | 1277 | void initializePpp() |
| nixnax | 142:54d1543e23e5 | 1278 | { |
| nixnax | 142:54d1543e23e5 | 1279 | pc.baud(115200); // USB serial port to pc |
| nixnax | 144:01d98cf7738e | 1280 | debugBaudRate(115200); // baud rate for (optional) debug serial port |
| nixnax | 142:54d1543e23e5 | 1281 | debugPrintf("\x1b[2J\x1b[H\x1b[30mmbed PPP-Blinky HTTP & WebSocket server ready :)\n"); // VT100 codes for clear_screen, home, black_text - Tera Term is a handy VT100 terminal |
| nixnax | 142:54d1543e23e5 | 1282 | pppInitStruct(); // initialize all the PPP properties |
| nixnax | 143:c5019f856a56 | 1283 | } |
 Nicolas Nackel
Nicolas Nackel